Hardware Hacking Lifting Firmware
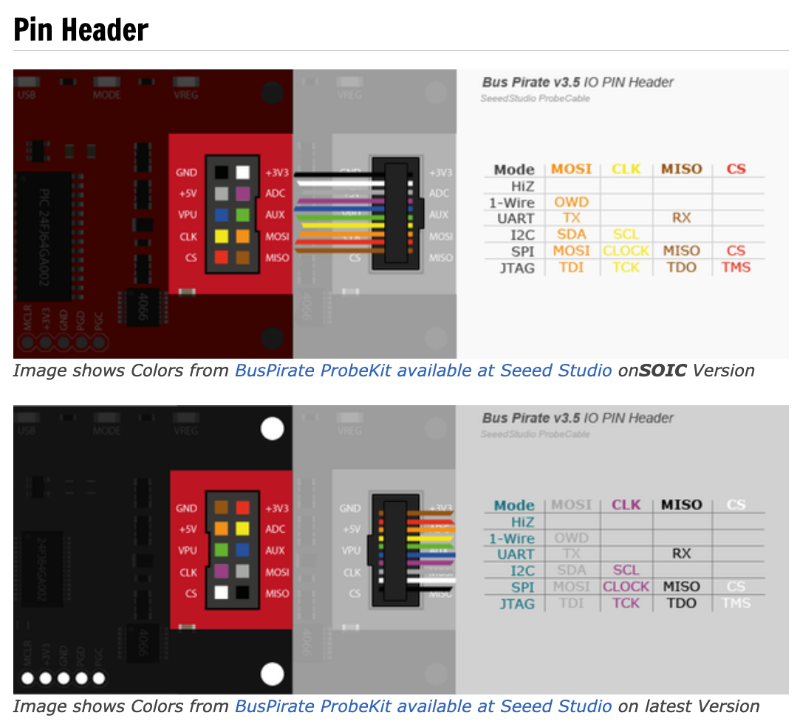
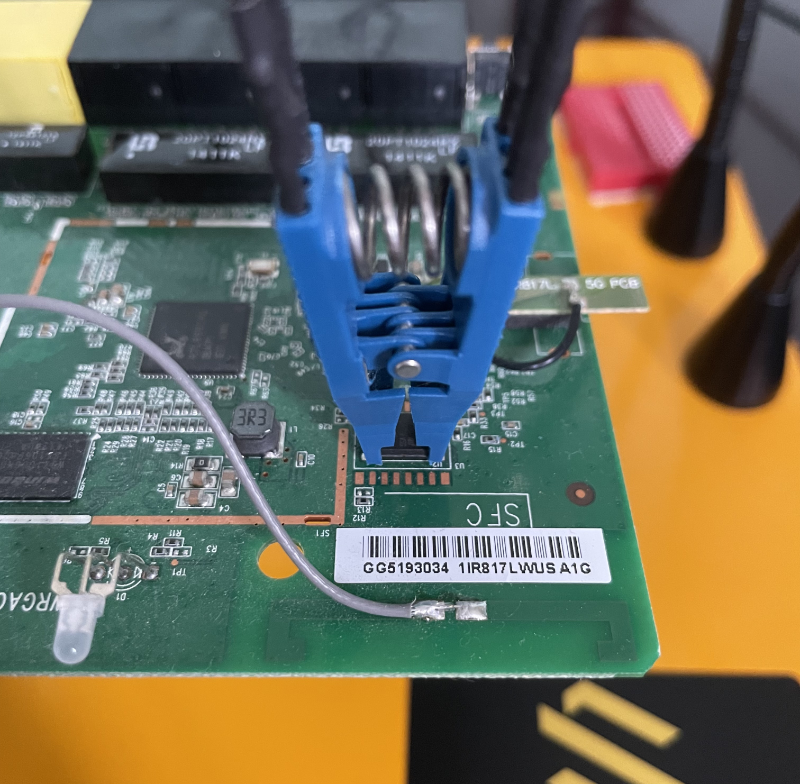
Hardware Hacking Lifting Firmware We have demonstrated the tools required to lift firmware using a pomona soic test clip, the bus pirate, and a few open source tools. this was in contrast to accessing firmware using common techniques, such as interfacing with uart or jtag. Obtaining the firmware from devices can be done in several different ways. depending on the target device, firmware can be extracted through physical, semi physical, or software only methods. this page covers both invasive and non invasive approaches.
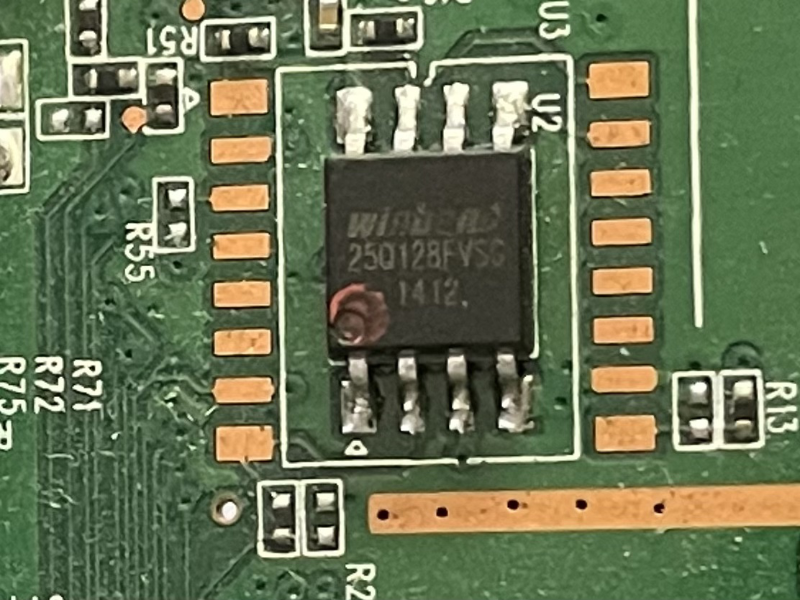
Hardware Hacking Lifting Firmware You'll get familiar with testing voltages, identifying data lines, and sometimes even dumping firmware to examine its contents. i recommend reading the following pages on how to approach your first hardware hacking journey:. The rapid growth in popularity of hardware platforms like the esp32 has democratized security research but has also introduced critical risks. security researchers and threat actors may be using the same tools, which could lead to the targeting of firmware based devices of all types. In a previous tutorial, we’ve talked about how embedded devices can have vulnerabilities inside, and one way to detect them, and to protect yourself from them, is to check them out by yourself. this will be focusing on the same idea, just without dumping the firmware yourself. With the introduction of more and more iot and embedded devices in the market, hackers are starting to find firmware exploitation as a more viable mechanism for gaining access into networks and taking over machines.
Hardware Hacking Lifting Firmware In a previous tutorial, we’ve talked about how embedded devices can have vulnerabilities inside, and one way to detect them, and to protect yourself from them, is to check them out by yourself. this will be focusing on the same idea, just without dumping the firmware yourself. With the introduction of more and more iot and embedded devices in the market, hackers are starting to find firmware exploitation as a more viable mechanism for gaining access into networks and taking over machines. In part three of our “getting started with iot and hardware hacking” series we will perform firmware analysis to hunt for vulnerabilities in custom firmware we loaded onto a raspberry pi. Learn how to get started with hardware hacking, from essential tools and uart jtag debugging to firmware extraction and real world pentesting techniques. explore hands on commands and expert tips. Firmware hacking refers to the practice of modifying the software that controls the hardware of an electronic device, such as a computer or a smartphone. this can be done for various reasons, including gaining unauthorized access, disabling security measures, or installing malicious software. We’ll focus on the essential steps from planning and reconnaissance to networking protocol, hardware, and firmware analysis, providing you with a high level overview of how to assess physical devices and their associated applications.

Hardware Hacking Lifting Firmware In part three of our “getting started with iot and hardware hacking” series we will perform firmware analysis to hunt for vulnerabilities in custom firmware we loaded onto a raspberry pi. Learn how to get started with hardware hacking, from essential tools and uart jtag debugging to firmware extraction and real world pentesting techniques. explore hands on commands and expert tips. Firmware hacking refers to the practice of modifying the software that controls the hardware of an electronic device, such as a computer or a smartphone. this can be done for various reasons, including gaining unauthorized access, disabling security measures, or installing malicious software. We’ll focus on the essential steps from planning and reconnaissance to networking protocol, hardware, and firmware analysis, providing you with a high level overview of how to assess physical devices and their associated applications.
Comments are closed.