Hill Cipher Problem Pdf Cryptography Secure Communication

Hill Cipher Problem Pdf Cryptography Secure Communication The hill cipher is based on linear algebra and overcomes the frequency distribution problem of the caesar cipher that was previously discussed. the rest of this paper will be devoted to an explanation of the hill cipher, its shortcomings, and one way to secure the cipher further. Cryptography plays a vital role in securing sensitive information in various domains. hill cipher, a classic encryption technique, has been widely used for its simplicity and effectiveness.

Hill Cipher Pdf Hill cipher free download as pdf file (.pdf), text file (.txt) or read online for free. the document appears to outline a cryptographic process involving encryption and decryption using modular arithmetic. Abstract— cryptography has a crucial role in securing data by preventing unauthorized access and ensuring the confidentiality and integrity of data. among various cryptographic techniques that have been developed, the hill cipher stands out as an early method founded on linear algebra principles. Cryptography is needed so that text can be kept secret. it is easy to imagine situations in ancient times where a writer who sent a message via courier would want to make sure that if the runner were intercepted, the interceptors could not read the message. In this paper, the novel block hill cipher represents a notable advancement in cryptographic techniques, providing improved security, versatility, and efficiency.

Hill Cipher 1 Pdf Cryptography is needed so that text can be kept secret. it is easy to imagine situations in ancient times where a writer who sent a message via courier would want to make sure that if the runner were intercepted, the interceptors could not read the message. In this paper, the novel block hill cipher represents a notable advancement in cryptographic techniques, providing improved security, versatility, and efficiency. In this paper, a secure cryptosystem is introduced that overcomes all the security drawbacks of the hill cipher. the proposed scheme includes an encryption algorithm that is a variant of the affine hill cipher for which a secure cryptographic protocol is introduced. Using a known plaintext attack, we can break the hill cipher with n blocks (of n letters) of matching plain ciphertext pairs. consider the following: let's say we know that "ma" encrypts to "ku" and that "th" encrypts to "mt". Since the letter frequencies are masked the hill cipher is considerably more difficult to crack than a monoalphabetic substitution that is vulnerable to frequency analysis. D american mathematician, conceived and developed the hill cipher method in 1929. hill cipher employs a variety of mathematical techniques, including numerous traditional cryptographic approaches. plaintext is separated into groups of letters of a predetermined si.
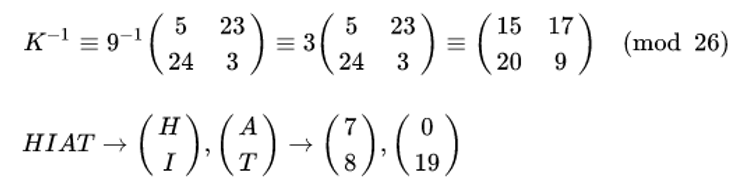
Hill Cipher In Cryptography In this paper, a secure cryptosystem is introduced that overcomes all the security drawbacks of the hill cipher. the proposed scheme includes an encryption algorithm that is a variant of the affine hill cipher for which a secure cryptographic protocol is introduced. Using a known plaintext attack, we can break the hill cipher with n blocks (of n letters) of matching plain ciphertext pairs. consider the following: let's say we know that "ma" encrypts to "ku" and that "th" encrypts to "mt". Since the letter frequencies are masked the hill cipher is considerably more difficult to crack than a monoalphabetic substitution that is vulnerable to frequency analysis. D american mathematician, conceived and developed the hill cipher method in 1929. hill cipher employs a variety of mathematical techniques, including numerous traditional cryptographic approaches. plaintext is separated into groups of letters of a predetermined si.
Comments are closed.