How Confidential Computing Enables Privacy Preserving

How Confidential Computing Enables Privacy Preserving Confidential computing enables organizations to comply with regulations such as gdpr, hipaa, and ccpa by ensuring that sensitive data is never exposed, even when processed in the cloud. Confidential computing architectures have emerged as essential elements in modern cloud computing infrastructures, addressing critical security concerns regarding data privacy and.
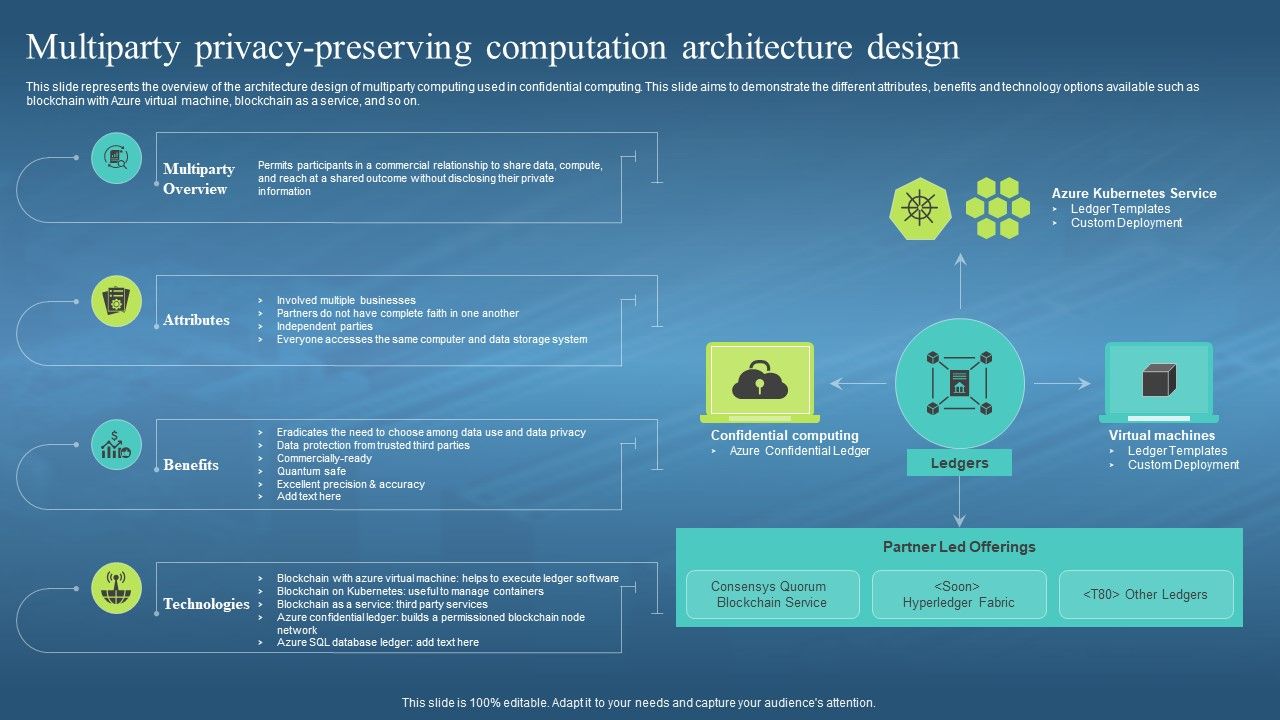
Confidential Computing Hardware Multiparty Privacy Preserving Confidential computing enables secure data sharing and analysis across organizations while preserving patient privacy. confidential computing lets healthcare organizations participate. To learn more about confidential computing, visit the confidential computing consortium (ccc), and take advantage of their resources, white papers, technical documentation, and more. Although organizations define the precise contours of the term differently (table 1), confidential computing generally involves a range of hardware based technologies that isolate data processing and provide technically enforceable administrative safeguards for data while it is actively in use. Secure multi party computation (smpc) is a privacy preserving technology that allows multiple parties to jointly compute a task using distributed algorithms while keeping each party's data private from the others.

Confidential Computing Consortium Multiparty Privacy Preserving Although organizations define the precise contours of the term differently (table 1), confidential computing generally involves a range of hardware based technologies that isolate data processing and provide technically enforceable administrative safeguards for data while it is actively in use. Secure multi party computation (smpc) is a privacy preserving technology that allows multiple parties to jointly compute a task using distributed algorithms while keeping each party's data private from the others. Confidential computing enables ai models to be trained on sensitive data without exposing the raw inputs, preserving privacy while improving performance. What is the importance of confidential computing? confidential computing holds vast potential for industries handling sensitive data, such as healthcare, finance, and government, where preserving privacy is paramount. it's also crucial for cloud based environments. Confidential computing is a set of technologies and processes that protect data in use, meaning data processed in memory or cpu registers, using hardware based isolation and attestation. Confidential computing solves this by using hardware to create a secure, isolated environment during processing. it keeps data encrypted in memory and only decrypts it inside a protected enclave, greatly reducing risks and improving privacy.

Confidential Computing System Technology Multiparty Privacy Preserving Confidential computing enables ai models to be trained on sensitive data without exposing the raw inputs, preserving privacy while improving performance. What is the importance of confidential computing? confidential computing holds vast potential for industries handling sensitive data, such as healthcare, finance, and government, where preserving privacy is paramount. it's also crucial for cloud based environments. Confidential computing is a set of technologies and processes that protect data in use, meaning data processed in memory or cpu registers, using hardware based isolation and attestation. Confidential computing solves this by using hardware to create a secure, isolated environment during processing. it keeps data encrypted in memory and only decrypts it inside a protected enclave, greatly reducing risks and improving privacy.

Privacy Preserving Software As A Service With Confidential Computing Confidential computing is a set of technologies and processes that protect data in use, meaning data processed in memory or cpu registers, using hardware based isolation and attestation. Confidential computing solves this by using hardware to create a secure, isolated environment during processing. it keeps data encrypted in memory and only decrypts it inside a protected enclave, greatly reducing risks and improving privacy.
How Confidential Computing Works Confidential Computing 101
Comments are closed.