Hacking Vs Spoofing Attack Methods Compared

Phishing Vs Spoofing And How To Avoid It Bank Of Commerce Discover differences between hacking and spoofing. learn the different methods, how to identify signs of these attacks and what to do if you are a victim. It can be tempting to call any cyberattack a "hack." but, hacking and spoofing are two different attack methods; notably, hacking attacks a device or network, while spoofing attacks.

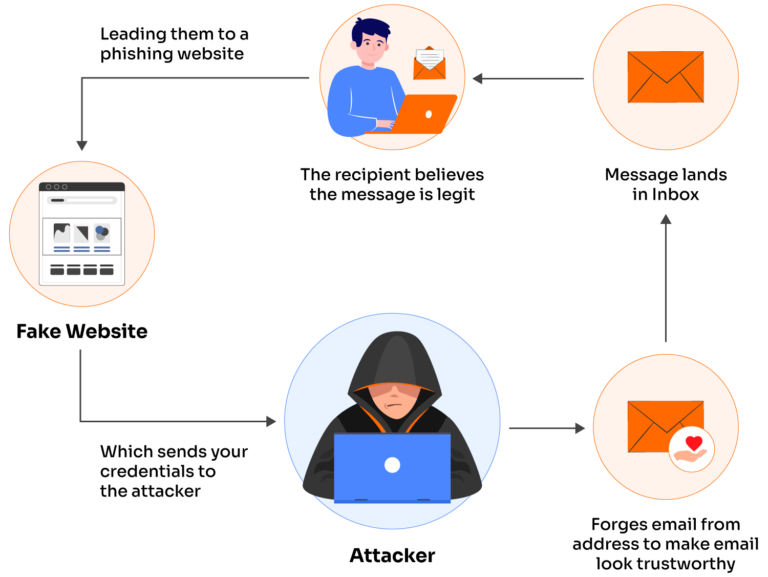
What Is A Spoofing Attack Everything To Know Hiya In hijacking, the main goal of a hacker is to take control of a target computer system or network connection to steal information without getting known to the target that they are getting hacked or hijacked. Hackers use methods like malware or brute force attacks to breach systems and steal information. spoofing, however, involves creating a fake account or message to deceive others, without needing direct access to the target’s account. Hacking and spoofing are two common cybersecurity threats that are often conflated, although they have similar consequences, almost everything else about these attacks are different . What is spoofing? the concept of spoofing has been around for decades and it involves techniques where an attacker or scammer impersonates or creates a means to deceive and mislead a person or system.

What Is A Spoofing Attack Definition And Types Hacking and spoofing are two common cybersecurity threats that are often conflated, although they have similar consequences, almost everything else about these attacks are different . What is spoofing? the concept of spoofing has been around for decades and it involves techniques where an attacker or scammer impersonates or creates a means to deceive and mislead a person or system. Hacking and spoofing can appear to be the same at first glance but are actually quite different. the risks of hacking, especially for businesses, are much greater than those posed by spoofing. Bec attacks have cost $55 billion over the past decade. most don't involve actual hacking — they're spoofing attacks. learn the critical difference and how to defend against both. Hacking and spoofing can appear to be the same at first glance but are actually quite different. the risks of hacking, especially for businesses, are much greater than those posed by spoofing. What is a spoofing attack definition and types hacking and spoofing can appear to be the same at first glance but are actually quite different. the risks of hacking, especially for businesses, are much greater than those posed by spoofing.
Phishing Vs Spoofing What S The Difference Valimail Hacking and spoofing can appear to be the same at first glance but are actually quite different. the risks of hacking, especially for businesses, are much greater than those posed by spoofing. Bec attacks have cost $55 billion over the past decade. most don't involve actual hacking — they're spoofing attacks. learn the critical difference and how to defend against both. Hacking and spoofing can appear to be the same at first glance but are actually quite different. the risks of hacking, especially for businesses, are much greater than those posed by spoofing. What is a spoofing attack definition and types hacking and spoofing can appear to be the same at first glance but are actually quite different. the risks of hacking, especially for businesses, are much greater than those posed by spoofing.
Comments are closed.