How Does A Zero Trust Security Architecture Work
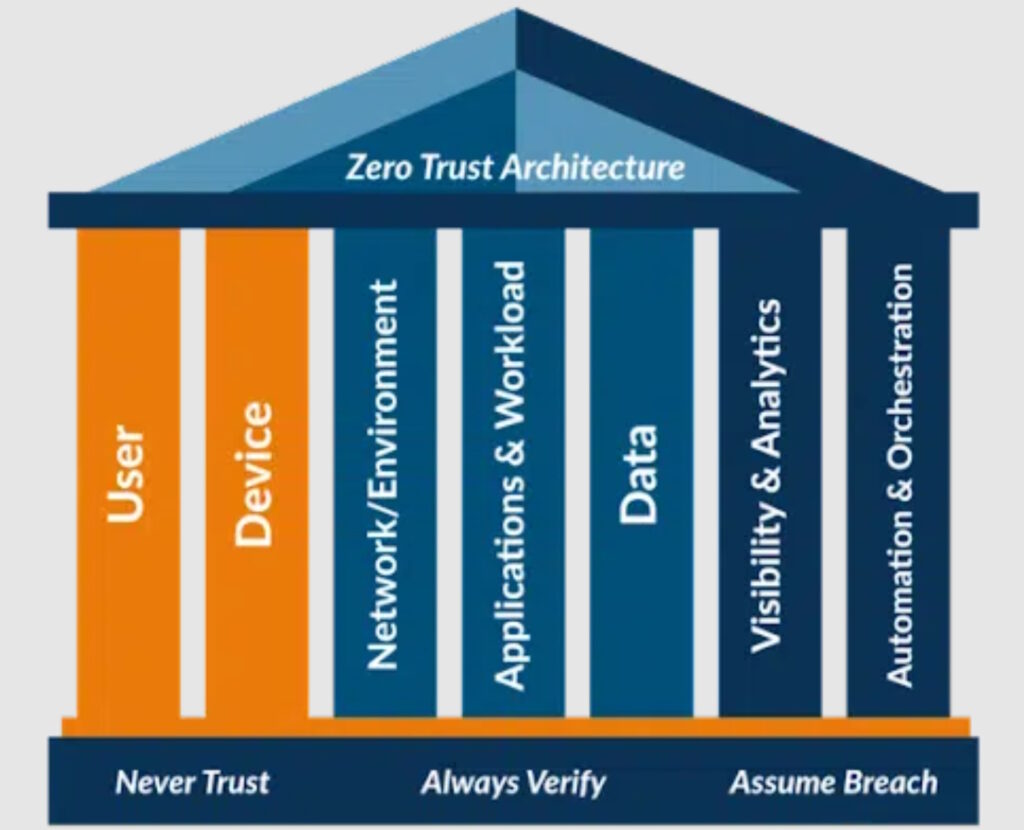
How Does A Zero Trust Security Architecture Work Achieving zero trust security requires a combination of two key elements: zero trust network access (ztna), which delivers zero trust from the outside, and microsegmentation, which achieves zero trust from the inside – for example, between machines within your network. Zero trust architecture outlines how these principles are applied across an enterprise's systems, networks, and workflows to ensure that no entity (user, device, or application) gains access without thorough validation.

What Is Zero Trust Architecture Zero Trust Security Model This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization. Explore our guide to zero trust architecture: understand what zta is, how it operates, and discover its key principles, benefits, and potential drawbacks. Learn what zero trust security architecture is, why it matters now, and how to implement it with practical steps, diagrams, and real world guidance. In this article, we’ll break down nist 800 207 to show what a zero trust architecture really is, how it works, and why it’s not a product but a security philosophy.
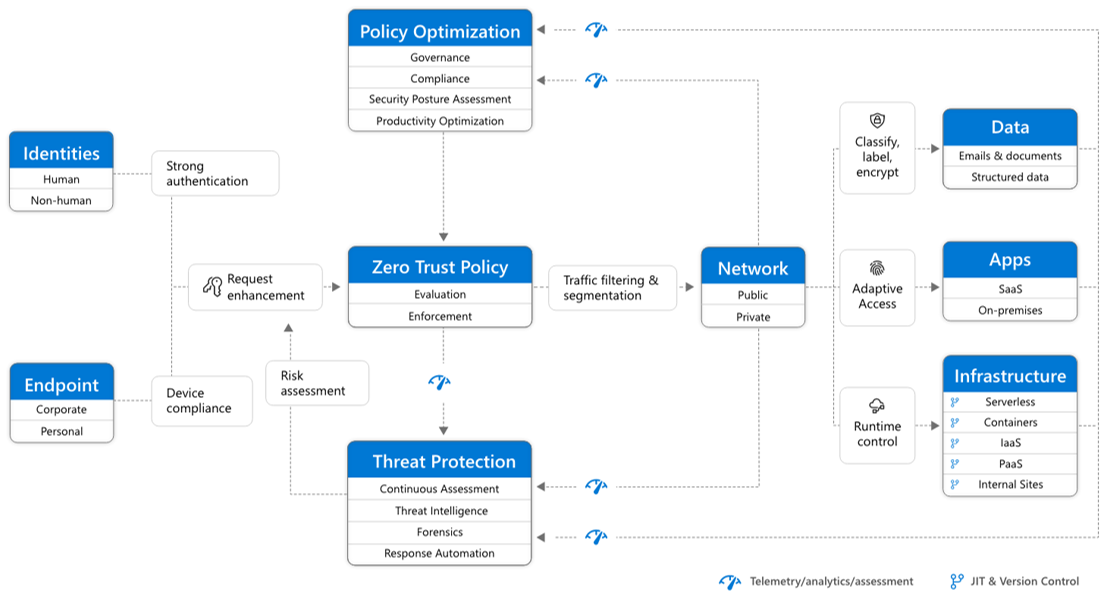
What Is Zero Trust Architecture Zero Trust Security Model Zero Trust Learn what zero trust security architecture is, why it matters now, and how to implement it with practical steps, diagrams, and real world guidance. In this article, we’ll break down nist 800 207 to show what a zero trust architecture really is, how it works, and why it’s not a product but a security philosophy. What it is: zero trust architecture (zta) is a cybersecurity framework built on the principle of “never trust, always verify.” it assumes every user, device, and application is untrusted until verified, enforcing strict identity, access, and policy controls. Zero trust is a robust security model that works on the principle of “never trust, always verify” to ensure secure connections. understanding what is zero trust and implementing it can help organizations safeguard their crucial applications, devices, data, and resources. What is zero trust? the zero trust security model uses identity and context information to continually verify trust before granting least privilege access for users, devices, apps, networks, and clouds. Explore the essential guide to zero trust architecture principles, benefits, implementation steps, and industry use cases to secure your enterprise in 2025.
What Does Zero Trust Security Architecture Mean What it is: zero trust architecture (zta) is a cybersecurity framework built on the principle of “never trust, always verify.” it assumes every user, device, and application is untrusted until verified, enforcing strict identity, access, and policy controls. Zero trust is a robust security model that works on the principle of “never trust, always verify” to ensure secure connections. understanding what is zero trust and implementing it can help organizations safeguard their crucial applications, devices, data, and resources. What is zero trust? the zero trust security model uses identity and context information to continually verify trust before granting least privilege access for users, devices, apps, networks, and clouds. Explore the essential guide to zero trust architecture principles, benefits, implementation steps, and industry use cases to secure your enterprise in 2025.

What Is Zero Trust Architecture Zero Trust Security Model Zero Trust What is zero trust? the zero trust security model uses identity and context information to continually verify trust before granting least privilege access for users, devices, apps, networks, and clouds. Explore the essential guide to zero trust architecture principles, benefits, implementation steps, and industry use cases to secure your enterprise in 2025.
Comments are closed.