Hill Cipher Pdf Cryptography Secrecy

Hill Cipher Pdf The document describes hill ciphers, a polygraphic substitution cipher invented in 1929. it uses linear algebra and modular arithmetic to encrypt messages by applying an encryption matrix to blocks of letters, and decrypts using the inverse decryption matrix. 1 encryption 1.1 formula the general formula for encrypting text using the hill cipher algorithm is k × p mod 26. where k is our n × n matrix that serves as the key. the determinant of k must be relatively prime with 26. p is our text we want to encrypt in the form of an n × 1 matrix.

Hill Cipher Pdf Cryptography plays a vital role in securing sensitive information in various domains. hill cipher, a classic encryption technique, has been widely used for its simplicity and effectiveness. Since the letter frequencies are masked the hill cipher is considerably more difficult to crack than a monoalphabetic substitution that is vulnerable to frequency analysis. In this literature, we take a square matrix of order 3x3 and use 36 characters (a z, 0 9). to produce cipher text, the method used is to carry out an encryption process based on the hill cipher algorithm. the encryption process is carried out by multiplying the key matrix by the plaintext. The hill cipher is based on linear algebra and overcomes the frequency distribution problem of the caesar cipher that was previously discussed. the rest of this paper will be devoted to an explanation of the hill cipher, its shortcomings, and one way to secure the cipher further.

Hill Cipher Pdf Encryption Applied Mathematics In this literature, we take a square matrix of order 3x3 and use 36 characters (a z, 0 9). to produce cipher text, the method used is to carry out an encryption process based on the hill cipher algorithm. the encryption process is carried out by multiplying the key matrix by the plaintext. The hill cipher is based on linear algebra and overcomes the frequency distribution problem of the caesar cipher that was previously discussed. the rest of this paper will be devoted to an explanation of the hill cipher, its shortcomings, and one way to secure the cipher further. To use the key to transform plaintext into ciphertext is to encipher the plaintext. to use the inverse key to transform the ciphertext back into plaintext is to decipher the ciphertext. Abstract— cryptography has a crucial role in securing data by preventing unauthorized access and ensuring the confidentiality and integrity of data. among various cryptographic techniques that have been developed, the hill cipher stands out as an early method founded on linear algebra principles. The hill cipher in cryptography is used to explain the application of matrices defined over a finite field, and the handling of characters and strings in computer programs. Cryptographic tools like hill's encryption algorithm protect digital data. in this work, we present a novel hill cipher security method that utilizes gaussian integers from number.
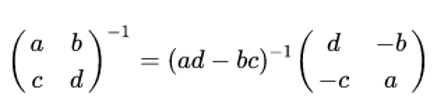
Hill Cipher In Cryptography To use the key to transform plaintext into ciphertext is to encipher the plaintext. to use the inverse key to transform the ciphertext back into plaintext is to decipher the ciphertext. Abstract— cryptography has a crucial role in securing data by preventing unauthorized access and ensuring the confidentiality and integrity of data. among various cryptographic techniques that have been developed, the hill cipher stands out as an early method founded on linear algebra principles. The hill cipher in cryptography is used to explain the application of matrices defined over a finite field, and the handling of characters and strings in computer programs. Cryptographic tools like hill's encryption algorithm protect digital data. in this work, we present a novel hill cipher security method that utilizes gaussian integers from number.
Comments are closed.