Hashing Hash Codes

What Is Hashing And Hash Table Python Programs Try various hashing functions, discover hash database, and decode unhash hash digest via reverse lookup. Hash functions are used in conjunction with hash tables to store and retrieve data items or data records. the hash function translates the key associated with each datum or record into a hash code, which is used to index the hash table.

Hashing And Its Use Cases In Java Scaler Topics Tool for hashing, cracking and decoding hash fingerprints (md5, sha1, sha256, etc.). decoding by brute force or dictionary. Hashing is a technique used in data structures that efficiently stores and retrieves data in a way that allows for quick access. hashing involves mapping data to a specific index in a hash table (an array of items) using a hash function. it enables fast retrieval of information based on its key. Hashing means using some function or algorithm to map object data to some representative integer value. this so called hash code (or simply hash) can then be used as a way to narrow down our search when looking for the item in the map. Learn how cryptographic hash functions work, from md5 to sha 256 and sha 512. covers the avalanche effect, collision attacks, password hashing with bcrypt argon2, hmac authentication, and real world applications in blockchain, tls, and git.
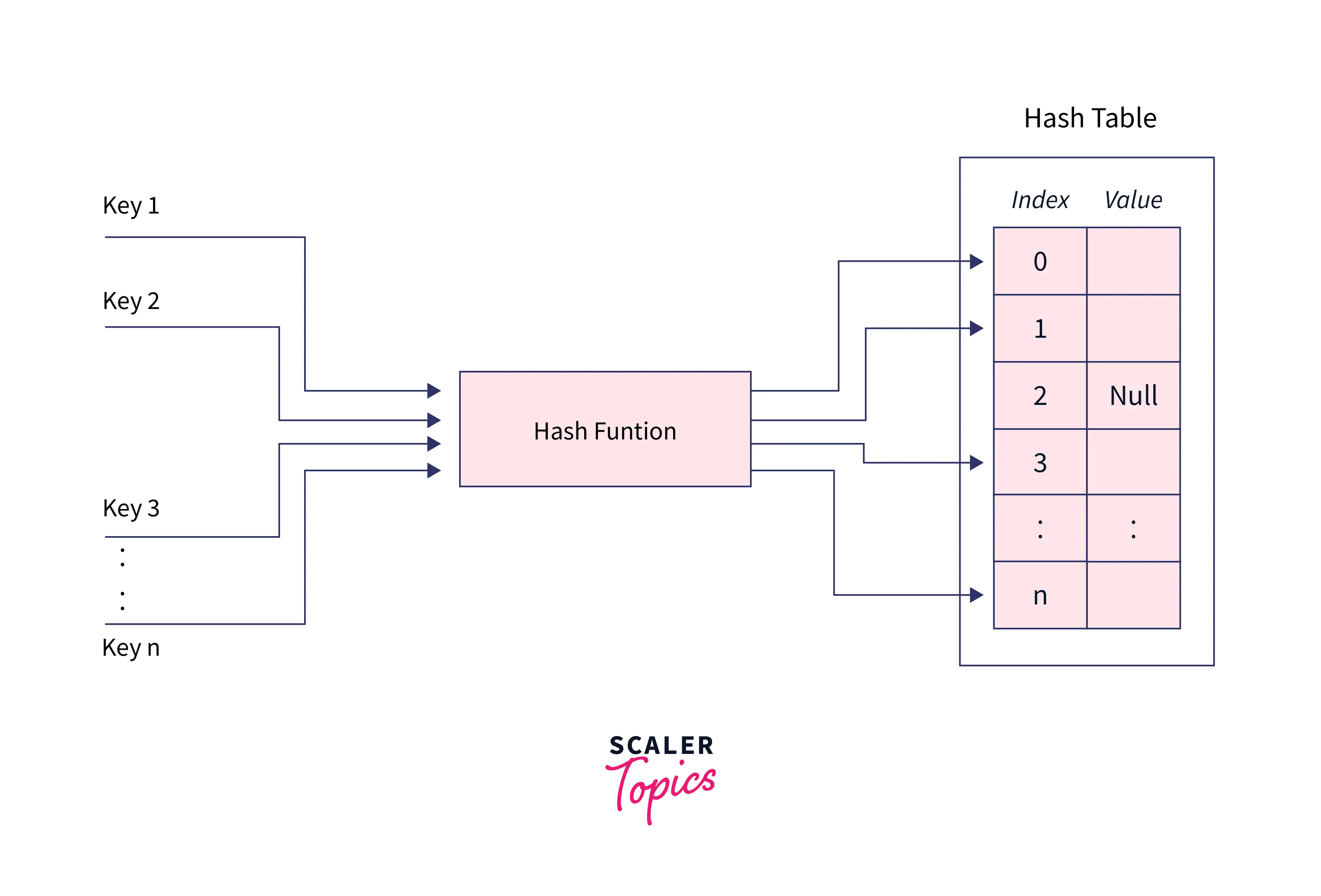
Hashing And Its Use Cases In Java Scaler Topics Hashing means using some function or algorithm to map object data to some representative integer value. this so called hash code (or simply hash) can then be used as a way to narrow down our search when looking for the item in the map. Learn how cryptographic hash functions work, from md5 to sha 256 and sha 512. covers the avalanche effect, collision attacks, password hashing with bcrypt argon2, hmac authentication, and real world applications in blockchain, tls, and git. Hashing refers to the technique of mapping arbitrary keys or data to fixed size integer values called hash codes. a hash function accepts the key and outputs this representative hash code. these hash codes are then used as indices to store and access data in a hash table efficiently. The sha 2 family of hash functions was originally developed by the us national security agency (nsa) and is the standard for hashing private data. it’s currently used by cryptocurrencies and the cia. Learn what hashing in cryptography is, how it works, key algorithms like sha 256, real world uses, and best practices to keep your data secure. Hash generator generate md5, sha 1, sha 256, sha 384, and sha 512 hashes from text or files. compare hashes to verify file integrity.
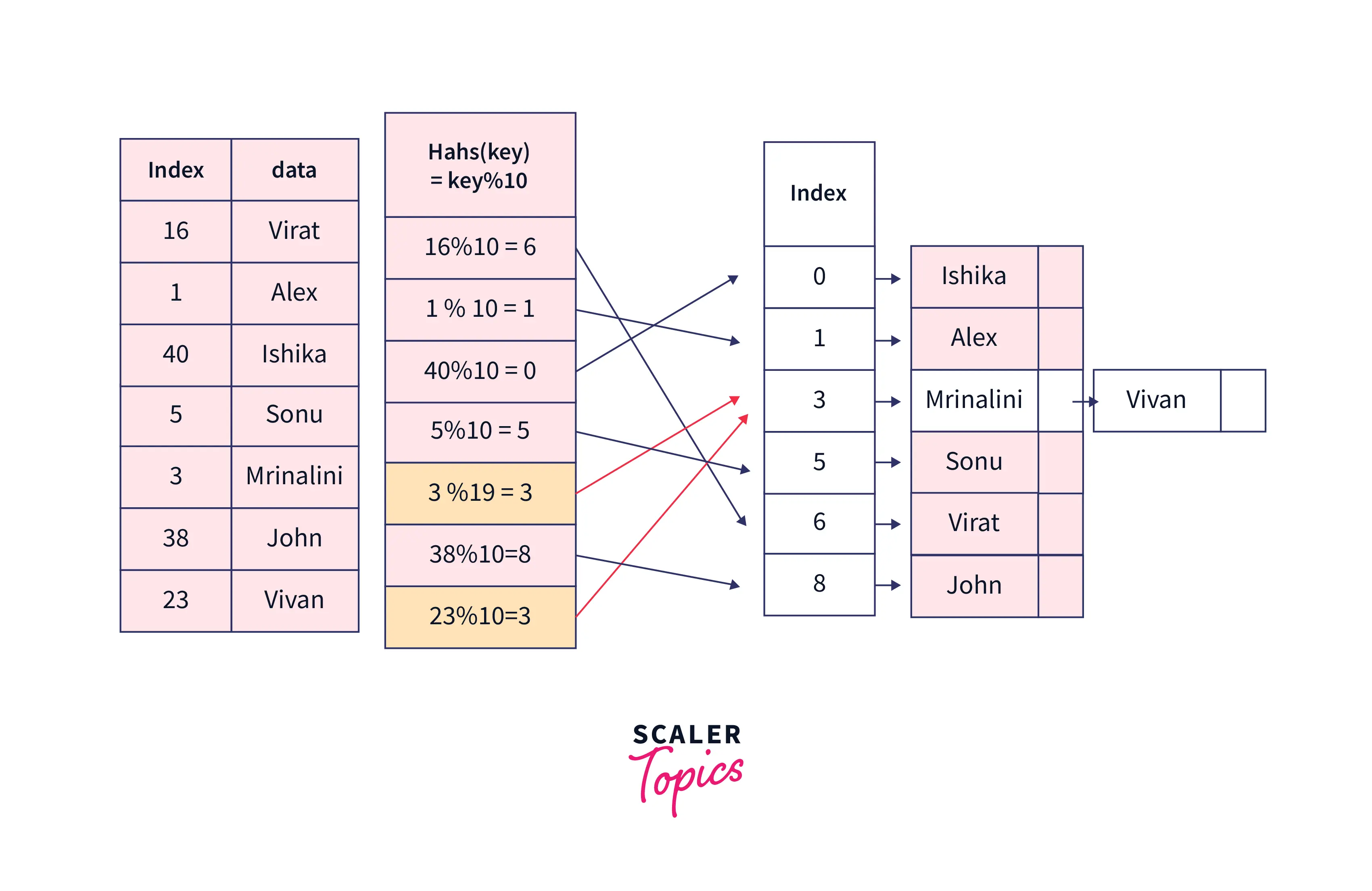
Hashing And Its Use Cases In Java Scaler Topics Hashing refers to the technique of mapping arbitrary keys or data to fixed size integer values called hash codes. a hash function accepts the key and outputs this representative hash code. these hash codes are then used as indices to store and access data in a hash table efficiently. The sha 2 family of hash functions was originally developed by the us national security agency (nsa) and is the standard for hashing private data. it’s currently used by cryptocurrencies and the cia. Learn what hashing in cryptography is, how it works, key algorithms like sha 256, real world uses, and best practices to keep your data secure. Hash generator generate md5, sha 1, sha 256, sha 384, and sha 512 hashes from text or files. compare hashes to verify file integrity.
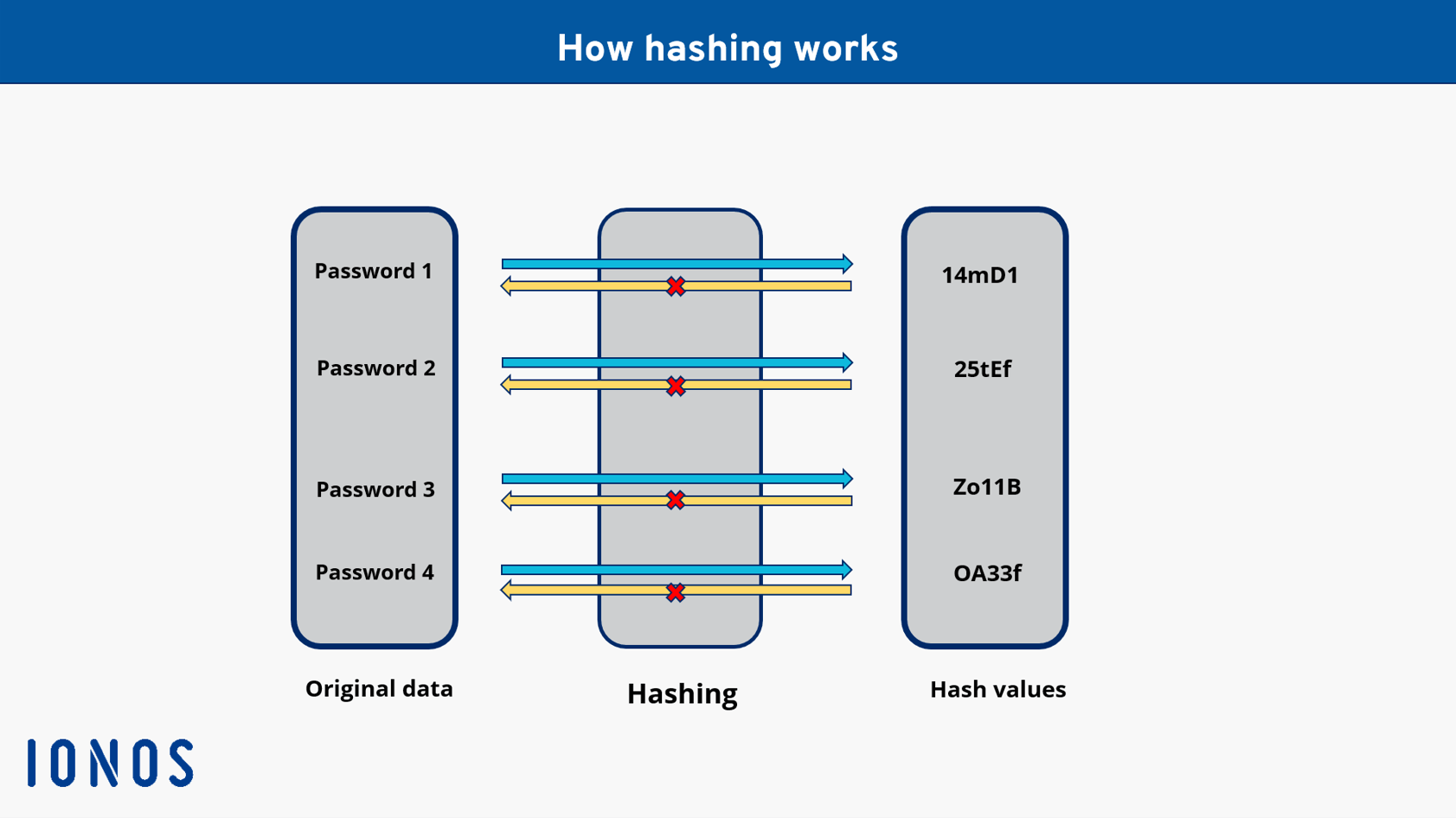
What Is Hashing And How Does It Work Ionos Uk Learn what hashing in cryptography is, how it works, key algorithms like sha 256, real world uses, and best practices to keep your data secure. Hash generator generate md5, sha 1, sha 256, sha 384, and sha 512 hashes from text or files. compare hashes to verify file integrity.
Comments are closed.