How Abusing Docker Api Led To Remote Code Execution Same Origin Bypass More

Black Hat Talk Well That Escalated Quickly How Abusing Docker Api The next step of our attack is to use what was achieved so far to escape the limitations imposed by sop, in order to be able to execute any command against docker daemon rest api. Explore a black hat conference talk that delves into the security vulnerabilities of docker api and their potential for exploitation. learn how abusing docker api can lead to remote code execution, same origin policy bypass, and persistence in hypervisors through shadow containers.

Docker Api Or Agent General Docker Community Forums Datadog security researchers recently encountered a new campaign that targets docker api endpoints publicly exposed without authentication, with the objective of spreading cryptojacking malware. If the api is exposed without authentication and encryption, it allows anyone with network access to the socket to execute docker commands, potentially leading to full system compromise. The vulnerability leverages a misconfigured docker engine api setting, allowing attackers to achieve remote code execution (rce) with minimal user interaction. while docker's default settings are secure, enabling specific configurations can leave systems critically exposed. Initial access is gained by exploiting misconfigured docker apis, followed by deployment of alpine linux containers that mount the host filesystem for persistent access. the operation uses tor hidden services for command and control, making detection and attribution more difficult.

Black Hat Talk Same Origin Method Execution Exploiting A Callback The vulnerability leverages a misconfigured docker engine api setting, allowing attackers to achieve remote code execution (rce) with minimal user interaction. while docker's default settings are secure, enabling specific configurations can leave systems critically exposed. Initial access is gained by exploiting misconfigured docker apis, followed by deployment of alpine linux containers that mount the host filesystem for persistent access. the operation uses tor hidden services for command and control, making detection and attribution more difficult. Well, that escalated quickly! how abusing the docker api led to remote code execution, same origin bypass and persistence in the hypervisor via shadow containers. michael cherny @chernymi. How abusing docker api led to remote code execution, same origin bypass and persistence in the hypervisor via shadow containers with over 5 billion pulls from the docker hub,. This comprehensive post delves into the murky waters of these api attack campaigns, exploring their tactics, techniques, and the crucial steps you can take to secure your docker environment. A new strain of malware has been identified in akamai hunt’s honeypot infrastructure that targets misconfigured docker apis to gain full root access and establish long term persistence.

Exploitation Of Docker Remote Api Servers Has Reached A Critical Level Well, that escalated quickly! how abusing the docker api led to remote code execution, same origin bypass and persistence in the hypervisor via shadow containers. michael cherny @chernymi. How abusing docker api led to remote code execution, same origin bypass and persistence in the hypervisor via shadow containers with over 5 billion pulls from the docker hub,. This comprehensive post delves into the murky waters of these api attack campaigns, exploring their tactics, techniques, and the crucial steps you can take to secure your docker environment. A new strain of malware has been identified in akamai hunt’s honeypot infrastructure that targets misconfigured docker apis to gain full root access and establish long term persistence.
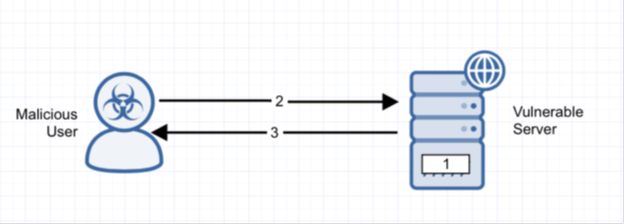
Docker Daemon Public Api Security Misconfiguration Alert Logic This comprehensive post delves into the murky waters of these api attack campaigns, exploring their tactics, techniques, and the crucial steps you can take to secure your docker environment. A new strain of malware has been identified in akamai hunt’s honeypot infrastructure that targets misconfigured docker apis to gain full root access and establish long term persistence.
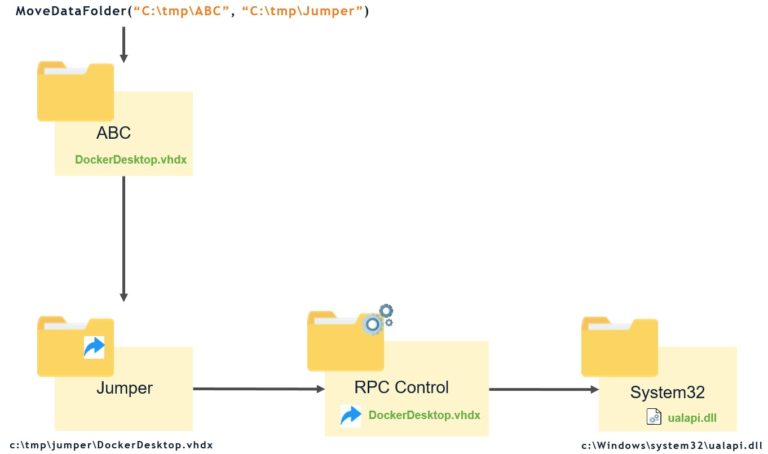
Breaking Docker Named Pipes Systematically Docker Desktop Privilege
Comments are closed.