Hill Cipher Explained With Example

Hill Cipher Pdf Master the hill cipher through comprehensive step by step examples that progress from simple 2x2 matrix encryption to advanced 3x3 implementations and cryptanalysis techniques. these examples provide complete calculations, demonstrating every stage of the encryption and decryption process. Hill cipher is a polygraphic substitution cipher based on linear algebra. in this method, each letter of the alphabet is represented by a number modulo 26, commonly using the scheme a = 0, b = 1, …, z = 25.

Hill Cipher Pdf The document provides an overview of the hill cipher, a polygraphic substitution cipher invented by lester s. hill in 1929, which utilizes linear algebra and matrix operations for encryption and decryption. The hill cipher is famous because it brings linear algebra into cryptography. instead of substituting letters one at a time, it encrypts blocks (pairs, triples, etc.), which can better obscure single letter frequencies. To keep the example basic, we will use a simple substitution method in which the letter a is mapped to 0, b is mapped to 1, and so on to adhere to a 2x2 key matrix. the hill cipher becomes more complicated as the key matrix size grows. The hill cipher is a polygraphic substitution cipher that utilizes linear algebra concepts to encrypt and decrypt messages. invented by lester s. hill in 1929, it operates on blocks of letters,.
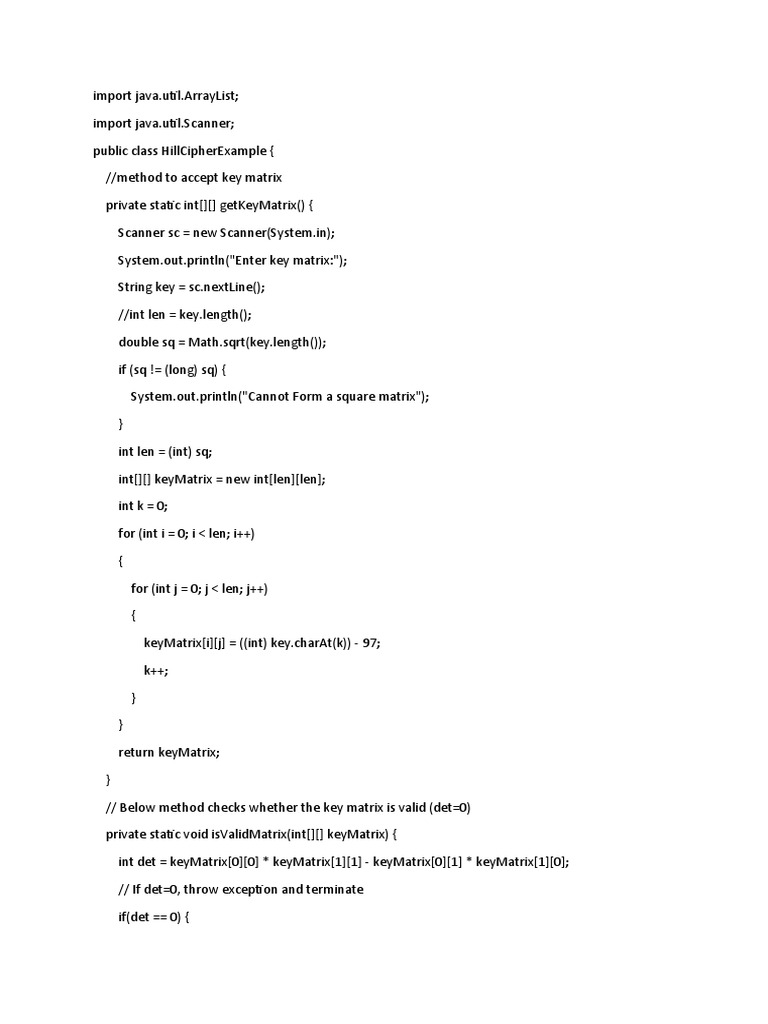
Hill Cipher Pdf Encryption Cryptography To keep the example basic, we will use a simple substitution method in which the letter a is mapped to 0, b is mapped to 1, and so on to adhere to a 2x2 key matrix. the hill cipher becomes more complicated as the key matrix size grows. The hill cipher is a polygraphic substitution cipher that utilizes linear algebra concepts to encrypt and decrypt messages. invented by lester s. hill in 1929, it operates on blocks of letters,. In this video, the hill cipher technique in cryptography is explained with a clear step by step example. What is the hill cipher? the hill cipher is a polygraphic substitution cipher built on concepts from linear algebra. the hill cipher makes use of modulo arithmetic, matrix multiplication, and matrix inverses; hence, it is a more mathematical cipher than others. In classical cryptography, the hill cipher is a polygraphic substitution cipher based on linear algebra. invented by lester s. hill in 1929, it was the first polygraphic cipher in which it was practical (though barely) to operate on more than three symbols at once. To counter charges that his system was too complicated for day to day use, hill constructed a cipher machine for his system using a series of geared wheels and chains. however, the machine never really sold. hill's major contribution was the use of mathematics to design and analyse cryptosystems.

Hill Cipher Pdf Encryption Secure Communication In this video, the hill cipher technique in cryptography is explained with a clear step by step example. What is the hill cipher? the hill cipher is a polygraphic substitution cipher built on concepts from linear algebra. the hill cipher makes use of modulo arithmetic, matrix multiplication, and matrix inverses; hence, it is a more mathematical cipher than others. In classical cryptography, the hill cipher is a polygraphic substitution cipher based on linear algebra. invented by lester s. hill in 1929, it was the first polygraphic cipher in which it was practical (though barely) to operate on more than three symbols at once. To counter charges that his system was too complicated for day to day use, hill constructed a cipher machine for his system using a series of geared wheels and chains. however, the machine never really sold. hill's major contribution was the use of mathematics to design and analyse cryptosystems.
Comments are closed.