Hijacking Aws Hosted Github Runners

Best Practices Working With Self Hosted Github Action Runners At Scale Hijacking aws – hosted github runners if you're running self hosted github actions runners on aws ec2, there's a critical timing vulnerability you need to know about. Aws compromise through self hosted github runners: a detailed guide on how attackers can exploit third party github actions to compromise aws environments. preventive measures: steps to secure your github workflows and aws environment from similar attacks.
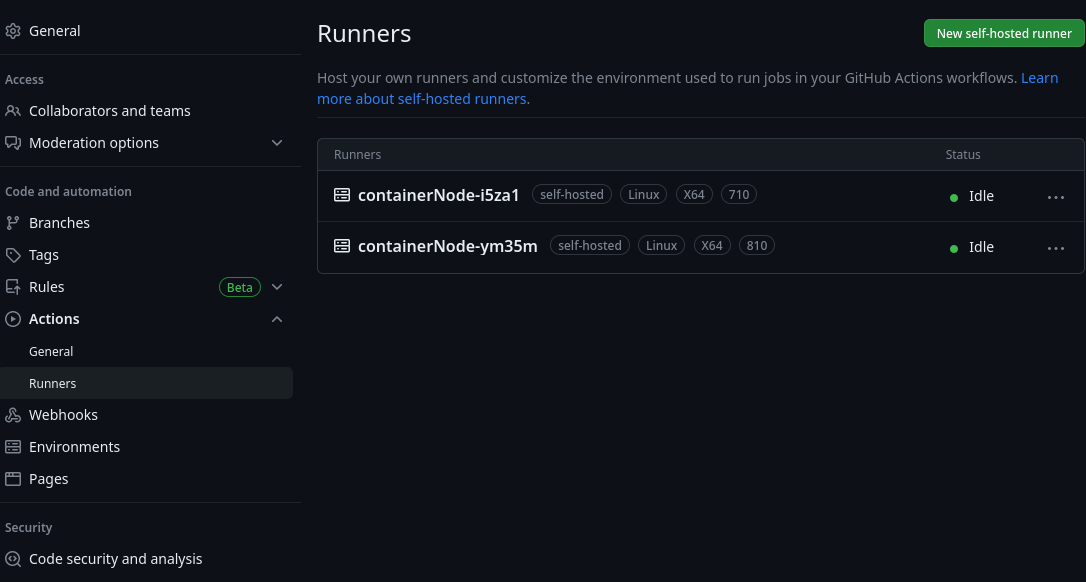
Best Practices Working With Self Hosted Github Action Runners At Scale In a recent engagement we managed to compromise a github app allowed to register self hosted runners at the organization level. turns out, it is possible to register a github runner with the ubuntu latest tag, granting access to jobs originally designated for github provisioned runners. In this blog, i explore security, performance and cost best practices to take into consideration when deploying github self hosted runners to your aws environment. These sections consider some of the steps an attacker can take if they're able to run malicious commands on a github actions runner. github hosted runners do not scan for malicious code downloaded by a user during their job, such as a compromised third party library. Using the shai hulud campaign as a case study, let’s explore how attackers can abuse github's self hosted runner infrastructure to establish persistent remote access. we will also examine the attack mechanics, detection strategies, and monitoring recommendations for security teams.

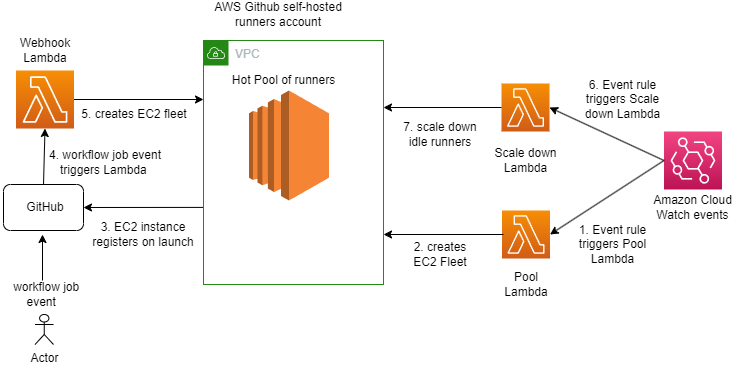
Best Practices Working With Self Hosted Github Action Runners At Scale These sections consider some of the steps an attacker can take if they're able to run malicious commands on a github actions runner. github hosted runners do not scan for malicious code downloaded by a user during their job, such as a compromised third party library. Using the shai hulud campaign as a case study, let’s explore how attackers can abuse github's self hosted runner infrastructure to establish persistent remote access. we will also examine the attack mechanics, detection strategies, and monitoring recommendations for security teams. White hat hackers at wiz performing red team adversarial simulations against aws codebuild ci cd pipelines have discovered a critical vulnerability—specifically, unanchored regex patterns in. In a recent engagement we managed to compromise a github app allowed to register self hosted runners at the organization level. turns out, it is possible to register a github runner with the ubuntu latest tag, granting access to jobs originally designated for github provisioned runners. This terraform module creates the required infrastructure needed to host github actions self hosted, auto scaling runners on aws spot instances. it provides the required logic to handle the life cycle for scaling up and down using a set of aws lambda functions. In this post, we will walk through steps to create a malicious github workflow and explore a method on how to use them to pivot into your aws environment. after that, what you do with that, is.
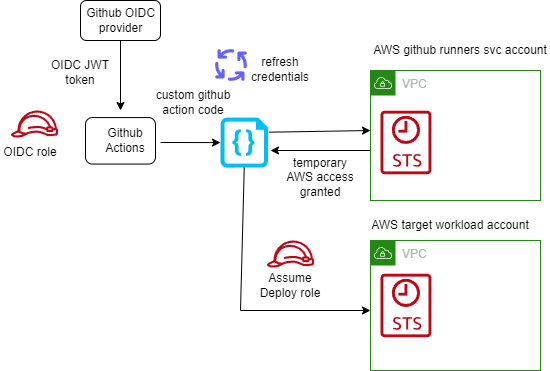
Best Practices Working With Self Hosted Github Action Runners At Scale White hat hackers at wiz performing red team adversarial simulations against aws codebuild ci cd pipelines have discovered a critical vulnerability—specifically, unanchored regex patterns in. In a recent engagement we managed to compromise a github app allowed to register self hosted runners at the organization level. turns out, it is possible to register a github runner with the ubuntu latest tag, granting access to jobs originally designated for github provisioned runners. This terraform module creates the required infrastructure needed to host github actions self hosted, auto scaling runners on aws spot instances. it provides the required logic to handle the life cycle for scaling up and down using a set of aws lambda functions. In this post, we will walk through steps to create a malicious github workflow and explore a method on how to use them to pivot into your aws environment. after that, what you do with that, is.
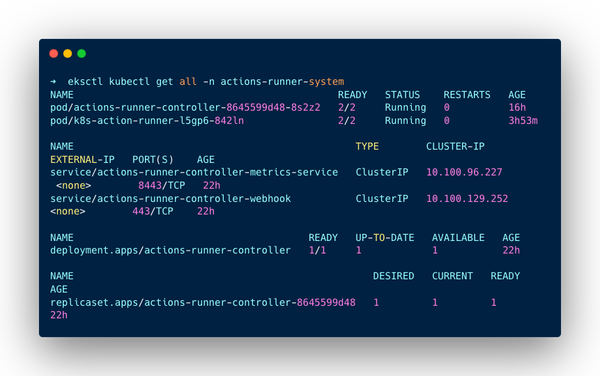
How To Setup Github Actions Runner On Aws Eks Cluster Self Hosted This terraform module creates the required infrastructure needed to host github actions self hosted, auto scaling runners on aws spot instances. it provides the required logic to handle the life cycle for scaling up and down using a set of aws lambda functions. In this post, we will walk through steps to create a malicious github workflow and explore a method on how to use them to pivot into your aws environment. after that, what you do with that, is.
End To End Testing With Self Hosted Runners In Github Actions Red Hat
Comments are closed.