Hashing
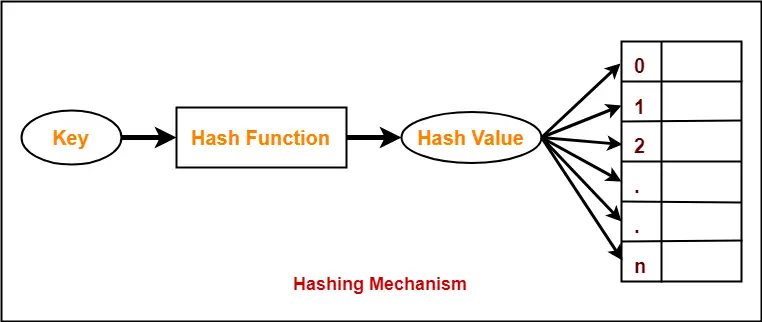
Hashing In Data Structure Hash Functions Gate Vidyalay Hashing is the process of converting data — text, numbers, files, or anything, really — into a fixed length string of letters and numbers. data is converted into these fixed length strings, or hash values, by using a special algorithm called a hash function. Hashing adalah salah satu konsep penting dalam dunia teknologi informasi, khususnya dalam menjaga keamanan data. dengan teknik ini, informasi diubah menjadi kode unik yang sulit dibalikkan ke bentuk aslinya.
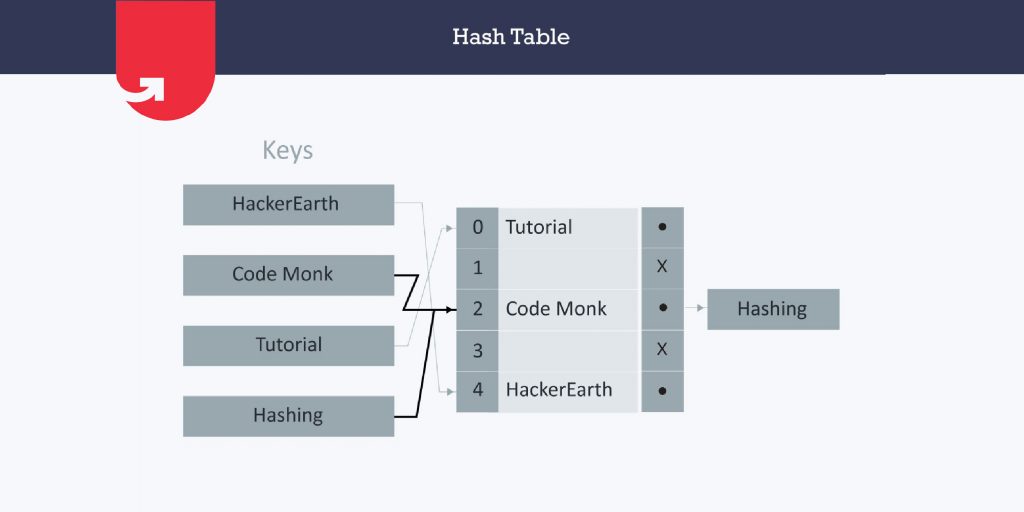
Hashing In Data Structure Function Techniques With Examples Hashing is a technique used in data structures that efficiently stores and retrieves data in a way that allows for quick access. hashing involves mapping data to a specific index in a hash table (an array of items) using a hash function. it enables fast retrieval of information based on its key. Hashing is a one way mathematical function that turns data into a string of nondescript text that cannot be reversed or decoded. in the context of cybersecurity, hashing is a way to keep sensitive information and data — including passwords, messages, and documents — secure. Hashing is a way to access data quickly and efficiently. unlike lists or trees, it provides near constant access time. it also uses much less storage than trying to store all possible keys directly, especially when keys are large or variable in length. Learn what hashing in cryptography is, how it works, key algorithms like sha 256, real world uses, and best practices to keep your data secure.
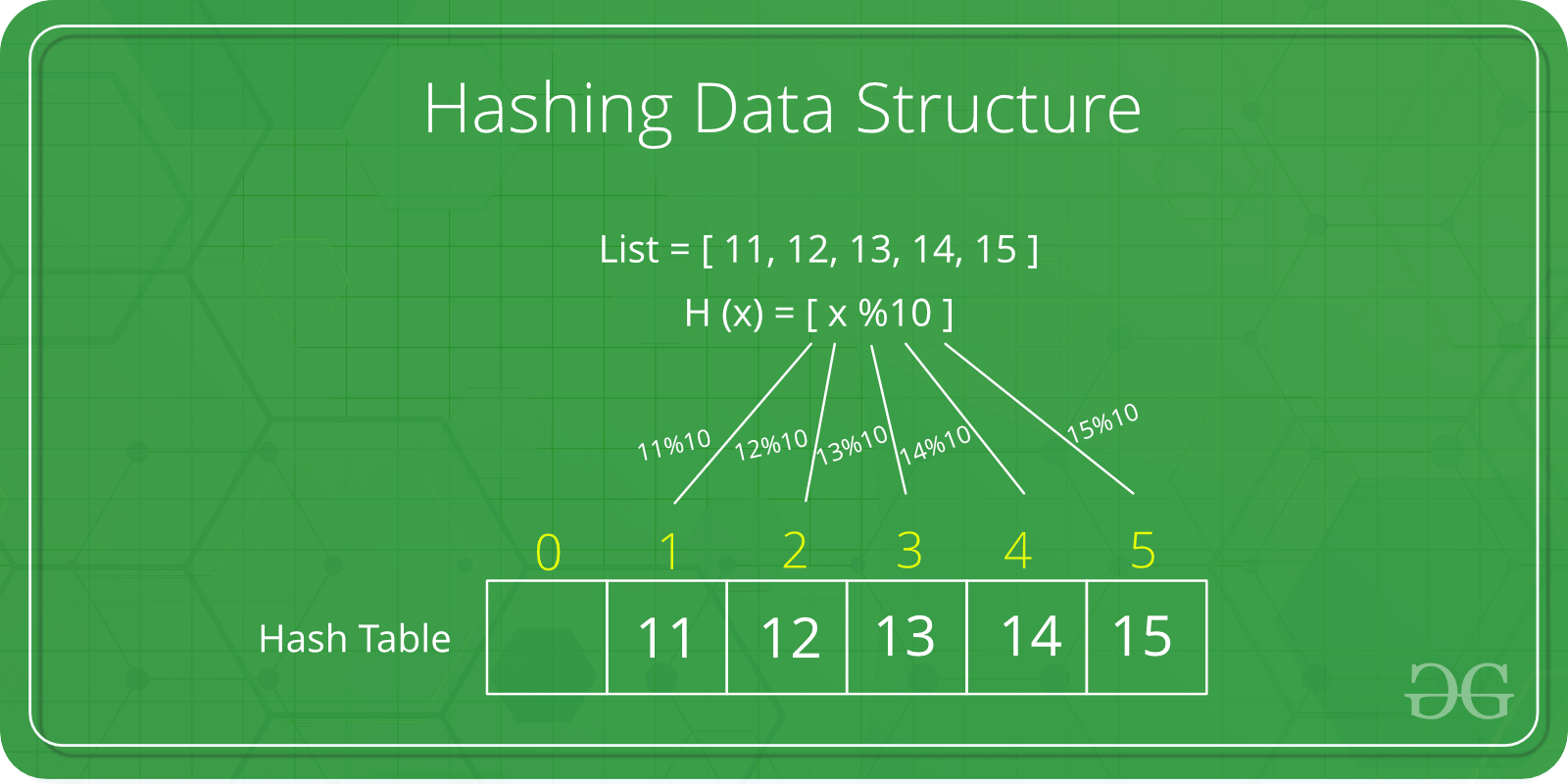
Hashing Hash Table Hash Functions And Collision Resolution Find Hashing is a way to access data quickly and efficiently. unlike lists or trees, it provides near constant access time. it also uses much less storage than trying to store all possible keys directly, especially when keys are large or variable in length. Learn what hashing in cryptography is, how it works, key algorithms like sha 256, real world uses, and best practices to keep your data secure. Find out what hashing is used for, how it works to transform keys and characters, and how it relates to data structure, cybersecurity and cryptography. Hashing is the process of transforming any given key or a string of characters into another value. this is usually represented by a shorter, fixed length value or key that represents and makes it easier to find or employ the original string. Discover what hashing is, how it works, and why it is the pillar of modern web security. includes interactive real time sha 256 examples. In cybersecurity, hashing is the process of converting input data like a file, document or password into a string of indecipherable characters. the process is one way and acts as a digital fingerprint, allowing users to track and verify data.
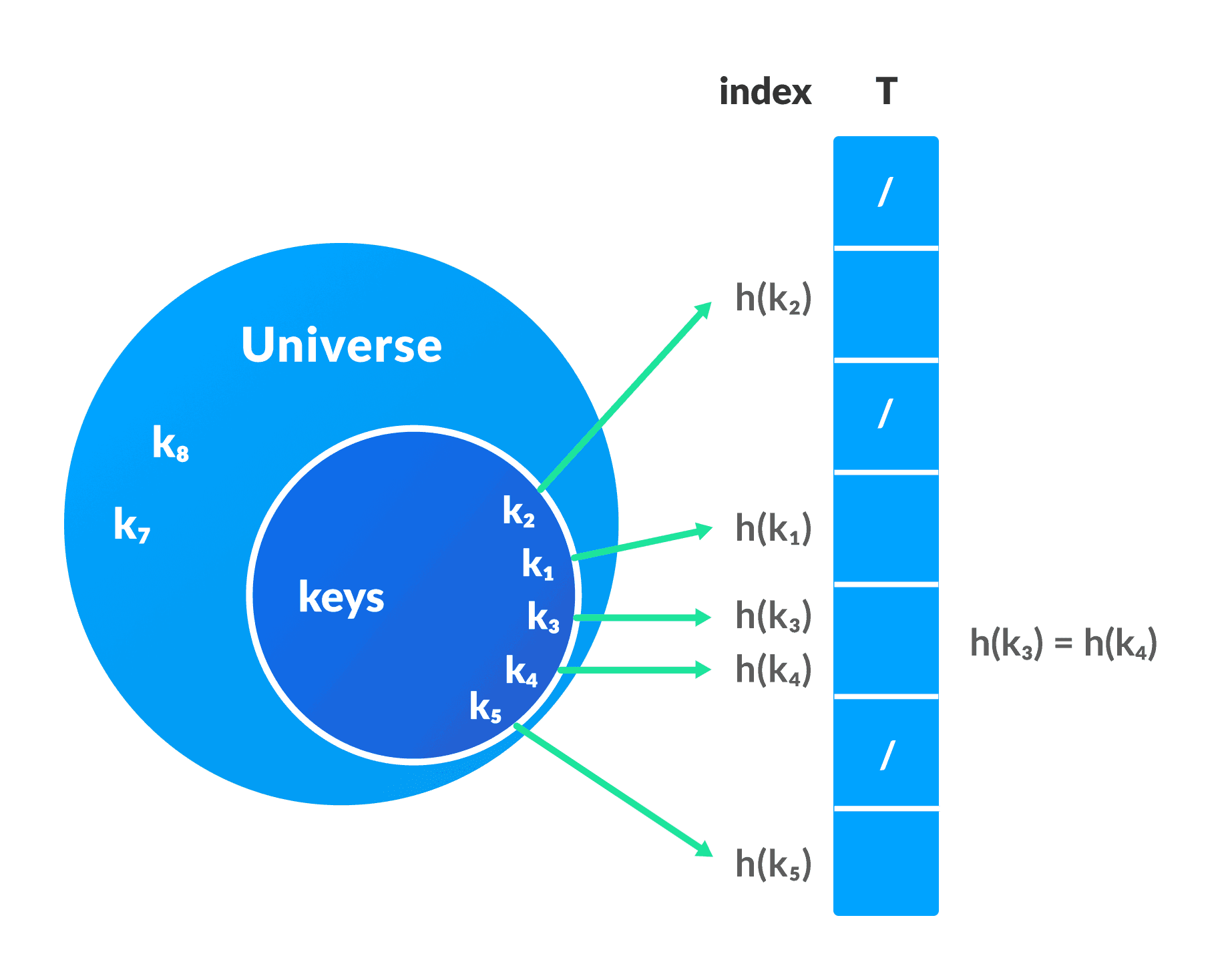
Hash Table Data Structure Find out what hashing is used for, how it works to transform keys and characters, and how it relates to data structure, cybersecurity and cryptography. Hashing is the process of transforming any given key or a string of characters into another value. this is usually represented by a shorter, fixed length value or key that represents and makes it easier to find or employ the original string. Discover what hashing is, how it works, and why it is the pillar of modern web security. includes interactive real time sha 256 examples. In cybersecurity, hashing is the process of converting input data like a file, document or password into a string of indecipherable characters. the process is one way and acts as a digital fingerprint, allowing users to track and verify data.

Data Structures In Javascript Scaler Topics Discover what hashing is, how it works, and why it is the pillar of modern web security. includes interactive real time sha 256 examples. In cybersecurity, hashing is the process of converting input data like a file, document or password into a string of indecipherable characters. the process is one way and acts as a digital fingerprint, allowing users to track and verify data.
Comments are closed.