Hardware Vulnerability Assessment Process Model

Premium Ai Image Vulnerability Assessment Process In this comprehensive guide, we’ll explore vulnerability assessment methodology, the different types of vulnerability assessments, the best tools available, and best practices for conducting these assessments. To address this challenge, we propose a framework that provides systematic categorization of threat models, and describes a security metric formulation which can be used to evaluate vulnerability of microarchitectural components, as well as the system as a whole.
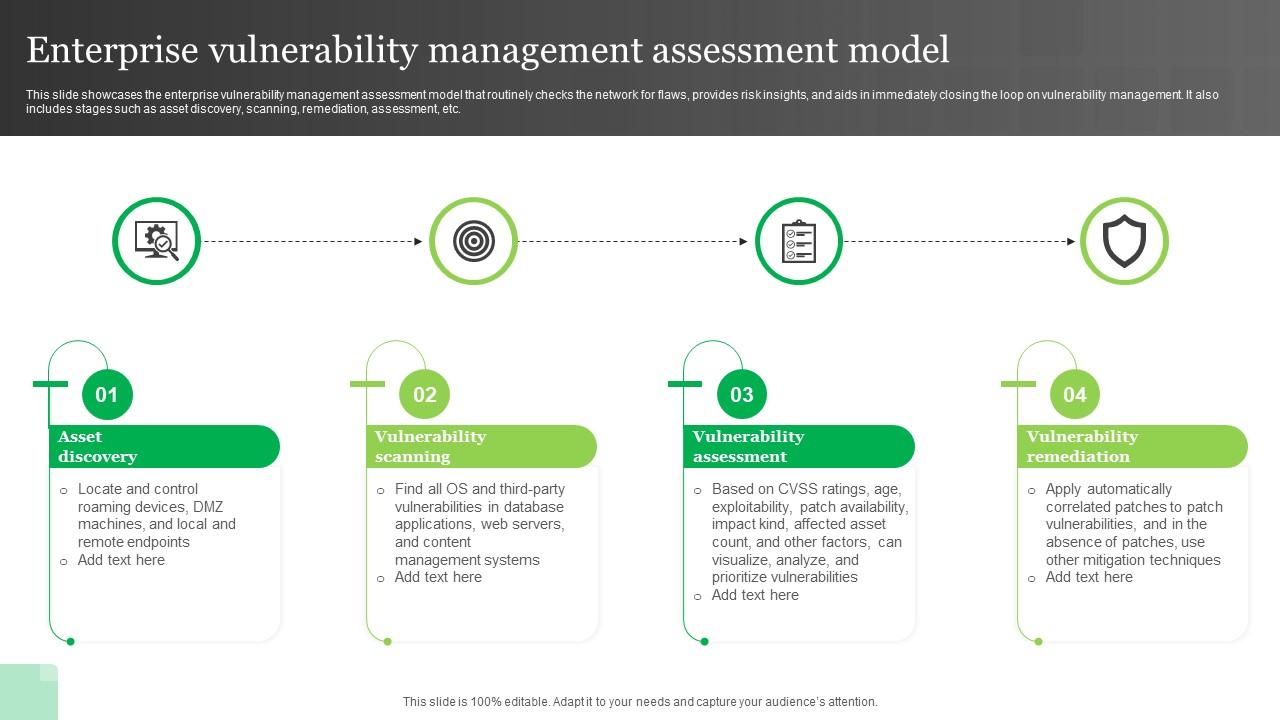
Enterprise Vulnerability Management Assessment Model Ppt Template Learn what vulnerability assessments are, why they matter, and how they align with it risk and vulnerability management. explore the step by step process, best practices, and how manageengine vulnerability manager plus helps secure your it environment. The vulnerability assessment process is a systematic approach to identifying, analyzing, and addressing security vulnerabilities within an organization’s it infrastructure. Microsoft defender vulnerability management hardware and firmware assessment provides a list of known hardware and firmware in your organization. it provides individual inventories for system models, processors, and bios. Discover how vulnerability assessments assist in identifying risks, the keys steps, and the benefits of a proactive security approach.

Vulnerability Assessment Services Ai Cyber Experts Microsoft defender vulnerability management hardware and firmware assessment provides a list of known hardware and firmware in your organization. it provides individual inventories for system models, processors, and bios. Discover how vulnerability assessments assist in identifying risks, the keys steps, and the benefits of a proactive security approach. Master vulnerability assessments with proven techniques, tools, and prioritization methods that cut real risk and close exposure fast. Learn about different vulnerability assessment types & methodologies to protect your organization from security risks and breaches. The process of finding vulnerabilities and risks in computer networks, systems, hardware, applications, and other aspects of the it ecosystem is known as vulnerability assessment. A vulnerability assessment systematically identifies, evaluates, and addresses security weaknesses within a system. this guide provides a detailed walkthrough of the vulnerability assessment process, from initial planning to remediation.
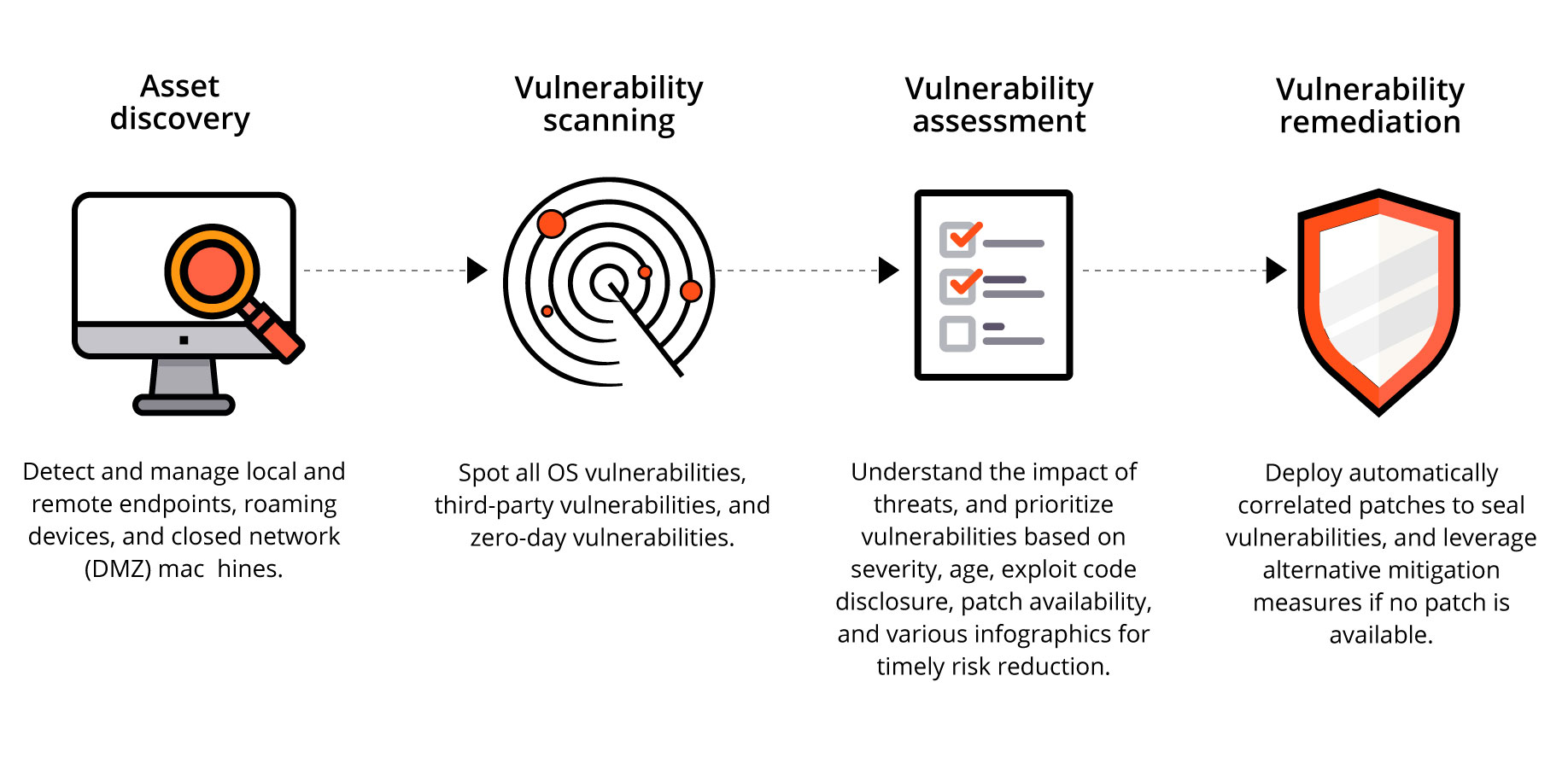
Vulnerability Assessment Websec Services Master vulnerability assessments with proven techniques, tools, and prioritization methods that cut real risk and close exposure fast. Learn about different vulnerability assessment types & methodologies to protect your organization from security risks and breaches. The process of finding vulnerabilities and risks in computer networks, systems, hardware, applications, and other aspects of the it ecosystem is known as vulnerability assessment. A vulnerability assessment systematically identifies, evaluates, and addresses security weaknesses within a system. this guide provides a detailed walkthrough of the vulnerability assessment process, from initial planning to remediation.

Sprocket Security Vulnerability Assessment Process And 5 Critical The process of finding vulnerabilities and risks in computer networks, systems, hardware, applications, and other aspects of the it ecosystem is known as vulnerability assessment. A vulnerability assessment systematically identifies, evaluates, and addresses security weaknesses within a system. this guide provides a detailed walkthrough of the vulnerability assessment process, from initial planning to remediation.
Steps Involved In Vulnerability Assessment Process
Comments are closed.