How Do You Perform Cloud Security Forensic Analysis
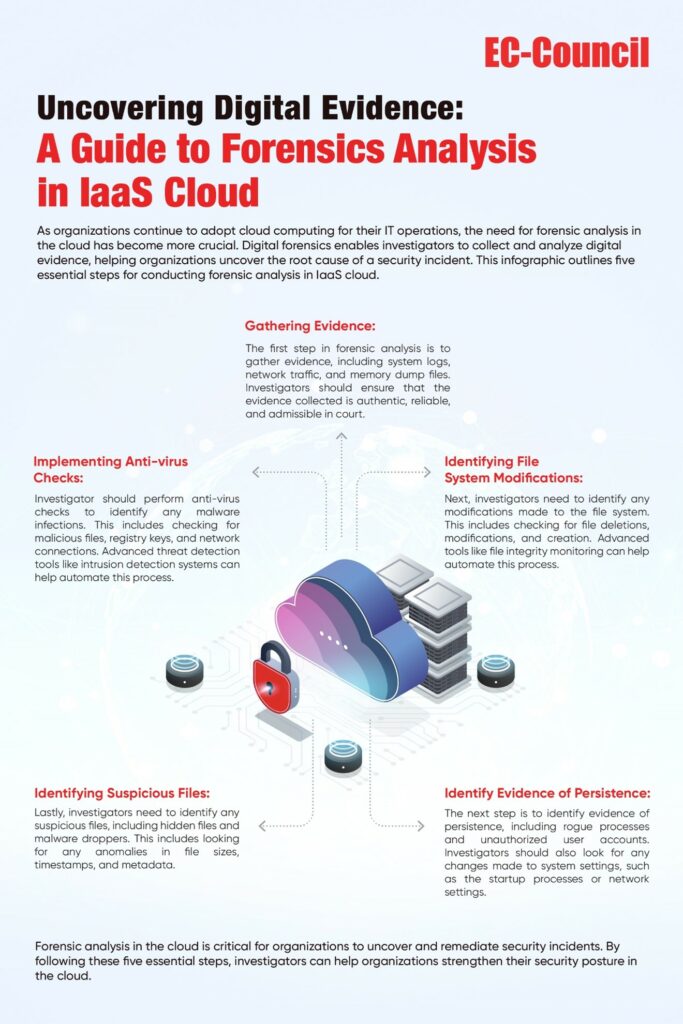
A Guide To Cloud Forensics In Iaas Overcoming Challenges And Cloud forensics is the process of applying digital forensic methods to cloud environments. it involves identifying, acquiring, analyzing, and preserving digital evidence from cloud systems to investigate incidents, detect threats, and support compliance. From data collection methods across various cloud service models to incident response planning and the use of specialized forensic tools, this guide offers a comprehensive overview to equip you with the knowledge and skills to navigate the cloud security landscape effectively.

Cybersecurity Forensic Analysis Security Forensic Analysis In this edition, google staff security engineer aaron peterson shares an inside look at google’s approach to cloud forensics, and offers top tips for hunting down evidence in the cloud. The cloud forensic process flow is designed to help investigators collect, preserve, and analyze data in a cloud computing environment. by following this process, investigators can more effectively determine what happened and who was responsible for an incident. This section provides comprehensive guidance on leveraging cloudtrail for security incident response and forensic analysis. you'll learn how to understand critical event fields, implement best practices for security monitoring, and access curated resources to strengthen your security posture. Once you have your environment and aws account structure set up for forensics, you’ll want to define the technologies required to effectively perform forensically sound methodologies across the four phases:.
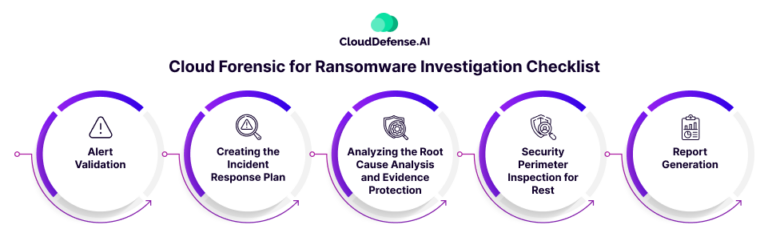
Cloud Forensics And Data Visualization For Ransomware Attack This section provides comprehensive guidance on leveraging cloudtrail for security incident response and forensic analysis. you'll learn how to understand critical event fields, implement best practices for security monitoring, and access curated resources to strengthen your security posture. Once you have your environment and aws account structure set up for forensics, you’ll want to define the technologies required to effectively perform forensically sound methodologies across the four phases:. To conduct cloud computing forensics investigations, analysts need evidence. explore techniques and tools used for evidence acquisition and analysis. Due to organizations' growing dependence on cloud platforms, cloud forensics is quickly becoming a vital pillar of cybersecurity. in this post, we’ll review cloud forensic investigations' objectives, challenges, and processes in detail. As more organizations migrate to the cloud, the need for effective cloud forensics becomes increasingly critical. here’s an overview of essential elements for conducting thorough cloud based. In this article, we take a look at what a cloud forensic analysis should achieve, consider the various types of forensics that are implemented during the process, and discuss the benefits in relation to cloud security management.
Cloud Forensics Tool Owade Pulls Online Services Data Hacker 10 To conduct cloud computing forensics investigations, analysts need evidence. explore techniques and tools used for evidence acquisition and analysis. Due to organizations' growing dependence on cloud platforms, cloud forensics is quickly becoming a vital pillar of cybersecurity. in this post, we’ll review cloud forensic investigations' objectives, challenges, and processes in detail. As more organizations migrate to the cloud, the need for effective cloud forensics becomes increasingly critical. here’s an overview of essential elements for conducting thorough cloud based. In this article, we take a look at what a cloud forensic analysis should achieve, consider the various types of forensics that are implemented during the process, and discuss the benefits in relation to cloud security management.
Comments are closed.