How Do Hackers Really Exploit Systems

3 Ways Hackers Can Exploit Your Encrypted Tunnels While some hackers use their skills for good, others exploit systems for money, revenge, or attention. understanding the different types of hackers and the common techniques they use—like viruses, phishing, and ransomware—can help you stay alert and take simple steps to protect your data. Learn how hackers exploit software vulnerabilities, weak configurations, and exposed systems, plus practical ways to protect your business from malware.

Companies Are Paying Hackers To Attack Their Own It Systems World Hackers can take control of other computers through various methods that exploit vulnerabilities in software, hardware, or human behavior. here’s an overview of the common techniques hackers use to gain unauthorized access and control over a target's computer: 1. phishing attacks. But real world hacking is far more nuanced—and often far more dangerous—than hollywood would have you believe. in this post, we’ll demystify how hacking actually works, the techniques hackers use, and what businesses and individuals can do to protect themselves. One of the primary threats to security is the exploitation of vulnerabilities by hackers. understanding how hackers identify, target, and exploit these weaknesses is essential for building. Understanding how hackers exploit these vulnerabilities is essential for both individuals and organisations to protect themselves effectively. this article delves into the methods hackers use, common types of vulnerabilities, and best practices to minimise risks.
5 Key Points Why Do Hackers Hack Ethical Hacking One of the primary threats to security is the exploitation of vulnerabilities by hackers. understanding how hackers identify, target, and exploit these weaknesses is essential for building. Understanding how hackers exploit these vulnerabilities is essential for both individuals and organisations to protect themselves effectively. this article delves into the methods hackers use, common types of vulnerabilities, and best practices to minimise risks. This article explains how hackers identify vulnerabilities, how they exploit them, and how organizations can protect their systems effectively. understanding system vulnerabilities. Understanding how hackers exploit vulnerabilities and how to secure your network is critical in preventing breaches and protecting your sensitive data. this article explores how hackers exploit common vulnerabilities and provides practical steps to security your network from these threats. Learn how hackers exploit operating system vulnerabilities to gain unauthorized access, execute malware, and bypass security controls. discover how vulnerabilities arise, common attack methods, and ways to protect your systems, with guidance from ethical hacking training institute, webasha technologies, and cybersecurity training institute. In this blog, we discuss five key questions you need to ask in order to decide how effective your vulnerability strategy is. but first, it’s helpful to understand how hackers target your environment and exploit the most critical vulnerabilities.

Hack Exploit The Biggest Threat For Technology Companies This article explains how hackers identify vulnerabilities, how they exploit them, and how organizations can protect their systems effectively. understanding system vulnerabilities. Understanding how hackers exploit vulnerabilities and how to secure your network is critical in preventing breaches and protecting your sensitive data. this article explores how hackers exploit common vulnerabilities and provides practical steps to security your network from these threats. Learn how hackers exploit operating system vulnerabilities to gain unauthorized access, execute malware, and bypass security controls. discover how vulnerabilities arise, common attack methods, and ways to protect your systems, with guidance from ethical hacking training institute, webasha technologies, and cybersecurity training institute. In this blog, we discuss five key questions you need to ask in order to decide how effective your vulnerability strategy is. but first, it’s helpful to understand how hackers target your environment and exploit the most critical vulnerabilities.

How Do Hackers Enter Your System Exploiting Vulnerabilities In 2023 Learn how hackers exploit operating system vulnerabilities to gain unauthorized access, execute malware, and bypass security controls. discover how vulnerabilities arise, common attack methods, and ways to protect your systems, with guidance from ethical hacking training institute, webasha technologies, and cybersecurity training institute. In this blog, we discuss five key questions you need to ask in order to decide how effective your vulnerability strategy is. but first, it’s helpful to understand how hackers target your environment and exploit the most critical vulnerabilities.

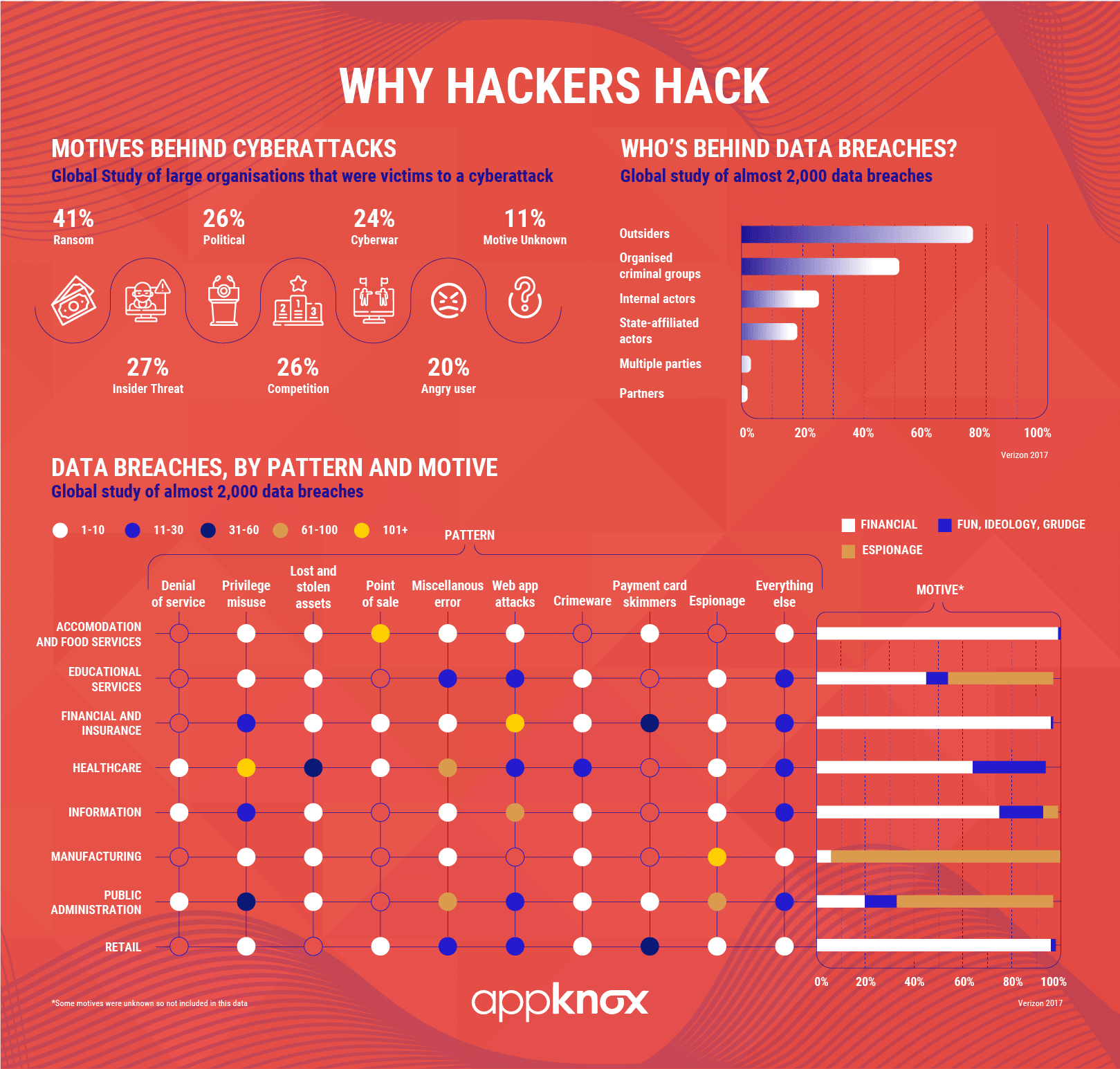
Cyber Exploitation It Purpose Of Hackers Infographics Pdf
Comments are closed.