How Do Hackers Clone Your Sim Using Personal Info

Us And Uk Accused Of Hacking Sim Card Firm To Steal Codes Bbc News Uncover the hidden world of sim cloning: learn how hackers steal your mobile identity, protect yourself from digital threats, and safeguard your personal information. Learn how hackers use sim card attacks to steal pii and compromise accounts—and how to protect against these growing cyber threats.
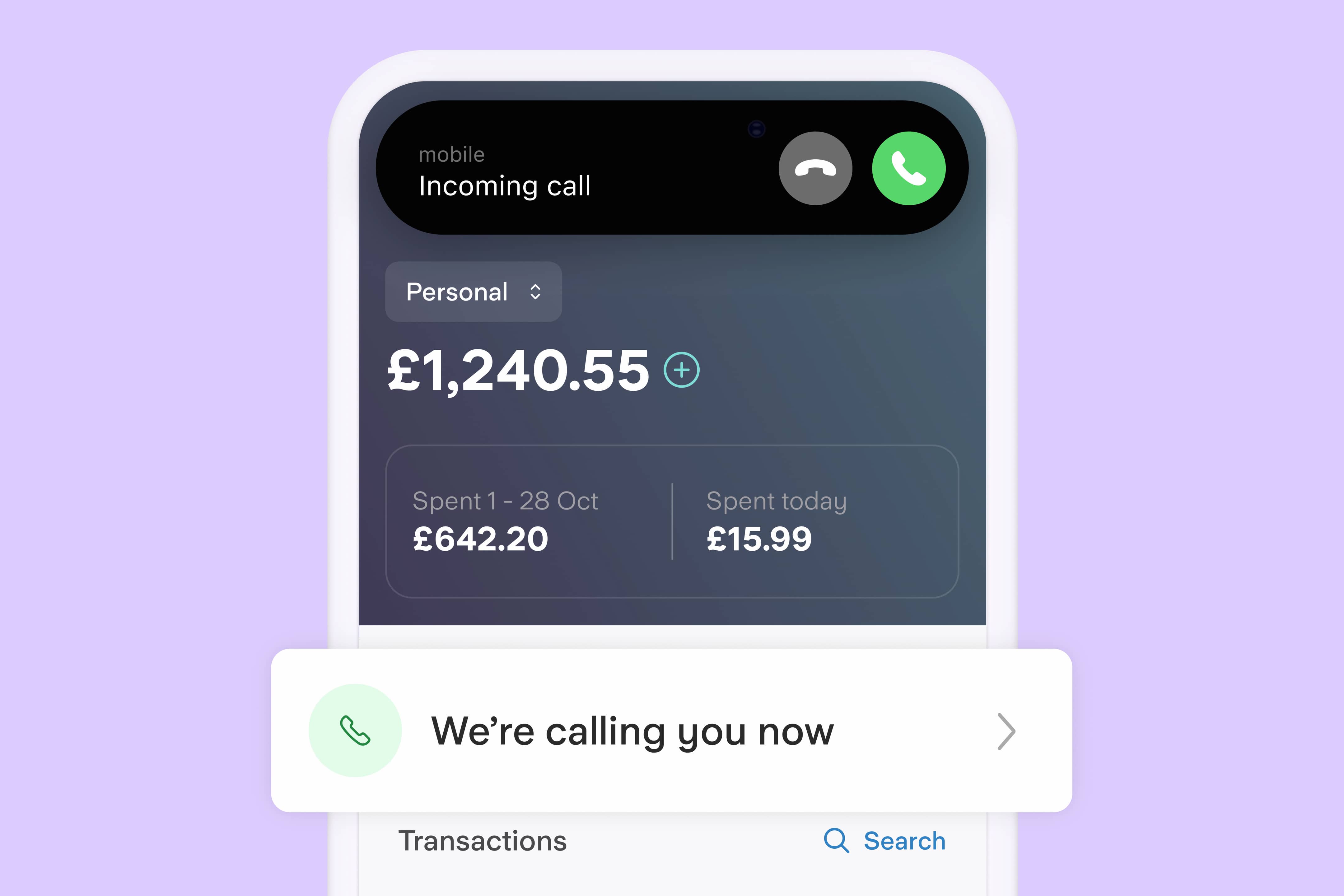
Protecting Your Sim Card From Hackers Starling Learn what sim cloning is, how attackers exploit it to intercept calls and sms, and why it remains a telecom security threat in 2025 despite stronger sim encryption. How hackers clone your sim using personal info 👉 sim cloning explained 👉 discover how hackers use your personal info to clone your sim and hijack your phone. Sim cloning is one such technique where an attacker creates a duplicate sim card to gain unauthorized access to a victim’s mobile network, calls, messages, and even banking transactions. this leads to serious financial fraud, identity theft, and data breaches. Learn what sim cloning is and how it works. discover key risks associated with this fraud and explore effective ways to detect and prevent it.

Prevent Sim Swapping Hackers From Stealing Your Phone Number And The Sim cloning is one such technique where an attacker creates a duplicate sim card to gain unauthorized access to a victim’s mobile network, calls, messages, and even banking transactions. this leads to serious financial fraud, identity theft, and data breaches. Learn what sim cloning is and how it works. discover key risks associated with this fraud and explore effective ways to detect and prevent it. Hackers gather personal information through phishing, social engineering, or data leaks (such as your full name, phone number, id details, etc.). using specialized tools, hackers attempt to extract encryption keys from the sim card, allowing them to program a blank sim with identical data. In this article i’ll explain, in plain language, how sim based attacks work at a high level, what warning signs to watch for, what to do if it happens, and — most importantly — how to lock. The harm inflicted by sim cloning is systemic as well as personal. the victims are deprived of their phones and online accounts, realising the breach only when improper dealings or login attempts have occurred. You're not alone—phone cloning and other violating forms of phone hacking is far too common. but don't worry—we're here to help you regain control of your phone. this wikihow article will show you signs that your phone or sim card is cloned, help you reverse the damage, and teach you how to stay safe from the most common forms of cellular.

Criminals Can Break Into Your Phone In Sim Swapping Attack Without Hackers gather personal information through phishing, social engineering, or data leaks (such as your full name, phone number, id details, etc.). using specialized tools, hackers attempt to extract encryption keys from the sim card, allowing them to program a blank sim with identical data. In this article i’ll explain, in plain language, how sim based attacks work at a high level, what warning signs to watch for, what to do if it happens, and — most importantly — how to lock. The harm inflicted by sim cloning is systemic as well as personal. the victims are deprived of their phones and online accounts, realising the breach only when improper dealings or login attempts have occurred. You're not alone—phone cloning and other violating forms of phone hacking is far too common. but don't worry—we're here to help you regain control of your phone. this wikihow article will show you signs that your phone or sim card is cloned, help you reverse the damage, and teach you how to stay safe from the most common forms of cellular.

Is Your Phone Cloned Sim Swaps Explained Tarrant County S Credit Union The harm inflicted by sim cloning is systemic as well as personal. the victims are deprived of their phones and online accounts, realising the breach only when improper dealings or login attempts have occurred. You're not alone—phone cloning and other violating forms of phone hacking is far too common. but don't worry—we're here to help you regain control of your phone. this wikihow article will show you signs that your phone or sim card is cloned, help you reverse the damage, and teach you how to stay safe from the most common forms of cellular.
Comments are closed.