High Level Architecture Vulnerability Lookup
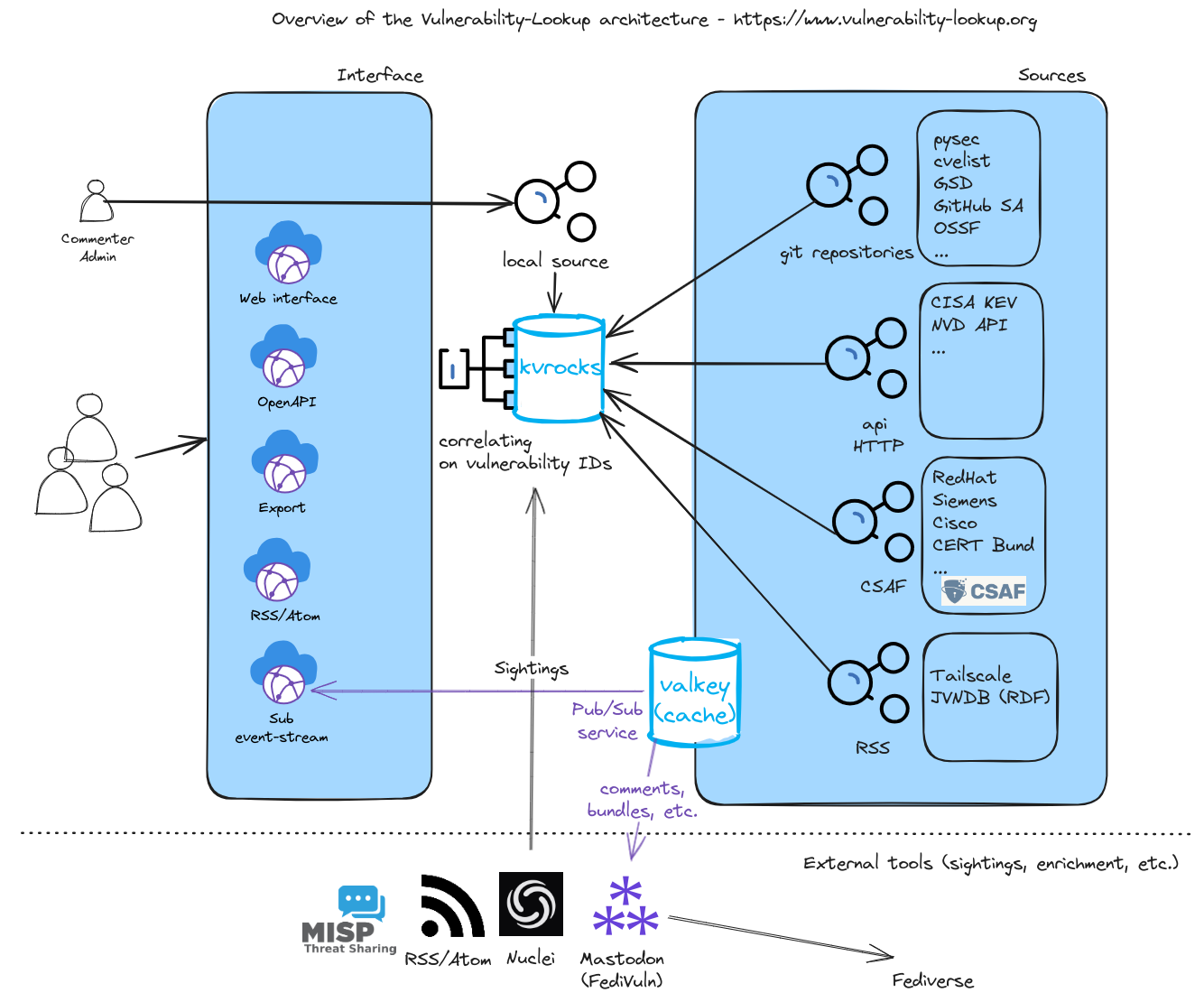
High Level Architecture Vulnerability Lookup It is possible to extend vulnerability lookup functionalities thanks to its api and various tools. for example to facilitate the provision of sightings. High level architecture # fig. 2 high level architecture # previous command line interface next.
High Level Architecture Vulnerability Lookup Identify, define, and catalog publicly disclosed cybersecurity vulnerabilities. there are currently over 321,000 cve records accessible via download or keyword search above. the cve program partners with community members worldwide to grow cve content and expand its usage. This document describes the overall architecture of the vulnerability lookup system, including its key components, data flow, and integration points. it provides a technical overview of how the system is structured and how its various components interact. Interface # tools # it is possible to extend vulnerability lookup functionalities thanks to its api and various tools. for example to facilitate the provision of sightings. previous command line interface next. Cve find is a cybersecurity intelligence platform indexing cves, cwes, capec, cvss, epss and threat data. search, track, and analyze known vulnerabilities and exploit risks.

Vulnerability Lookup Interface # tools # it is possible to extend vulnerability lookup functionalities thanks to its api and various tools. for example to facilitate the provision of sightings. previous command line interface next. Cve find is a cybersecurity intelligence platform indexing cves, cwes, capec, cvss, epss and threat data. search, track, and analyze known vulnerabilities and exploit risks. Site privacy | accessibility | privacy program | copyrights | vulnerability disclosure | no fear act policy | foia | environmental policy | scientific integrity | information quality standards | commerce.gov | science.gov | usa.gov. This list provides a starting point on where security practitioners can search for vulnerability data pertinent to the systems and software relevant to their organization. The vulners rest api offers reliable, high performance access to vulnerability intelligence, with 99.9% sla uptime and cdn backed data delivery for seamless global access. You can view cve vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time.
Comments are closed.