How Do You Implement A Vulnerability Management Program Next Lvl Programming

How To Implement Vulnerability Management Training Program Learn what vulnerability management is, what steps are involved in the process, and how you can implement a robust vulnerability management program that leverages automation. It will walk you through the steps of building a vulnerability management program. we will define the program, explain why it is important to have a program, pitfalls to avoid, and opportunities to implement and automate features of the program.

4 Steps To A Winning Vulnerability Management Program 2 Coding With A successful vulnerability management program isn't built overnight, but the steps outlined here provide a practical framework that addresses the real world challenges organizations face. Learn what is a vulnerability management plan and how to create it, measure key kpis, and strengthen security posture for lasting organizational protection. Vulnerability management program: complete guide to cloud security with best practices, implementation strategies, metrics, and executive reporting for 2025. Learn how to set up a vulnerability management program to help your team speed up remediation workflows and focus on high risk vulnerabilities.
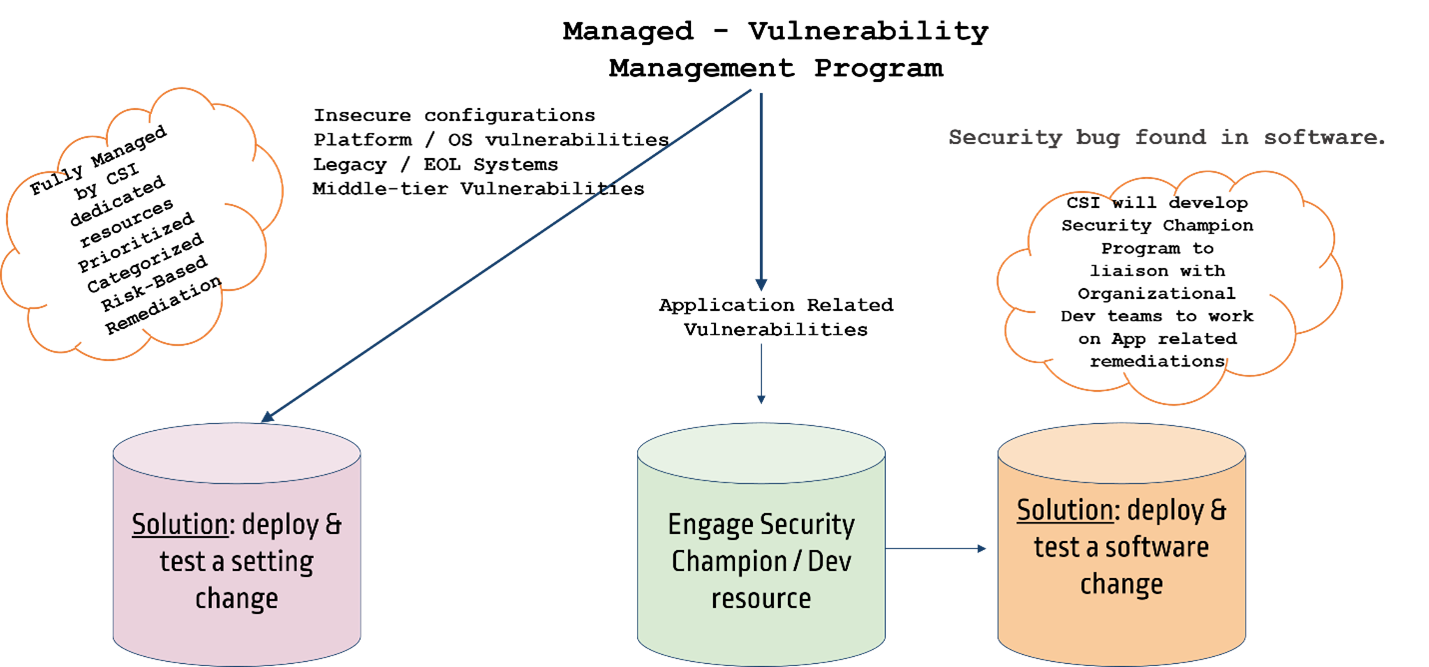
Managed Vulnerability Management Program Cybersecurityinc Vulnerability management program: complete guide to cloud security with best practices, implementation strategies, metrics, and executive reporting for 2025. Learn how to set up a vulnerability management program to help your team speed up remediation workflows and focus on high risk vulnerabilities. How do you implement a vulnerability management program? in this informative video, we’ll guide you through the essential steps to implement a vulnerability. Discover how a vulnerability management program can enhance your cloud security, plus how contextual assessments can turn your security from passive to active. In this article, we’ll break down the vulnerability management lifecycle, its key steps, how it relates to broken access control, and how you can begin to implement and automate vulnerability management at your organization. Build an audit ready, compliant vulnerability management program with structured processes, risk based prioritization, and effective remediation workflows.

Vulnerability Management Programs Codingwithcookie How do you implement a vulnerability management program? in this informative video, we’ll guide you through the essential steps to implement a vulnerability. Discover how a vulnerability management program can enhance your cloud security, plus how contextual assessments can turn your security from passive to active. In this article, we’ll break down the vulnerability management lifecycle, its key steps, how it relates to broken access control, and how you can begin to implement and automate vulnerability management at your organization. Build an audit ready, compliant vulnerability management program with structured processes, risk based prioritization, and effective remediation workflows.
Comments are closed.