How Do Mac Spoofing Attacks Work

How Do Mac Spoofing Attacks Work In mac spoofing attacks, hackers change a device's mac address to imitate a different device present on the network using techniques like cloning and randomizing a mac address. This comprehensive blog breaks down what mac spoofing is, how it works, why it’s used, and how to protect against it —including real world examples and the latest mitigation techniques in 2026.
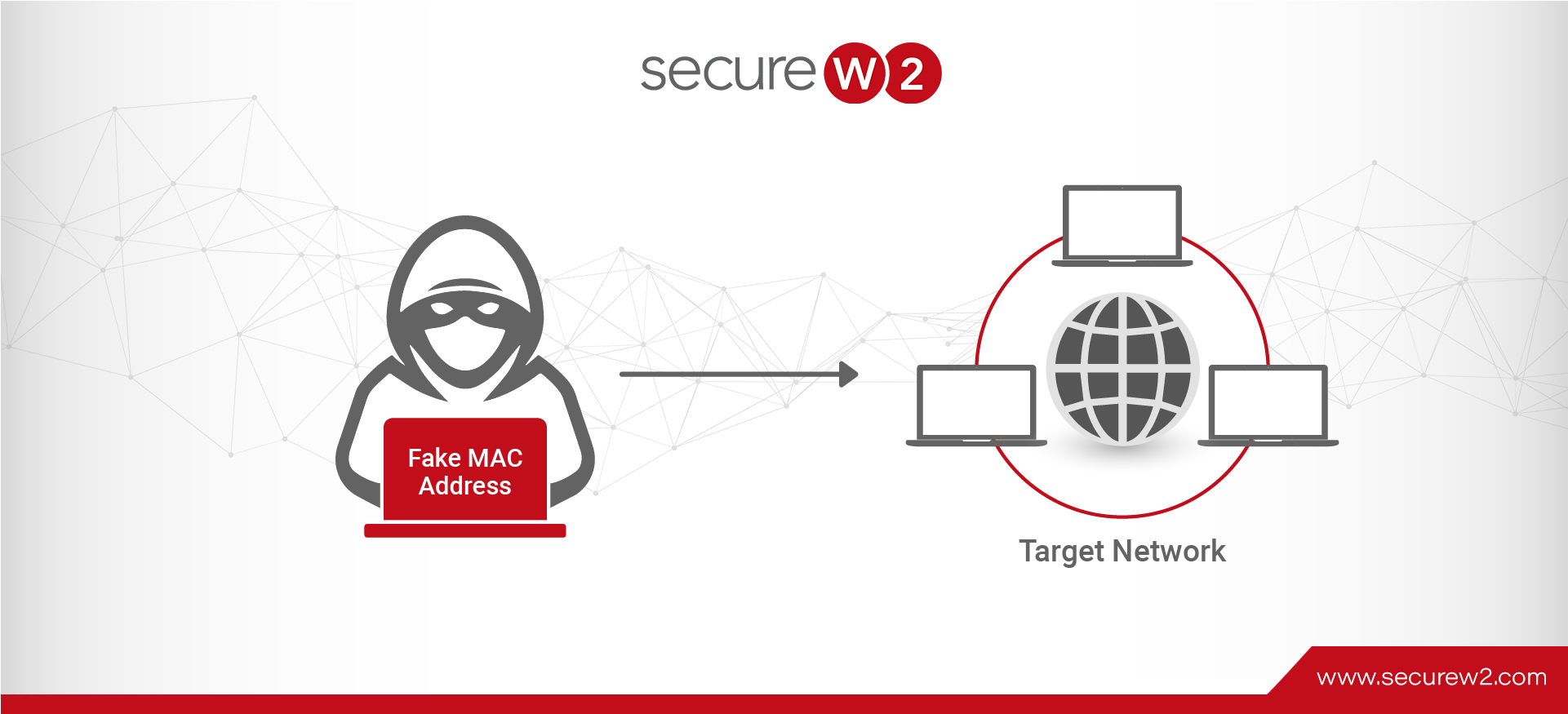
Mac Spoofing Attacks Explained A Technical Overview How does a mac spoofing attack work? in a mac spoofing attack, the hacker changes their device’s mac address to match a legitimate device’s address, connects to the network, and intercepts or redirects data. A mac spoofing attack is when a hacker mimics your mac address to redirect data sent to your device to another device. it allows the attacker to gain unauthorized access to a network to launch a man in the middle attack. In this tutorial, we looked over how a switched lan network works, and we saw how a mac flooding and a mac spoofing attack works. we discussed what the attacker could achieve and how network administrators can mitigate these attacks. Mac spoofing is a technique for changing a factory assigned media access control (mac) address of a network interface on a networked device. the mac address that is hard coded on a network interface controller (nic) cannot be changed. however, many drivers allow the mac address to be changed.
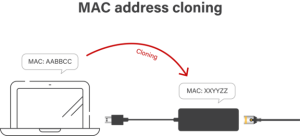
Mac Spoofing Attacks Explained A Technical Overview In this tutorial, we looked over how a switched lan network works, and we saw how a mac flooding and a mac spoofing attack works. we discussed what the attacker could achieve and how network administrators can mitigate these attacks. Mac spoofing is a technique for changing a factory assigned media access control (mac) address of a network interface on a networked device. the mac address that is hard coded on a network interface controller (nic) cannot be changed. however, many drivers allow the mac address to be changed. A mac spoofing attack is when a hacker changes the mac address of their device to match the mac address of another on a network in order to gain unauthorized access or launch a man in the middle attack. Learn what mac spoofing is, how attackers fake device identities, risks to networks, detection methods, and best ways to prevent mac address spoofing. Conclusion: mac spoofing is a technique that can be used to fool the operating system into believing it has received an arp request from another machine. this allows the attacker to gain access to a victim's network without being detected. Explore the intricacies of mac spoofing, from basics to prevention. learn how it works, its risks, real world examples, and protection strategies.
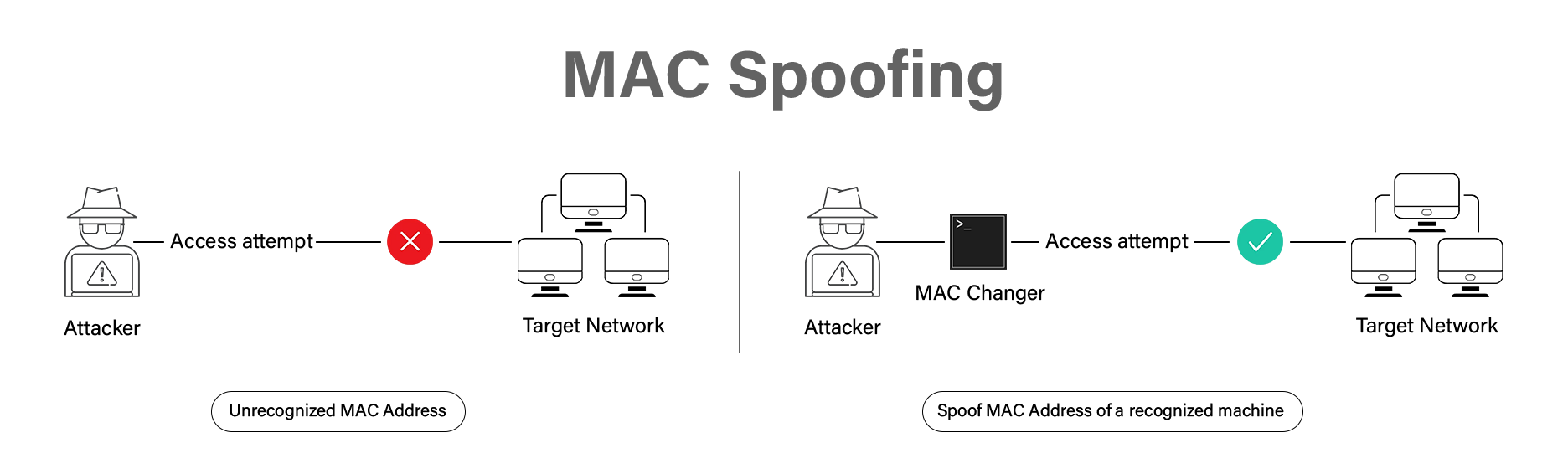
Mac Spoofing Attacks Explained A Technical Overview A mac spoofing attack is when a hacker changes the mac address of their device to match the mac address of another on a network in order to gain unauthorized access or launch a man in the middle attack. Learn what mac spoofing is, how attackers fake device identities, risks to networks, detection methods, and best ways to prevent mac address spoofing. Conclusion: mac spoofing is a technique that can be used to fool the operating system into believing it has received an arp request from another machine. this allows the attacker to gain access to a victim's network without being detected. Explore the intricacies of mac spoofing, from basics to prevention. learn how it works, its risks, real world examples, and protection strategies.
How Do I Find My Mac Address On Any Device Easily Conclusion: mac spoofing is a technique that can be used to fool the operating system into believing it has received an arp request from another machine. this allows the attacker to gain access to a victim's network without being detected. Explore the intricacies of mac spoofing, from basics to prevention. learn how it works, its risks, real world examples, and protection strategies.

How To Update Mac Operating System Easily
Comments are closed.