Host Header Injection Attack Authentication Bypass
Phases Of Host Header Injection While developers often focus on endpoints and payloads, attackers see headers as fertile ground for injection, spoofing, and misdirection. improperly handled headers can lead to severe. One way for a web application to take a guess where the visitor comes from is the host header. normal browsers always keep it in sync with the target of the connection, so it is not possible to send the request to one host but have another value in the host header.
Host Header Attack Bypass authentication and authorization: certain applications rely on the host header for authentication or authorization checks. by manipulating the header, attackers might be able to bypass these checks and gain unauthorized access to restricted resources or functionalities. When an application implements incomplete checks on the host value, these protections can allow targeted bypasses. here are the most common cases and how to exploit them. Bypass security controls that rely on the header. initial testing is as simple as supplying another domain (i.e. attacker ) into the host header field. it is how the web server processes the header value that dictates the impact. The website may block requests with multiple host headers, but you may be able to bypass this validation by indenting one of them like this. if the front end ignores the indented header, the request will be processed as an ordinary request for vulnerable website .
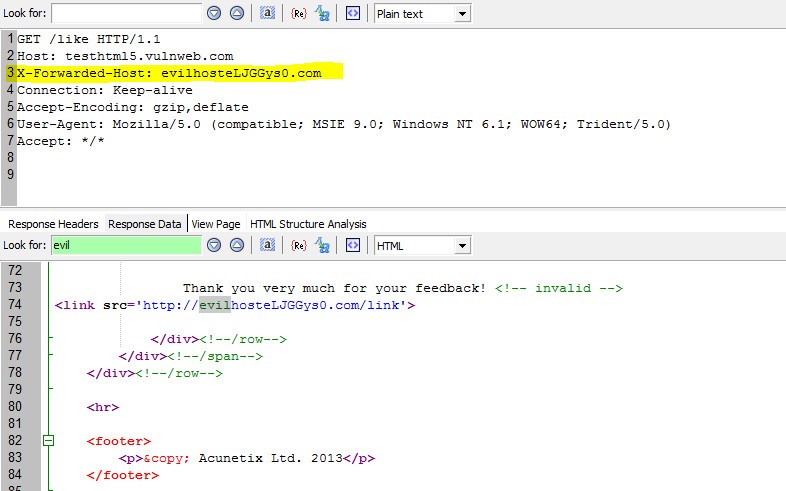
Host Header Attack Bypass security controls that rely on the header. initial testing is as simple as supplying another domain (i.e. attacker ) into the host header field. it is how the web server processes the header value that dictates the impact. The website may block requests with multiple host headers, but you may be able to bypass this validation by indenting one of them like this. if the front end ignores the indented header, the request will be processed as an ordinary request for vulnerable website . While technically simple to exploit, the consequences of a host header attack are severe, enabling phishing campaigns that are highly convincing because they appear to originate from a legitimate domain. Today, i’m sharing a critical vulnerability i discovered that led to both verification bypass and authentication bypass — a pretty dangerous combination if left unchecked. Cve id :cve 2026 33511 published : march 24, 2026, 8:16 p.m. | 52 minutes ago description :pyload is a free and open source download manager written in python. from version 0.4.20 to before version 0.5.0b3.dev97, the local check decorator in pyload’s clicknload feature can be bypassed by any remote attacker through http host header spoofing. this allows unauthenticated remote. Host header injection is one of those deceptively simple vulnerabilities that can quietly undermine password reset flows, poison caches, bypass authentication logic, and even lead to full account takeover.
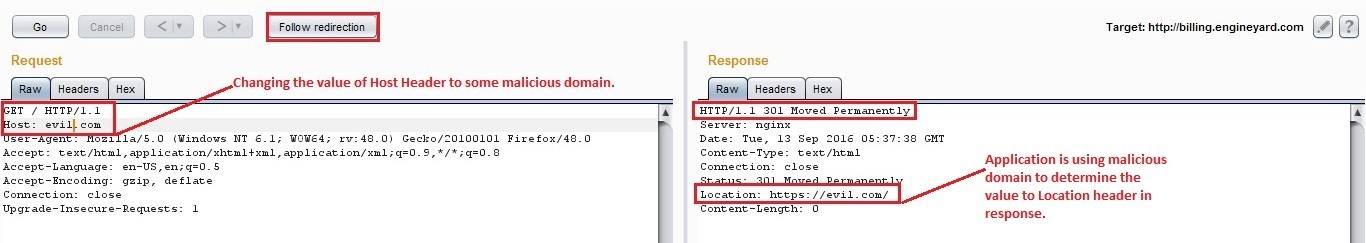
Host Header Attack While technically simple to exploit, the consequences of a host header attack are severe, enabling phishing campaigns that are highly convincing because they appear to originate from a legitimate domain. Today, i’m sharing a critical vulnerability i discovered that led to both verification bypass and authentication bypass — a pretty dangerous combination if left unchecked. Cve id :cve 2026 33511 published : march 24, 2026, 8:16 p.m. | 52 minutes ago description :pyload is a free and open source download manager written in python. from version 0.4.20 to before version 0.5.0b3.dev97, the local check decorator in pyload’s clicknload feature can be bypassed by any remote attacker through http host header spoofing. this allows unauthenticated remote. Host header injection is one of those deceptively simple vulnerabilities that can quietly undermine password reset flows, poison caches, bypass authentication logic, and even lead to full account takeover.
What Is Http Header Injection Acunetix Cve id :cve 2026 33511 published : march 24, 2026, 8:16 p.m. | 52 minutes ago description :pyload is a free and open source download manager written in python. from version 0.4.20 to before version 0.5.0b3.dev97, the local check decorator in pyload’s clicknload feature can be bypassed by any remote attacker through http host header spoofing. this allows unauthenticated remote. Host header injection is one of those deceptively simple vulnerabilities that can quietly undermine password reset flows, poison caches, bypass authentication logic, and even lead to full account takeover.

What Is A Host Header Attack Acunetix
Comments are closed.