Hill Cipher 1 Pdf

Hill Cipher Pdf 1 encryption 1.1 formula the general formula for encrypting text using the hill cipher algorithm is k × p mod 26. where k is our n × n matrix that serves as the key. the determinant of k must be relatively prime with 26. p is our text we want to encrypt in the form of an n × 1 matrix. Using a known plaintext attack, we can break the hill cipher with n blocks (of n letters) of matching plain ciphertext pairs. consider the following: let's say we know that "ma" encrypts to "ku" and that "th" encrypts to "mt".

Hill Cipher 1 Pdf Since the letter frequencies are masked the hill cipher is considerably more difficult to crack than a monoalphabetic substitution that is vulnerable to frequency analysis. Salah satu metode kriptografi yang memanfaatkan matriks adalah kriptografi hill cipher. hill cipher merupakan salah satu algoritma kriptografi kunci simetriks. algoritma hill cipher menggunakan matriks invertible berukuran n x n sebagai kunci untuk melakukan enkripsi dan dekripsi pada chipertext. The method which has been used to encode messages is called a hill substitution cipher. the method was invented by mathematician lester hill and is reviewed in references 1 and 2. this form of cipher is harder to decode than the simple substitution cipher. To encrypt a message using the hill cipher we must first turn our keyword into a key matrix (a 2 × 2 matrix for working with digraphs, a 3 × 3 matrix for working with trigraphs, etc.).

Hill Cipher Example Pdf Hill cipher 1 free download as pdf file (.pdf), text file (.txt) or view presentation slides online. hill ciphers, created by lester s. hill in 1929, are polygraphic substitution ciphers that utilize linear algebra and modular arithmetic for encryption and decryption. Hill ciphers (invented in 1929) are a type of block cipher: the ciphertext character that replaces a particular plaintext character in the encryption will depend on the neighboring plaintext characters. To use the key to transform plaintext into ciphertext is to encipher the plaintext. to use the inverse key to transform the ciphertext back into plaintext is to decipher the ciphertext. To produce cipher text, the method used is to carry out an encryption process based on the hill cipher algorithm. the encryption process is carried out by multiplying the key matrix by the plaintext.
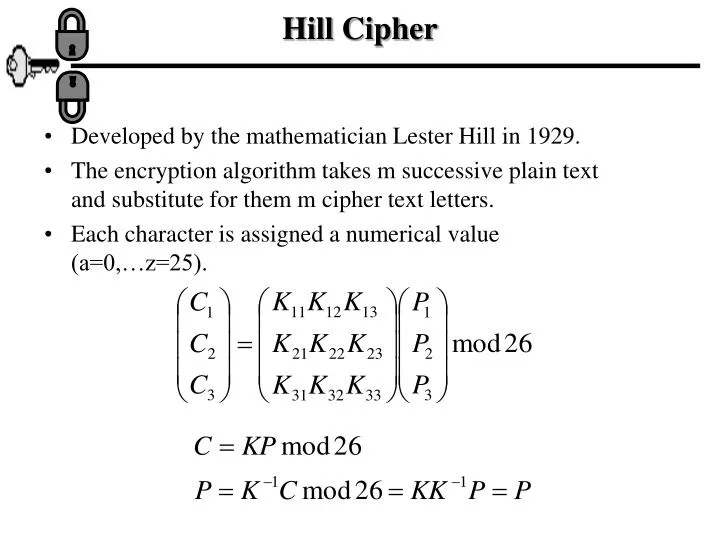
Ppt Hill Cipher Powerpoint Presentation Free Download Id 548808 To use the key to transform plaintext into ciphertext is to encipher the plaintext. to use the inverse key to transform the ciphertext back into plaintext is to decipher the ciphertext. To produce cipher text, the method used is to carry out an encryption process based on the hill cipher algorithm. the encryption process is carried out by multiplying the key matrix by the plaintext.
Comments are closed.