How A Zero Day Exploit Works

5 Ways To Protect Yourself From A Zero Day Exploit Learn what a zero day exploit is, why it poses such a severe risk, and how organizations can detect and mitigate zero day attacks using proactive threat intelligence. A zero day exploit is a method or code specifically engineered to trigger the underlying vulnerability. it enables attackers to take desired actions—such as executing commands, escalating privileges, or bypassing authentication—by exploiting the flaw.
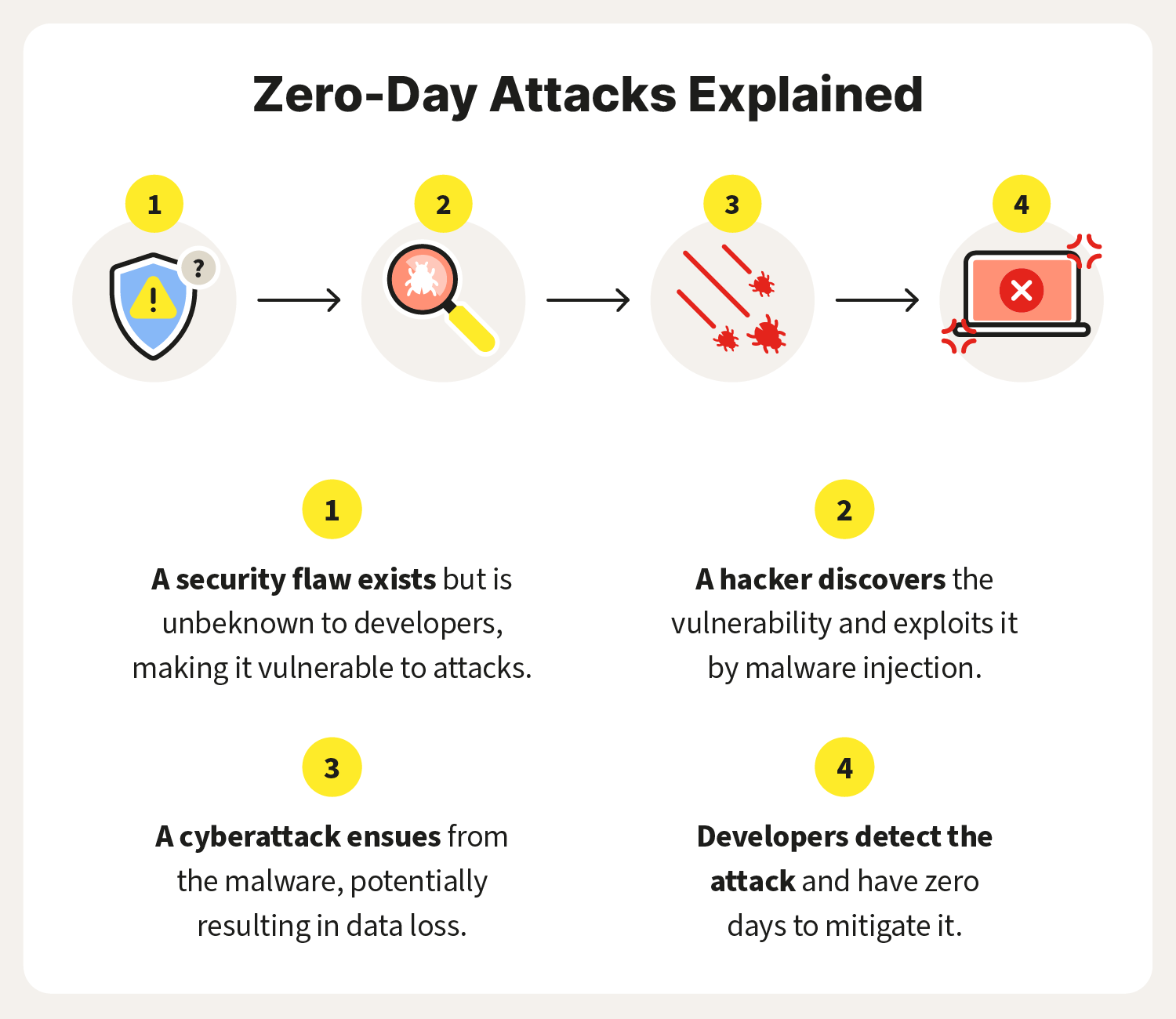
What Is A Zero Day Exploit Definition And Prevention Tips 41 Off This article is a complete guide to zero day exploits and how companies deal with the danger of undiscovered security flaws in it systems. we explain how zero day exploits typically occur and present the most effective ways to prevent hackers from leveraging unknown vulnerabilities in your systems. This guide breaks down how zero day exploits work and who’s behind them. we’ll cover practical defenses your team can implement today, famous examples from stuxnet to moveit, plus current statistics on the evolving threat landscape. Zero day exploit is a type of cyber security attack that occurs on the same day the software, hardware, or firmware flaw is detected by the manufacturer. as it’s been zero days since the security flaw was last exploited, the attack is termed a zero day exploit or zero day attack. Zero day exploits work by taking advantage of software flaws nobody else has spotted yet, not even the people who built it. attackers move fast, slipping in before anyone knows there’s a problem, so there’s no fix, no warning, nothing to stop them.
Preventing Zero Day Exploits And Attacks Scan On Computer Zero day exploit is a type of cyber security attack that occurs on the same day the software, hardware, or firmware flaw is detected by the manufacturer. as it’s been zero days since the security flaw was last exploited, the attack is termed a zero day exploit or zero day attack. Zero day exploits work by taking advantage of software flaws nobody else has spotted yet, not even the people who built it. attackers move fast, slipping in before anyone knows there’s a problem, so there’s no fix, no warning, nothing to stop them. In cybersecurity, a zero day exploit involves exploiting a flaw in software before the developer has had a chance to address and patch the vulnerability. this means that the exploit can be used effectively and silently until the flaw is discovered and resolved. Zero day exploit: a zero day exploit starts with a software developer releasing insecure code that a malicious actor discovers flaw and exploits it. the attacker then either succeeds in committing identity or information theft, or the developer produces a patch to limit the spread of the attack. Unlike known vulnerabilities that can be patched through regular updates, zero day exploits give cybercriminals a head start, allowing them to infiltrate systems without detection. the exploits can be used to deploy malware, steal data or even take control of critical systems. A zero day exploit is a software vulnerability that attackers discover before developers can patch it. this guide explains how zero days work, how attackers weaponize them, how to detect and defend against them, and how penligent helps organizations build true zero day resilience.

What Is A Zero Day Exploit Askcybersecurity In cybersecurity, a zero day exploit involves exploiting a flaw in software before the developer has had a chance to address and patch the vulnerability. this means that the exploit can be used effectively and silently until the flaw is discovered and resolved. Zero day exploit: a zero day exploit starts with a software developer releasing insecure code that a malicious actor discovers flaw and exploits it. the attacker then either succeeds in committing identity or information theft, or the developer produces a patch to limit the spread of the attack. Unlike known vulnerabilities that can be patched through regular updates, zero day exploits give cybercriminals a head start, allowing them to infiltrate systems without detection. the exploits can be used to deploy malware, steal data or even take control of critical systems. A zero day exploit is a software vulnerability that attackers discover before developers can patch it. this guide explains how zero days work, how attackers weaponize them, how to detect and defend against them, and how penligent helps organizations build true zero day resilience.
Comments are closed.