Hill Cipher Algorithm Decryption With Example
Decryption Hill Cipher Hill cipher is a polygraphic substitution cipher based on linear algebra. in this method, each letter of the alphabet is represented by a number modulo 26, commonly using the scheme a = 0, b = 1, …, z = 25. This page provides comprehensive hill cipher examples with complete step by step solutions, including 2x2 and 3x3 encryption and decryption, keyword to matrix conversion, known plaintext attack demonstrations, and detailed mathematical calculations.
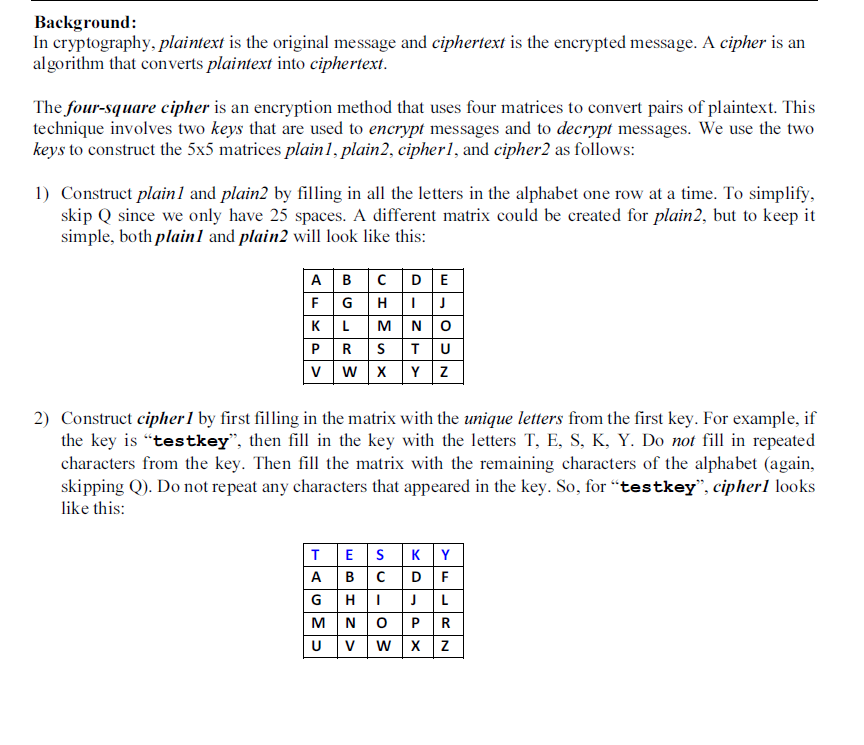
Hill Cipher Decryption Tool Timegas This python code builds the hill cipher encryption algorithm with the help of numpy for matrix operations. it creates functions to define the key matrix from a given key, encrypt a message with the help of the generated key matrix, and do the hill cipher encryption. The most practical hill cipher guide: block encryption with matrices mod 26, invertibility requirements, worked examples, encoding decoding workflow, and breaking via known plaintext and scoring. Tool to decrypt encrypt with hill cipher, a ciphering system similar to affine cipher but using a coefficient matrix instead of 2 affine coefficients (gradient). In the examples given, we shall walk through all the steps to use this cipher to act on digraphs and trigraphs. it can be extended further, but this then requires a much deeper knowledge of the background mathematics.
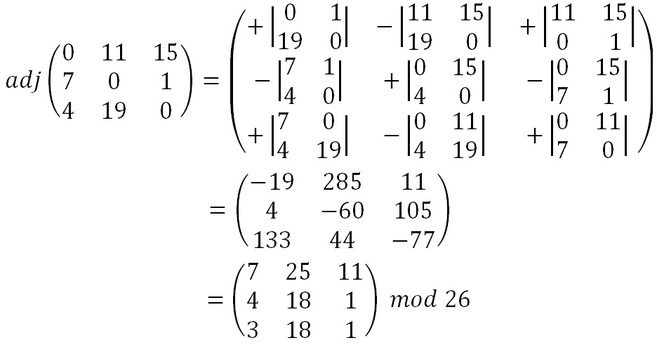
Github Ronaksharma11 Hill Cipher Decryption Tool to decrypt encrypt with hill cipher, a ciphering system similar to affine cipher but using a coefficient matrix instead of 2 affine coefficients (gradient). In the examples given, we shall walk through all the steps to use this cipher to act on digraphs and trigraphs. it can be extended further, but this then requires a much deeper knowledge of the background mathematics. Hill cipher algorithm | decryption | with example technistry lab 344 subscribers subscribe. The known ciphertext attack is the best one to try when trying to break the hill cipher, if no sections of the plaintext are known, guesses can be made. for the case of a 2 by 2 hill cipher, we could attack it by measuring the frequencies of all the digraphs that occur in the ciphertext. To decrypt the message, each block is multiplied by the inverse of the matrix used for encryption. the matrix used for encryption is the cipher key, and it should be chosen randomly from the set of invertible n × n matrices (modulo 26). To encrypt a message using the hill cipher we must first turn our keyword into a key matrix (a 2 × 2 matrix for working with digraphs, a 3 × 3 matrix for working with trigraphs, etc.).
Comments are closed.