History Audit Logs
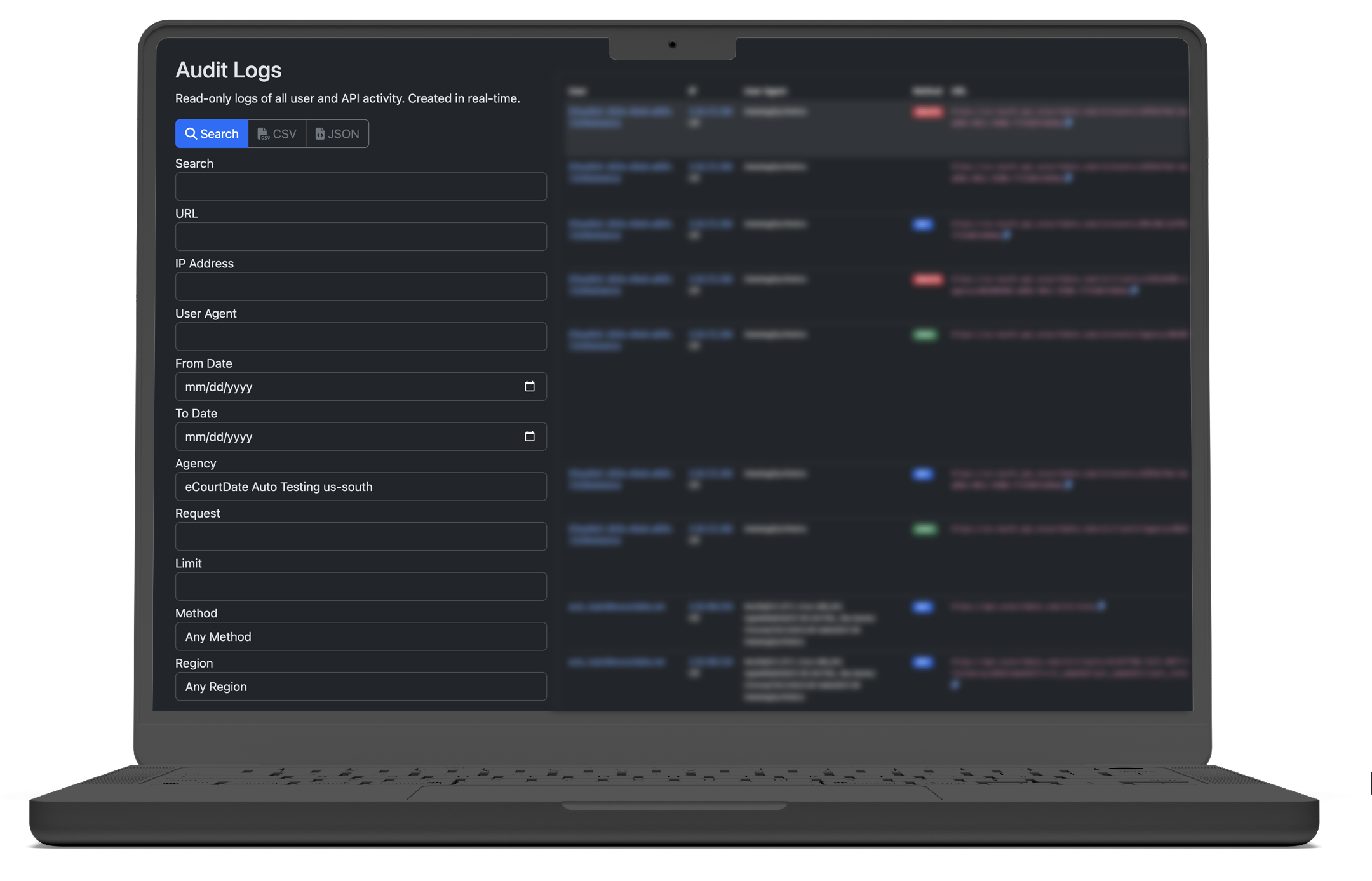
Real Time User And System Activity Logs The tables in this article describe the activities recorded in the microsoft 365 audit log. you can search for these activities by searching the audit log in the microsoft purview portal. In this guide, you’ll learn how audit logs work, what they track, and how middleware simplifies secure, centralized audit logging for compliance and observability.
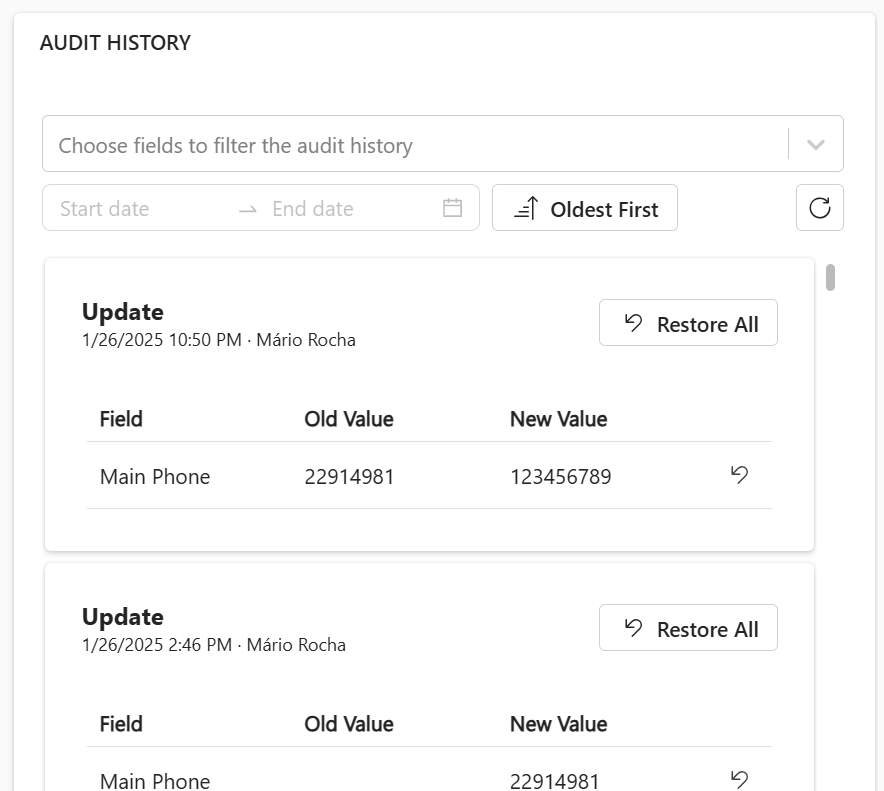
Audit History Pcf Gallery Audit logs contain detailed historical information that can be used to reconstruct the timeline of a system outage or incident. for instance, logs can help distinguish between operator error and system error. Learn what audit logs are, why they matter for compliance and security, and how to implement them effectively to protect your enterprise data and meet regulations. Audit logging records who did what, when, and where across systems for accountability and forensic tracing. analogy: audit logs are the black box recorder for digital systems. formal: tamper evident sequential records of security relevant events captured with contextual metadata for detection, compliance, and investigation. An audit log, often called an audit trail or audit history, is a chronological record of events, actions and changes within a computer system, software application, network or organization.
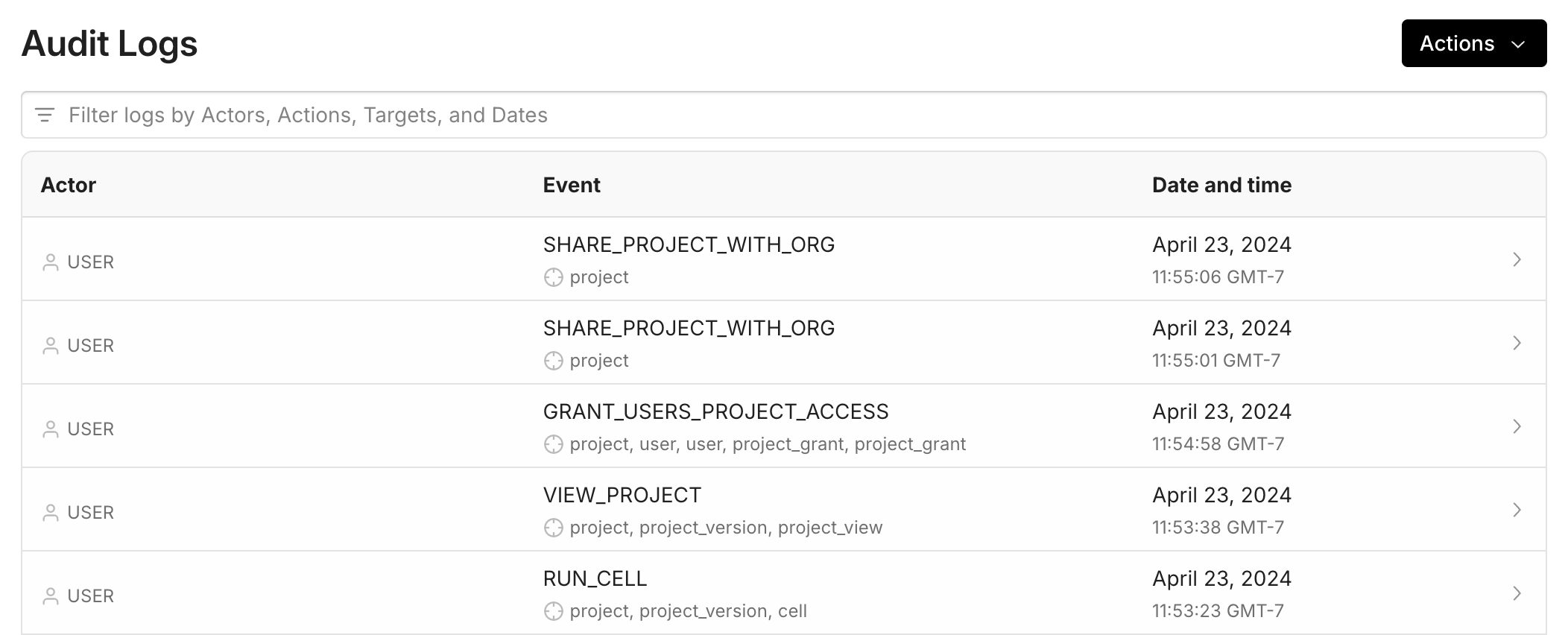
Audit Logs Overview Learn Hex Technologies Audit logging records who did what, when, and where across systems for accountability and forensic tracing. analogy: audit logs are the black box recorder for digital systems. formal: tamper evident sequential records of security relevant events captured with contextual metadata for detection, compliance, and investigation. An audit log, often called an audit trail or audit history, is a chronological record of events, actions and changes within a computer system, software application, network or organization. The answer is relatively simple, and it lies in audit logs. these digital breadcrumbs track every login and modification for a detailed history of actions. whether you need to trace the source of a security breach or simply verify a user’s activity, audit logs are the ideal tool. What are audit logs? audit logs are text files that record events and changes within a system. they are typically stored in a secure location and can be generated by specific processes or monitoring tools. Activity history and audit trail software that logs every action across tasks, docs, and workflows. full transparency. compliance ready. It provides a detailed, time stamped audit trail of every single action performed by any user within the project. this feature is essential for security, accountability, troubleshooting, and understanding the complete history of your project.
Comments are closed.