How Does Mega S Zero Knowledge Encryption Work Mega Help Centre

Mega How Does Mega S Zero Knowledge Encryption Work Mega’s zero knowledge encryption relies on your password to unlock all of your account’s encrypted data. essentially, your password is a cryptographic key: if your password is weak (too short, guessable, or reused on other sites), your account is vulnerable. How can we help you today? welcome to the mega help centre. search our extensive documentation and self help resources.

Mega Help Pdf We use zero knowledge encryption, also known as user controlled end to end encryption, to protect your data online, even when sharing. this means that only you and those you share information with have the keys to see, read, or listen to that data on mega. The client machines are responsible for generating, exchanging and managing the encryption keys. mega's encryption model does not require any usable symmetric or private keys to ever leave the end user's computer. In 2013, mega pioneered user controlled end to end encryption through the web browser. today, it provides the same zero knowledge privacy and security for its cloud storage and chat applications, whether through a web browser, mobile app, desktop app or command line tool. Mega encrypts your data with a master key that is randomly generated on the device you use to create your account. the master key is encrypted with a hash of your password and saved on mega's servers for the next time you login.

Mega 2 Pdf Computer Hardware Computing In 2013, mega pioneered user controlled end to end encryption through the web browser. today, it provides the same zero knowledge privacy and security for its cloud storage and chat applications, whether through a web browser, mobile app, desktop app or command line tool. Mega encrypts your data with a master key that is randomly generated on the device you use to create your account. the master key is encrypted with a hash of your password and saved on mega's servers for the next time you login. Mega provides end to end encryption of your data, using keys that only you know. they use aes 128 encryption to protect the data when at rest, and double down by adding a layer of tls encryption when your data is in transit. Zero knowledge encryption is a method of encryption, rather than an encryption protocol such as aes 256. the term most often describes an encryption process where your data is secured at all times, with only you having the key or password needed to access and decrypt it. So there are a few cloud storage services such as mega.nz, syn and others which state that they use zero knowledge encryption. this would mean that they don't have access to the private keys which are required to decrypt and view the content stored by a user on their cloud storage. Standard 256 bit encryption is strong, but the gold standard is zero knowledge encryption. with this technology, you (and only you) hold the keys to your data. not even the cloud storage.
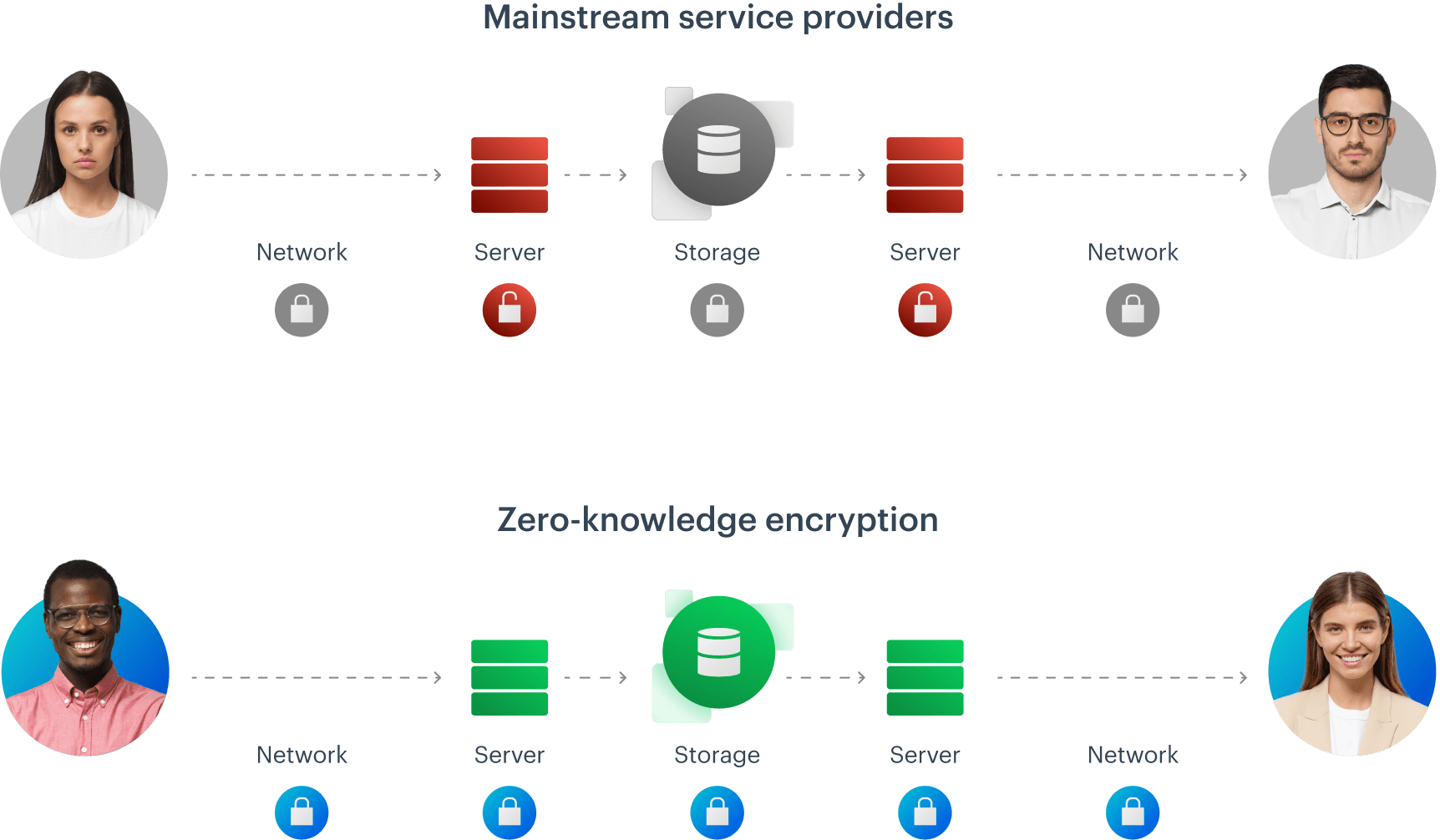
Zero Knowledge Encryption Tresorit Features Mega provides end to end encryption of your data, using keys that only you know. they use aes 128 encryption to protect the data when at rest, and double down by adding a layer of tls encryption when your data is in transit. Zero knowledge encryption is a method of encryption, rather than an encryption protocol such as aes 256. the term most often describes an encryption process where your data is secured at all times, with only you having the key or password needed to access and decrypt it. So there are a few cloud storage services such as mega.nz, syn and others which state that they use zero knowledge encryption. this would mean that they don't have access to the private keys which are required to decrypt and view the content stored by a user on their cloud storage. Standard 256 bit encryption is strong, but the gold standard is zero knowledge encryption. with this technology, you (and only you) hold the keys to your data. not even the cloud storage.
Comments are closed.