How Do Phishing Attacks Work
Phishing Attacks Hanley S Consulting Services Phishing is a method of online identity theft involving fake messages that mimic reputable sources like banks or online retailers. phishers plan, set up and execute attacks to steal personal and financial data, often using deceptive tactics like spoofed email addresses and obfuscated links. Phishing is a social engineering attack designed to trick individuals into revealing sensitive information or performing actions that compromise security. the term originates from the analogy of “fishing,” where attackers “bait” victims with a deceptive lure in hopes that someone will “bite.”.

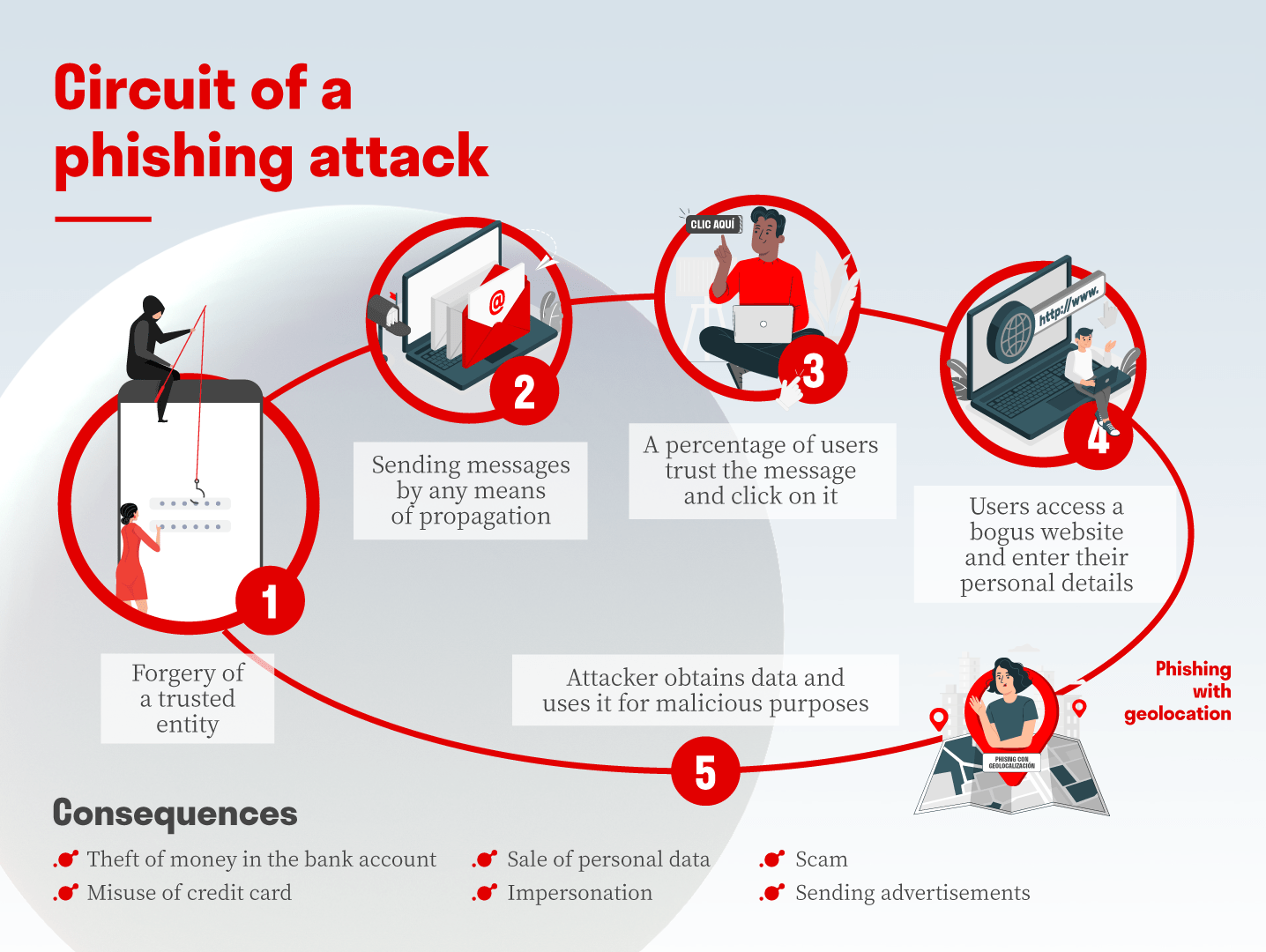
How Do Phishing Attacks Work Netsweeper It's not about complex code or breaking through firewalls; it's about playing on human emotions and trust. so, how do these sneaky attacks actually unfold? let's break it down, step by step. How does phishing work? phishing is a type of social engineering and cybersecurity attack where the attacker impersonates someone else via email or other electronic communication methods, including social networks and short message service (sms) text messages, to reveal sensitive information. Phishing is a cyberattack where attackers use fake messages or websites to trick victims into giving away sensitive information. it works like “fishing,” using bait to lure targets into clicking harmful links or entering confidential data. Phishing is a type of cyberattack where threat actors masquerade as legitimate companies or individuals to steal sensitive information such as usernames, passwords, credit card numbers, and other personal details.
.png#keepProtocol)
Phishing Attacks The Anatomy Of A Threat Phishing is a cyberattack where attackers use fake messages or websites to trick victims into giving away sensitive information. it works like “fishing,” using bait to lure targets into clicking harmful links or entering confidential data. Phishing is a type of cyberattack where threat actors masquerade as legitimate companies or individuals to steal sensitive information such as usernames, passwords, credit card numbers, and other personal details. Attackers use spoofed login pages and real time relay tools to capture both credentials and one time passcodes. in some cases, phishing kits are designed to bypass two factor authentication by immediately forwarding stolen credentials to the attacker's server, enabling instant access. Learn what is phishing attack and how does it work. read on to know the different types of phishing and how to prevent from such attack. If a phishing attack is successful, it means that malicious third parties managed to gather private data. the stolen information is then used to commit financial theft or identity theft. The basic element of a phishing attack is a message sent by email, social media, or other electronic communication means. a phisher may use public resources, especially social networks, to collect background information about the personal and work experience of their victim.

How Does A Phishing Attack Work Phishing Attacks And Strategies Ppt Slide Attackers use spoofed login pages and real time relay tools to capture both credentials and one time passcodes. in some cases, phishing kits are designed to bypass two factor authentication by immediately forwarding stolen credentials to the attacker's server, enabling instant access. Learn what is phishing attack and how does it work. read on to know the different types of phishing and how to prevent from such attack. If a phishing attack is successful, it means that malicious third parties managed to gather private data. the stolen information is then used to commit financial theft or identity theft. The basic element of a phishing attack is a message sent by email, social media, or other electronic communication means. a phisher may use public resources, especially social networks, to collect background information about the personal and work experience of their victim.
Comments are closed.