Hill Cipher Encryption And Decryption In Python Part Ii
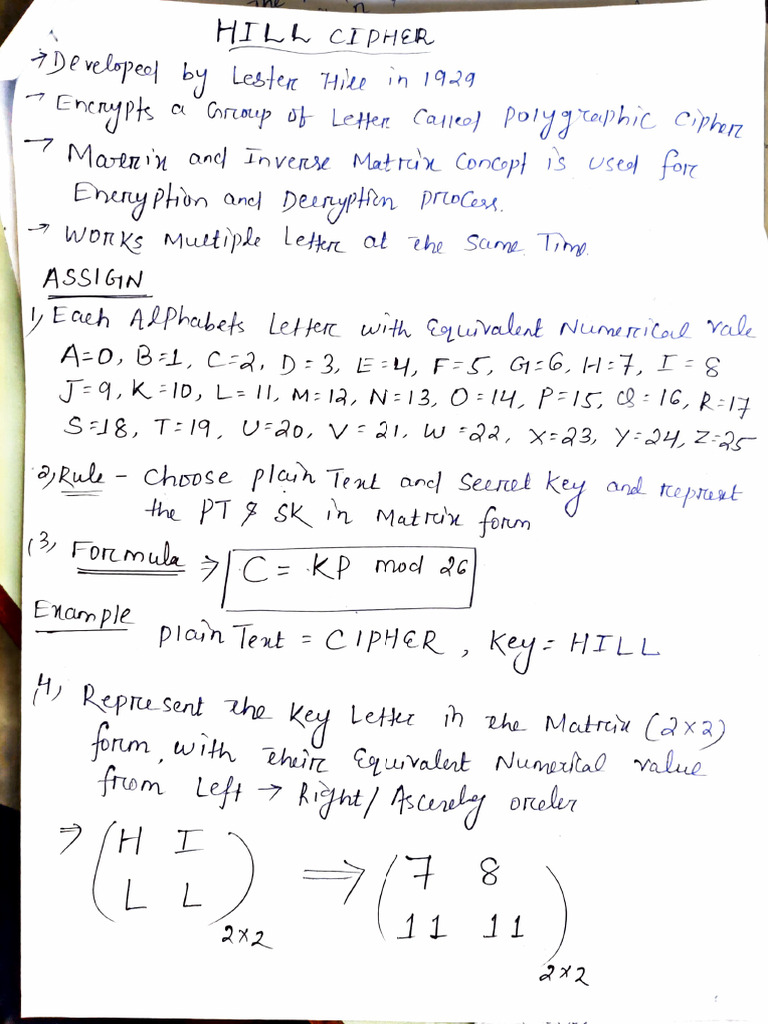
Hill Cipher Encryption Technique Pdf Learn how to apply the hill encryption method in python to encrypt and decrypt latin phrases using a key matrix. this tutorial provides a step by step guide and code examples. Hill cipher: the ‘hillcipher’ class below implements the hill cipher algorithm which uses modern linear algebra techniques to encode and decode text using an encryption key matrix.
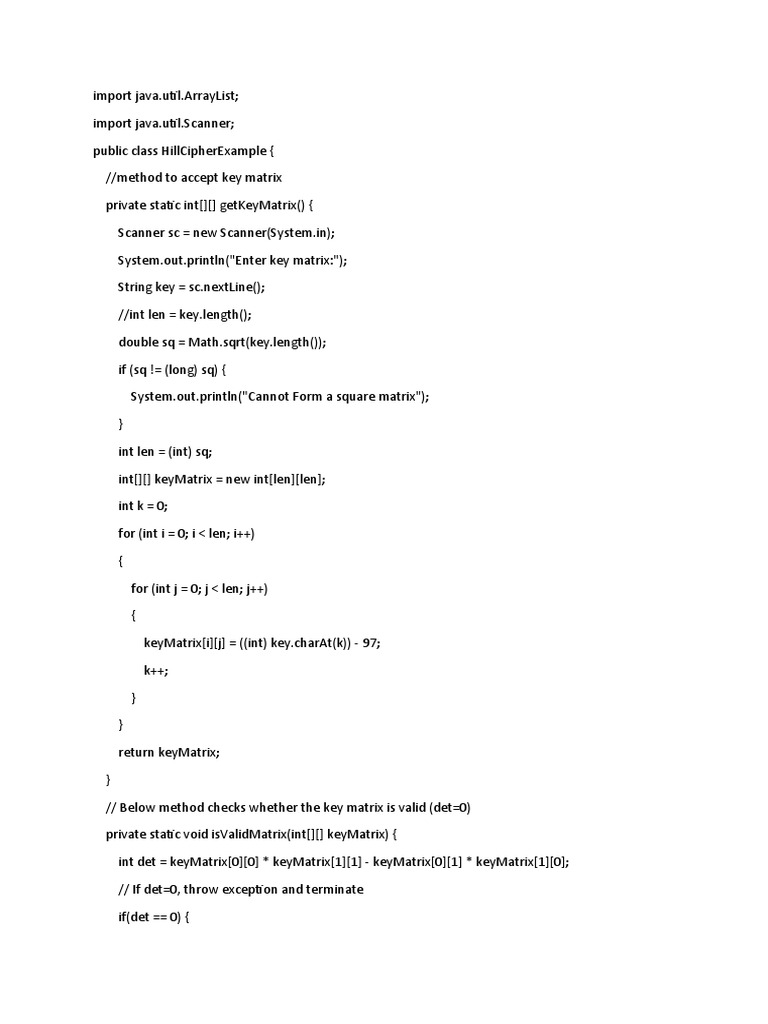
Hill Cipher Pdf Encryption Cryptography Hill cipher is a polygraphic substitution cipher based on linear algebra. in this method, each letter of the alphabet is represented by a number modulo 26, commonly using the scheme a = 0, b = 1, …, z = 25. Through this project, i explored the fundamental concepts behind the hill cipher and gained practical experience in combining mathematics with cryptography in python. Master the hill cipher through comprehensive step by step examples that progress from simple 2x2 matrix encryption to advanced 3x3 implementations and cryptanalysis techniques. these examples provide complete calculations, demonstrating every stage of the encryption and decryption process. Part 2: hill cipher decryption in python with complete elaboration of each step. make sure to watch part 1 to be able to understand.part 1: youtu.be.

Hill Cipher Pdf Encryption Secure Communication Master the hill cipher through comprehensive step by step examples that progress from simple 2x2 matrix encryption to advanced 3x3 implementations and cryptanalysis techniques. these examples provide complete calculations, demonstrating every stage of the encryption and decryption process. Part 2: hill cipher decryption in python with complete elaboration of each step. make sure to watch part 1 to be able to understand.part 1: youtu.be. Filter files by name, interpreter, abi, and platform. if you're not sure about the file name format, learn more about wheel file names. a simple implementation of the hill cipher encryption and decryption. In this article, we’ll walk through a python program that encrypts and decrypts messages using the hill cipher, one of the earliest examples of polygraphic substitution ciphers based on. I doubt the encryption have any issue but when i encrypt and decrypt i should receive the original message but yet i'm receiving a whole new text. i cant seem to find the error. In the examples given, we shall walk through all the steps to use this cipher to act on digraphs and trigraphs. it can be extended further, but this then requires a much deeper knowledge of the background mathematics.
Comments are closed.