Hill Cipher Encryption Pdf
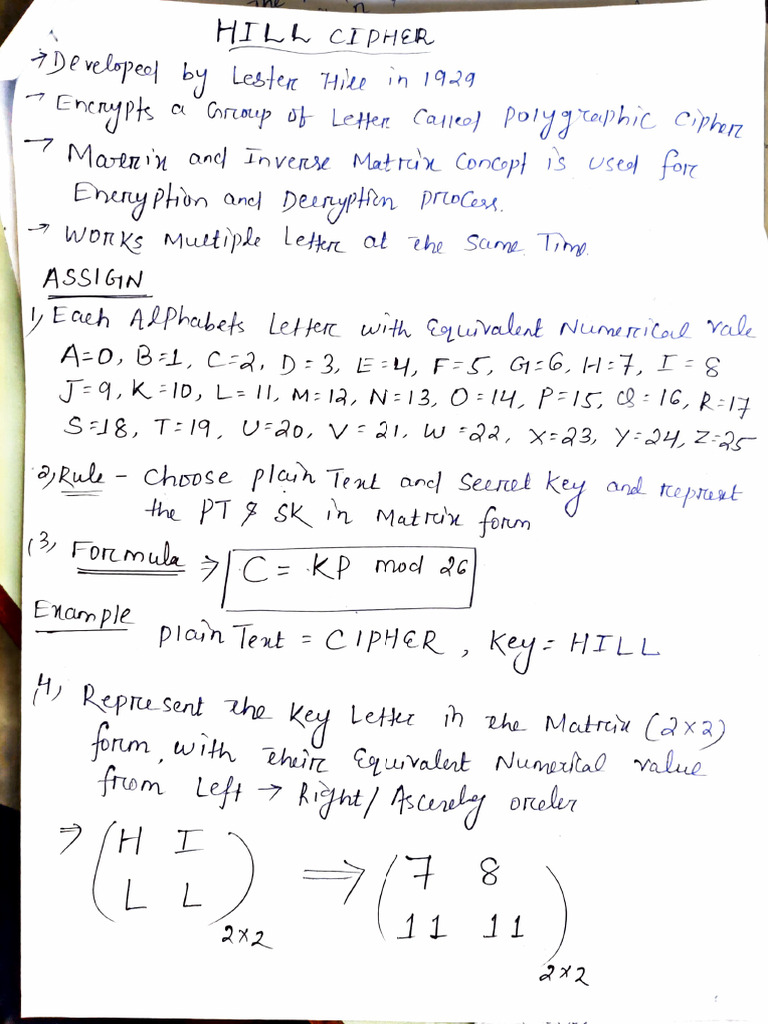
Hill Cipher Encryption Technique Pdf 1 encryption 1.1 formula the general formula for encrypting text using the hill cipher algorithm is k × p mod 26. where k is our n × n matrix that serves as the key. the determinant of k must be relatively prime with 26. p is our text we want to encrypt in the form of an n × 1 matrix. To encrypt a message using the hill cipher we must first turn our keyword into a key matrix (a 2 × 2 matrix for working with digraphs, a 3 × 3 matrix for working with trigraphs, etc.).

Advanced Encryption Standard Aes And Hill Cipher A Comparative Study The hill cipher is based on linear algebra and overcomes the frequency distribution problem of the caesar cipher that was previously discussed. the rest of this paper will be devoted to an explanation of the hill cipher, its shortcomings, and one way to secure the cipher further. Given the focus of this paper on the hill cipher, which is a symmetric encryption algorithm, the following sections will delve deeper into the principles and applications of symmetric encryption. To produce cipher text, the method used is to carry out an encryption process based on the hill cipher algorithm. the encryption process is carried out by multiplying the key matrix by the plaintext. Since the letter frequencies are masked the hill cipher is considerably more difficult to crack than a monoalphabetic substitution that is vulnerable to frequency analysis.

Implement Hill Cipher Encryption Decryption To produce cipher text, the method used is to carry out an encryption process based on the hill cipher algorithm. the encryption process is carried out by multiplying the key matrix by the plaintext. Since the letter frequencies are masked the hill cipher is considerably more difficult to crack than a monoalphabetic substitution that is vulnerable to frequency analysis. Cryptography plays a vital role in securing sensitive information in various domains. hill cipher, a classic encryption technique, has been widely used for its simplicity and effectiveness. Using a known plaintext attack, we can break the hill cipher with n blocks (of n letters) of matching plain ciphertext pairs. consider the following: let's say we know that "ma" encrypts to "ku" and that "th" encrypts to "mt". Hill ciphers (invented in 1929) are a type of block cipher: the ciphertext character that replaces a particular plaintext character in the encryption will depend on the neighboring plaintext characters. Hill cipher free download as pdf file (.pdf), text file (.txt) or read online for free. the document reports on a study of the hill cipher encryption and decryption algorithm.

Image Encryption Using Advanced Hill Cipher Algorithm Pdf Cryptography plays a vital role in securing sensitive information in various domains. hill cipher, a classic encryption technique, has been widely used for its simplicity and effectiveness. Using a known plaintext attack, we can break the hill cipher with n blocks (of n letters) of matching plain ciphertext pairs. consider the following: let's say we know that "ma" encrypts to "ku" and that "th" encrypts to "mt". Hill ciphers (invented in 1929) are a type of block cipher: the ciphertext character that replaces a particular plaintext character in the encryption will depend on the neighboring plaintext characters. Hill cipher free download as pdf file (.pdf), text file (.txt) or read online for free. the document reports on a study of the hill cipher encryption and decryption algorithm.

Hill Cipher Pdf Hill ciphers (invented in 1929) are a type of block cipher: the ciphertext character that replaces a particular plaintext character in the encryption will depend on the neighboring plaintext characters. Hill cipher free download as pdf file (.pdf), text file (.txt) or read online for free. the document reports on a study of the hill cipher encryption and decryption algorithm.
Comments are closed.