How Gigamon Inline Ssl Decryption Works
Example Inline Tls Ssl Decryption The vÜe community is a technical site where gigamon users, partners, security and network professionals and gigamon employees come together to share knowledge and expertise, ask questions, build their network and learn about best practices for gigamon products. Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on .

Gigavue Modules For Inline Ssl Decryption This 1 day course focuses on building inline ssl tls decryption solutions. training is conducted through comprehensive discussions, real world use cases, and practical hands on labs. This 1 day course focuses on building inline ssl tls decryption solutions. training is conducted through comprehensive discussions, real world use cases, and practical hands on labs. This document will provide a comprehensive overview of inline tls ssl decryption using gigasmart, including its configuration, validation of the solution, and best practices. Upon completing this gigamon designing and implementing inline ssl tls solutions (ssl solutions) course, learners will be able to meet these objectives: learn how gigamon manages traffic flows where decryption of traffic is essential.

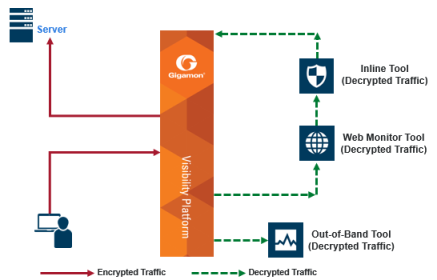
Unlock The Power Of Gigamon Ssl Decryption Comprehensive Datasheet This document will provide a comprehensive overview of inline tls ssl decryption using gigasmart, including its configuration, validation of the solution, and best practices. Upon completing this gigamon designing and implementing inline ssl tls solutions (ssl solutions) course, learners will be able to meet these objectives: learn how gigamon manages traffic flows where decryption of traffic is essential. Flex inline and decryption using flexible inline maps, you can identify specific flows of traffic using layer 2 to layer 4 rules, then designate the tools that will inspect the traffic, and specify the order of traffic to the tools. Identify hidden threats in both inbound and outbound encrypted trafic with the gigamon visibility fabric and gigasmart. decrypt once and share across all tools, scaling and increasing the eficacy of each by eliminating the processor overhead. This chapter describes the configuration procedures for the gigavue hc2 and fortigate ngfw as an inline tool group solution through gigamon’s gigavue fm. the procedures are organized as follows:. This process makes it possible to decrypt, perform a detailed inspection, and then re encrypt ssl traffic before sending it off to its destination. this helps ensure that only authorized ssl traffic is entering the network, and that malware hidden in ssl tls sessions is exposed and dealt with.

Unlock The Power Of Gigamon Ssl Decryption Comprehensive Datasheet Flex inline and decryption using flexible inline maps, you can identify specific flows of traffic using layer 2 to layer 4 rules, then designate the tools that will inspect the traffic, and specify the order of traffic to the tools. Identify hidden threats in both inbound and outbound encrypted trafic with the gigamon visibility fabric and gigasmart. decrypt once and share across all tools, scaling and increasing the eficacy of each by eliminating the processor overhead. This chapter describes the configuration procedures for the gigavue hc2 and fortigate ngfw as an inline tool group solution through gigamon’s gigavue fm. the procedures are organized as follows:. This process makes it possible to decrypt, perform a detailed inspection, and then re encrypt ssl traffic before sending it off to its destination. this helps ensure that only authorized ssl traffic is entering the network, and that malware hidden in ssl tls sessions is exposed and dealt with.
Comments are closed.