Hard Coded Credential Scanner Demonstration
Github Osashimiman Hardcoded Credential Hard coded credential scanner demonstration bruno caseiro 9 subscribers subscribe. Hard coded credentials are authentication data such as passwords, api keys, authorization tokens, or private keys which have been embedded directly into the source code or static configuration files rather than obtaining them from an external source or injecting them upon deployment runtime.
Github Cowsecurity Docker Credential Scanner It Is A Simple Script Take a test drive today to see bigid in action or book a 1:1 demo with our experts. hardcoded secrets expose credentials and sensitive access keys. learn how bigid detects secrets in code and reduces risk across repositories and pipelines. Leaked credentials are one of the fastest paths to a breach. this guide compares the 18 best secrets detection tools for 2026 that help security teams find exposed api keys, database credentials, and hardcoded secrets before attackers do. Hence, we assess llms to represent these observations and feed extracted embedding vectors to a deep learning classifier to detect hard coded credentials. our model outperforms the current state of the art by 13% in f1 measure on the benchmark dataset. You can use flawnter to proactively scan for hard coded secrets and reduce the exposure to potential security breaches and enhance your application overall security posture.
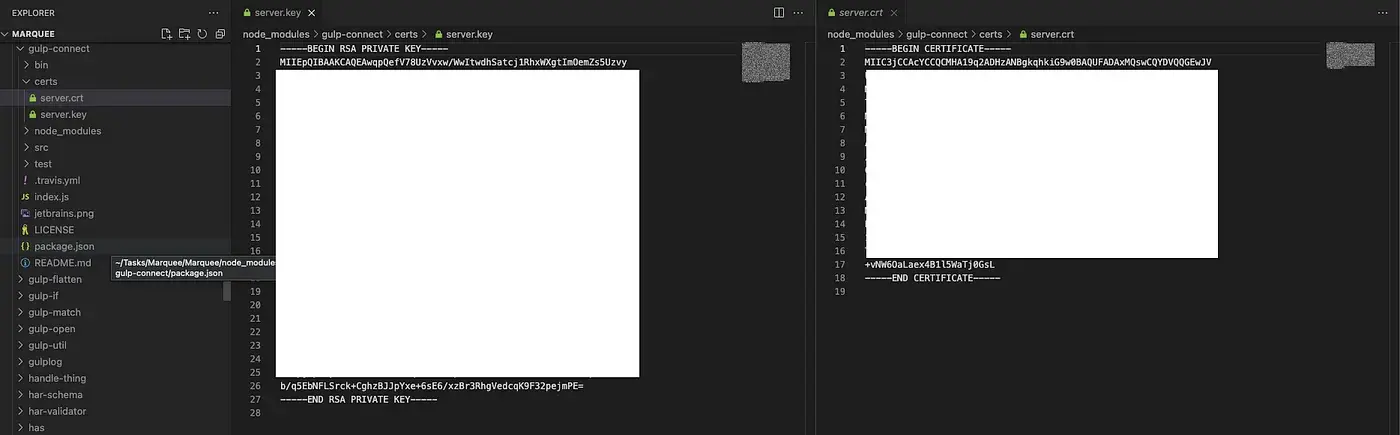
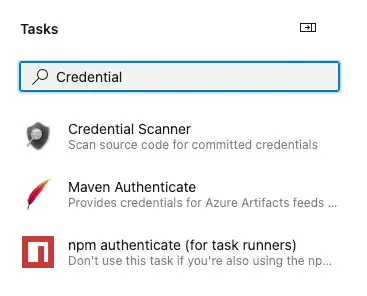
Blog Scan Code With Credential Scanner On Azure Devops Mycos Hence, we assess llms to represent these observations and feed extracted embedding vectors to a deep learning classifier to detect hard coded credentials. our model outperforms the current state of the art by 13% in f1 measure on the benchmark dataset. You can use flawnter to proactively scan for hard coded secrets and reduce the exposure to potential security breaches and enhance your application overall security posture. Once you’ve decided on either a tiered approach or a subset of applications to scan, you can use different static code analysis tools or qualitative discovery methods to find the hard coded application credentials. Credential digger is a github scanning tool that identifies hardcoded credentials (passwords, api keys, secret keys, tokens, personal information, etc), filtering the false positive data through machine learning models. For users who wish to see all available information for the cwe capec entry. for users who want to customize what details are displayed. the product contains hard coded credentials, such as a password or cryptographic key. This guide explains what hardcoded credentials are, why sast scanners flag them, how to interpret and fix the checkmarx cwe 798 finding, and the correct remediation patterns for the most common languages.
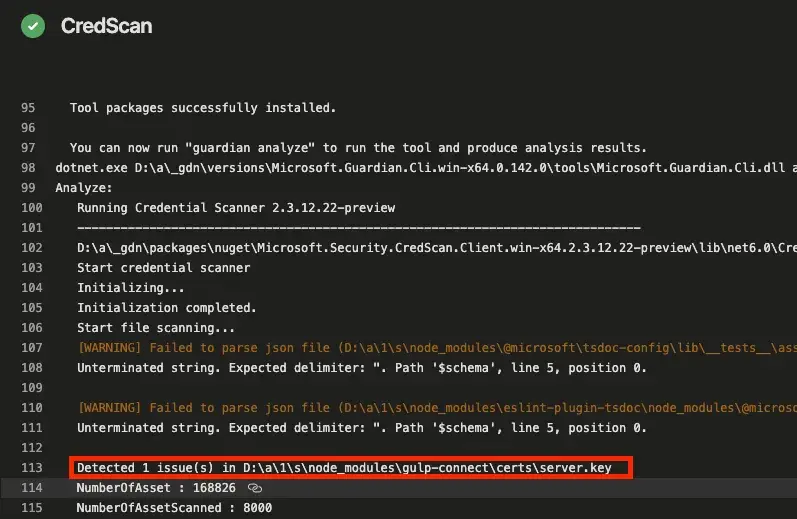
Blog Scan Code With Credential Scanner On Azure Devops Mycos Once you’ve decided on either a tiered approach or a subset of applications to scan, you can use different static code analysis tools or qualitative discovery methods to find the hard coded application credentials. Credential digger is a github scanning tool that identifies hardcoded credentials (passwords, api keys, secret keys, tokens, personal information, etc), filtering the false positive data through machine learning models. For users who wish to see all available information for the cwe capec entry. for users who want to customize what details are displayed. the product contains hard coded credentials, such as a password or cryptographic key. This guide explains what hardcoded credentials are, why sast scanners flag them, how to interpret and fix the checkmarx cwe 798 finding, and the correct remediation patterns for the most common languages.
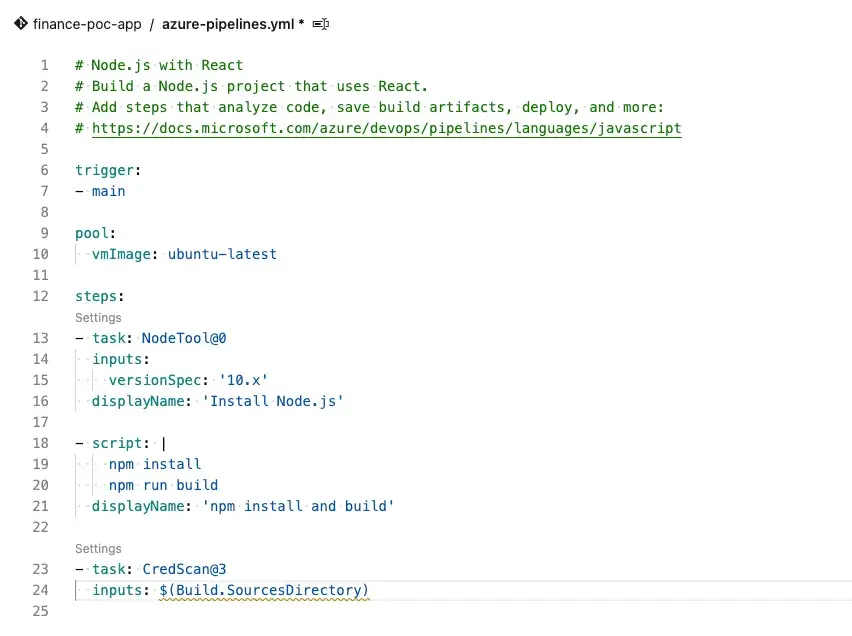
Blog Scan Code With Credential Scanner On Azure Devops Mycos For users who wish to see all available information for the cwe capec entry. for users who want to customize what details are displayed. the product contains hard coded credentials, such as a password or cryptographic key. This guide explains what hardcoded credentials are, why sast scanners flag them, how to interpret and fix the checkmarx cwe 798 finding, and the correct remediation patterns for the most common languages.
Blog Scan Code With Credential Scanner On Azure Devops Mycos
Comments are closed.