Half Yearly Cloud Security Infrastructure Roadmap With Key Operations

Half Yearly Cloud Security Infrastructure Roadmap With Key Operations Showcase the detailed overview of the project, the key deliverables, and the milestones to be achieved with the help of our fully customizable powerpoint layout. Presenting our innovatively structured cloud computing security half yearly roadmap with deployment plan guidelines template. showcase your roadmap process in different formats like pdf, png, and jpg by clicking the download button below.
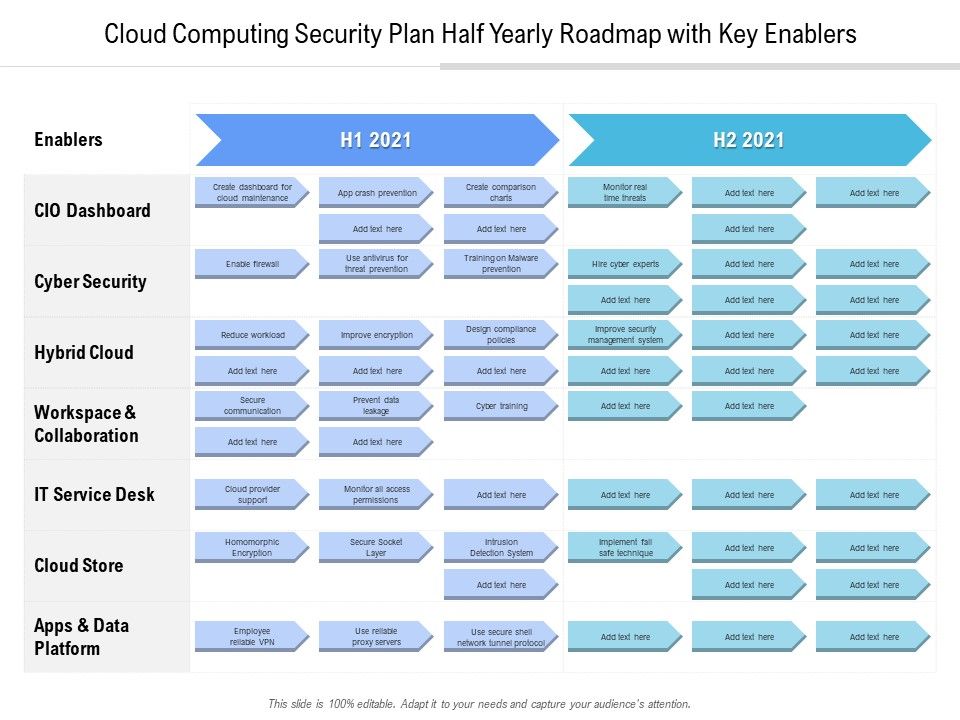
Cloud Computing Security Plan Half Yearly Roadmap With Key Enablers Diagram Combining real world insights compiled by the orca research pod, it offers practical guidance on where to focus, what to prioritize, and how to effectively secure multi cloud environments in the age of ai. we hope this report serves as a valuable resource for your teams. Although this document is not a tutorial on cloud security, it also introduces important concepts that are fundamental to cloud security, such as the shared security model, and it points to. This comprehensive guide examines twelve essential cloud security technologies, providing technical maturity assessments, deployment priorities, and vendor comparisons to help you build an effective cloud security deployment timeline for 2025 and beyond. This roadmap aligns at a high level with the expected knowledge areas for a cloud security engineer and is intended for people who are new to cloud security and aspire to perform a cloud security engineering role.

Half Yearly Cyber Security Infrastructure Roadmap Timeline This comprehensive guide examines twelve essential cloud security technologies, providing technical maturity assessments, deployment priorities, and vendor comparisons to help you build an effective cloud security deployment timeline for 2025 and beyond. This roadmap aligns at a high level with the expected knowledge areas for a cloud security engineer and is intended for people who are new to cloud security and aspire to perform a cloud security engineering role. Understanding the key security tools at each layer of the cloud and what matters most for your organization’s maturity. this post covers: cloud environments present adversaries with vast attack surfaces through their dynamic, multi layered architectures. Security and business leaders know that readiness plays a crucial role, and our cybersecurity forecast report for 2025 extrapolates from today’s trends the scenarios that we expect to arise in. The challenge isn’t knowing what good security looks like — it’s building it without wrecking your business or budget. that’s why this roadmap exists. Through a comprehensive survey of over 900 cisos, cybersecurity professionals, and it decision makers conducted in early 2025, this report captures the current state of cloud security from the ciso’s perspective — including what’s working, what’s breaking down, and where organizations are investing next. key findings:.
Comments are closed.