Hooking Java Methods With Frida
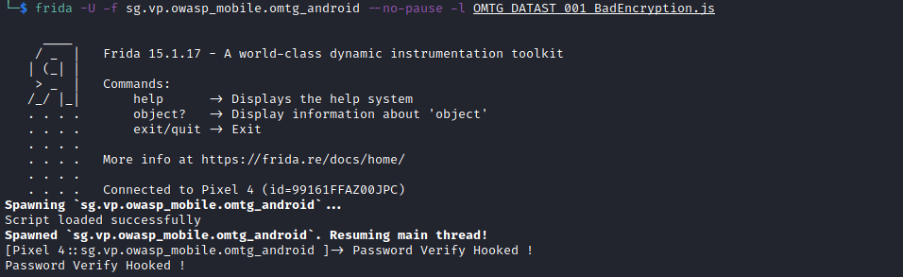
Github Frida Frida Java Bridge Java Runtime Interop From Frida Method 2: java hook (bypassing cmpstr) instead of guessing the correct input, we can modify how cmpstr works using frida, a powerful android dynamic analysis tool. This document explains the fundamental concepts and mechanisms for intercepting and replacing java method implementations using javascript. method hooking is the core instrumentation technique in frida java bridge, allowing you to observe and modify the behavior of java methods at runtime.

Júlio César Magro On Linkedin Hooking Java Methods With Frida In this video, we use frida to hook and augment the functionality of a java method in an android application. more. The frida trace command line argument for hooking an java android method is j. you always have to specify a class name and a method name and optional the search options. After putting this all together, i was able to use frida trace to hook thousands of methods and obtain understandable output. i especially found the ability to view the content of byte arrays as ascii text super useful. This tutorial is noob friendly and its purpose is to introduce people in hooking methods with frida and more specifically native methods. we are going to present the entire process from having just the apk and move on step by step.
Frida Can T Hook Java Lang Runtime In Application Issue 410 Frida After putting this all together, i was able to use frida trace to hook thousands of methods and obtain understandable output. i especially found the ability to view the content of byte arrays as ascii text super useful. This tutorial is noob friendly and its purpose is to introduce people in hooking methods with frida and more specifically native methods. we are going to present the entire process from having just the apk and move on step by step. This project demonstrates how to perform native hooking on android applications using frida. it includes scripts for intercepting and logging jni function calls within native libraries. In the following section, we will demonstrate a technique for capturing the return value of a java method using a tool called frida—a dynamic instrumentation toolkit widely used by developers, reverse engineers, and security researchers. This article explores how frida handles the interception of java and native methods, detailing the underlying mechanisms and practical implications for security testing and reverse engineering. This page provides practical examples demonstrating the most common operations in frida java bridge. it covers loading classes, creating instances, calling methods, hooking implementations, accessing fields, and manipulating objects.

Hook Hooking Android Method With Frida But Implementation Not This project demonstrates how to perform native hooking on android applications using frida. it includes scripts for intercepting and logging jni function calls within native libraries. In the following section, we will demonstrate a technique for capturing the return value of a java method using a tool called frida—a dynamic instrumentation toolkit widely used by developers, reverse engineers, and security researchers. This article explores how frida handles the interception of java and native methods, detailing the underlying mechanisms and practical implications for security testing and reverse engineering. This page provides practical examples demonstrating the most common operations in frida java bridge. it covers loading classes, creating instances, calling methods, hooking implementations, accessing fields, and manipulating objects.
Frida Hooking Native Functions Are You Ready For Part 3 This Is The This article explores how frida handles the interception of java and native methods, detailing the underlying mechanisms and practical implications for security testing and reverse engineering. This page provides practical examples demonstrating the most common operations in frida java bridge. it covers loading classes, creating instances, calling methods, hooking implementations, accessing fields, and manipulating objects.
Comments are closed.