How Do Quantum Computers Work Quantum Cryptography Presentation
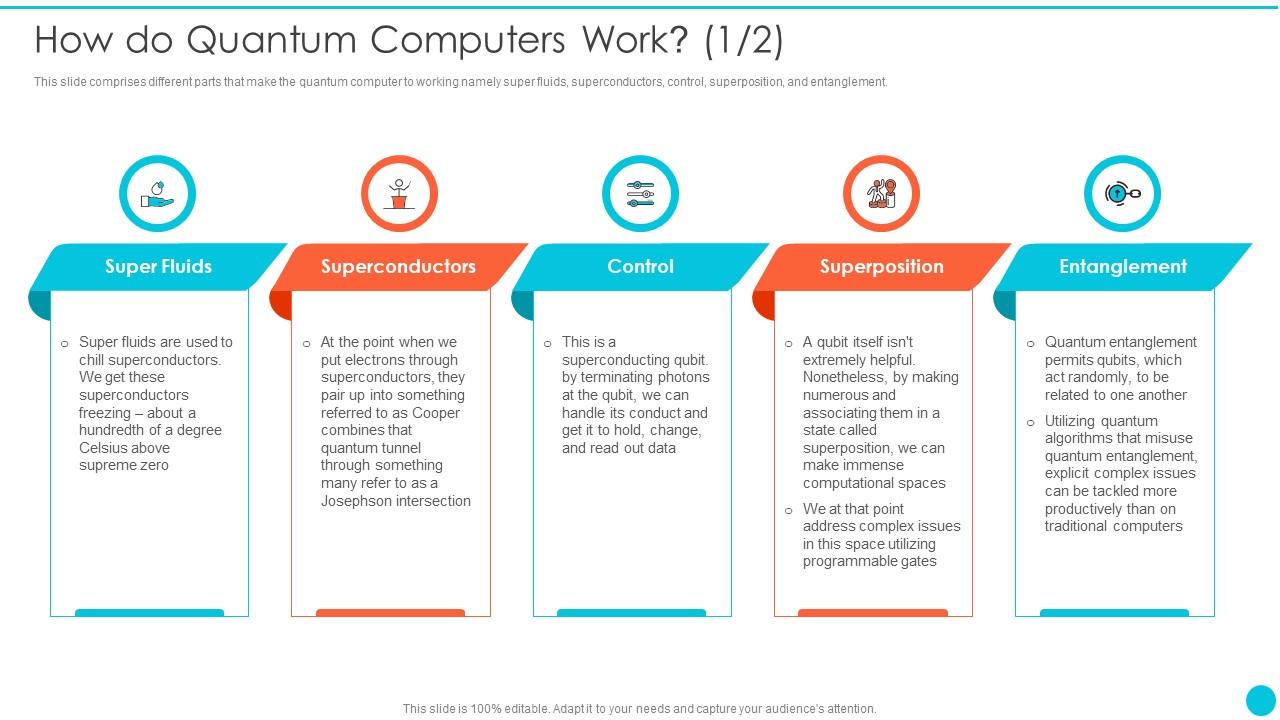
How Do Quantum Computers Work Quantum Cryptography Presentation This document discusses quantum cryptography. it begins with an introduction to traditional cryptography and then defines quantum cryptography as exploiting quantum mechanical properties like the heisenberg uncertainty principle and quantum entanglement for cryptographic tasks. Use our how do quantum computers work quantum cryptography to effectively help you save your valuable time. they are readymade to fit into any presentation structure.
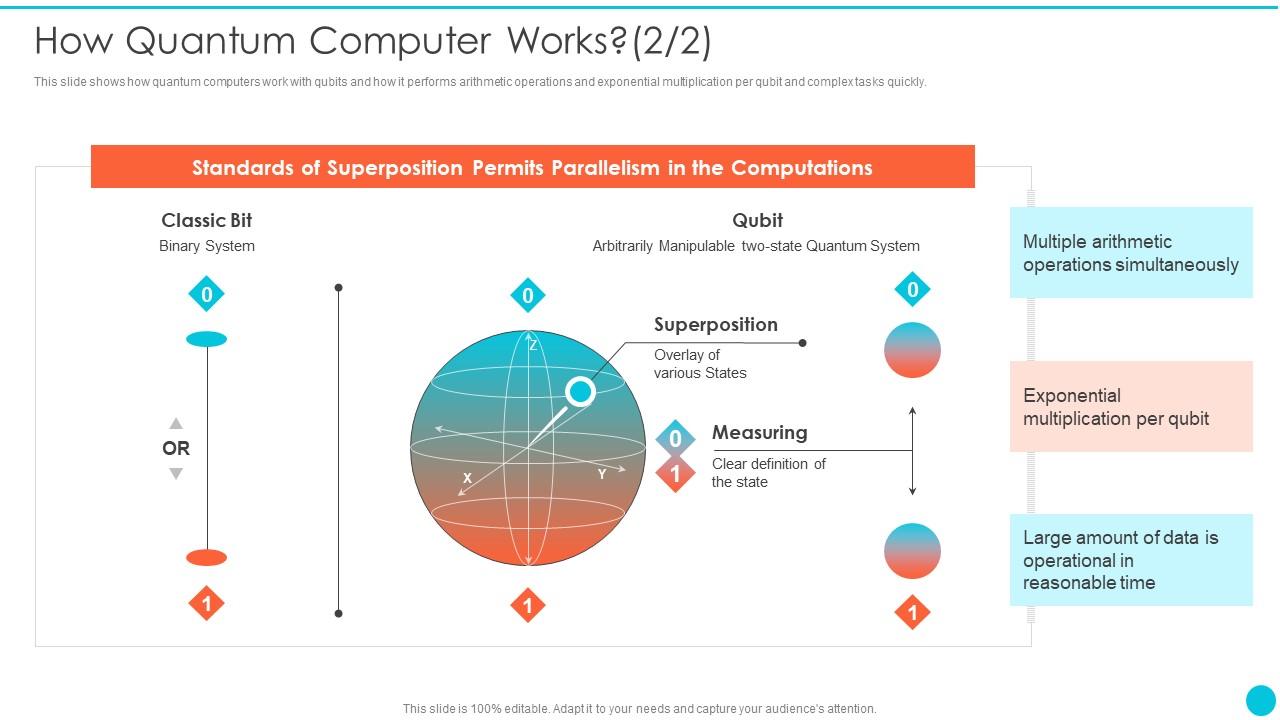
How Do Quantum Computers Work Quantum Cryptography Presentation Quantum cryptography is the single most successful application of quantum computing information theory. for the first time in history, we can hope to use the forces of nature to implement perfectly secure cryptosystems. Quantum cryptography (eecs 598 presentation) (eecs 598 presentation) by. amit marathe. Chapter 15: quantum cryptography unconditionally secure basic quantum cryptographic protocols, such as bit commitment and oblivious transfer, are impossible. – id: 43ef5f zmy2o. These results signify an important transition from noisy intermediate scale quantum computing to reliable quantum computing, and demonstrate advanced capabilities toward large scale fault tolerant quantum computing.
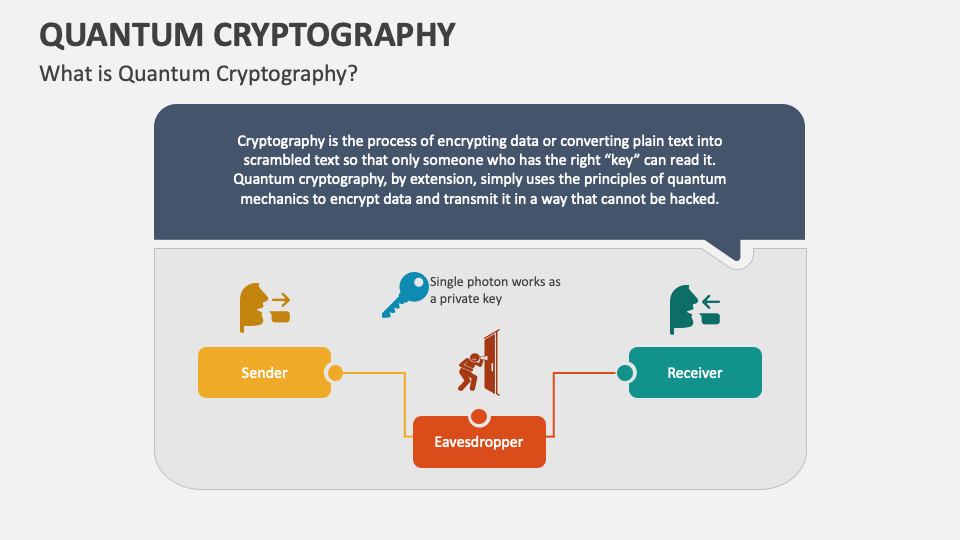
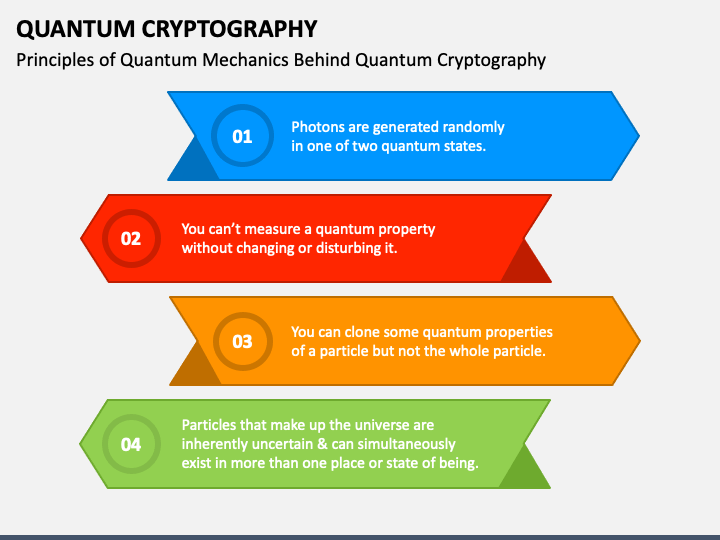
Quantum Cryptography Powerpoint And Google Slides Template Ppt Slides Chapter 15: quantum cryptography unconditionally secure basic quantum cryptographic protocols, such as bit commitment and oblivious transfer, are impossible. – id: 43ef5f zmy2o. These results signify an important transition from noisy intermediate scale quantum computing to reliable quantum computing, and demonstrate advanced capabilities toward large scale fault tolerant quantum computing. Using quantum mechanics in crypto protocols. what is quantum mechanics? classical world. everything is in a well defined state. you can observe the state of a system. quantum world. things can be in “superposition” of several classical states. observation make the system jump into one possibility. An important new feature of quantum cryptography is that security of cryptographic protocols generation is based on the laws of nature and not on the unproven assumptions of computational complexity theory. An introduction to quantum computers and quantum cryptography computer network security prepared by: nima bayan, p.eng. fall 2003 contents ! introduction " cryptography and relativity " quantum algorithms " quantum computers !. Quantum cryptography provides unconditionally secure key distribution by exploiting properties of quantum mechanics, such as photon polarization. it solves the key distribution problem by allowing two parties to generate a shared random key known only to them to encrypt subsequent communications.
Why Do We Need Quantum Computers Quantum Cryptography Presentation Using quantum mechanics in crypto protocols. what is quantum mechanics? classical world. everything is in a well defined state. you can observe the state of a system. quantum world. things can be in “superposition” of several classical states. observation make the system jump into one possibility. An important new feature of quantum cryptography is that security of cryptographic protocols generation is based on the laws of nature and not on the unproven assumptions of computational complexity theory. An introduction to quantum computers and quantum cryptography computer network security prepared by: nima bayan, p.eng. fall 2003 contents ! introduction " cryptography and relativity " quantum algorithms " quantum computers !. Quantum cryptography provides unconditionally secure key distribution by exploiting properties of quantum mechanics, such as photon polarization. it solves the key distribution problem by allowing two parties to generate a shared random key known only to them to encrypt subsequent communications.
Quantum Cryptography Powerpoint And Google Slides Template Ppt Slides An introduction to quantum computers and quantum cryptography computer network security prepared by: nima bayan, p.eng. fall 2003 contents ! introduction " cryptography and relativity " quantum algorithms " quantum computers !. Quantum cryptography provides unconditionally secure key distribution by exploiting properties of quantum mechanics, such as photon polarization. it solves the key distribution problem by allowing two parties to generate a shared random key known only to them to encrypt subsequent communications.
Comments are closed.