Hacking Remote Docker Api Misconfiguration

Docker Api Or Agent General Docker Community Forums One such vulnerability has emerged in containerized environments, specifically with misconfigured docker apis. attackers are now leveraging these misconfigurations to stealthily mine. Attackers exploit docker misconfigurations to mine cryptocurrency using tor, targeting technology, financial, and healthcare industries.

Docker Error Invoking Remote Method How To Fix It In a recent campaign uncovered by trend micro, attackers exploited exposed docker apis to launch a sophisticated cryptojacking operation — hiding behind tor, modifying system configs, and. This repository contains a docker remote api scanner and exploit tool designed for educational and research purposes. it enables users to perform security assessments and experiments related to docker container environments. Recent incidents highlight the severity of exploiting docker remote api servers. in one notable case, an unidentified threat actor deployed a cryptocurrency miner using the described method. This blog explains about misconfigurations on default ports in docker, their risks, impacts, and methods to mitigate them.
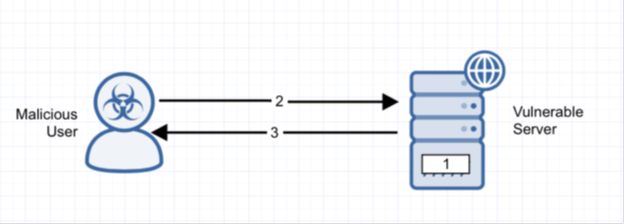
Docker Daemon Public Api Security Misconfiguration Alert Logic Recent incidents highlight the severity of exploiting docker remote api servers. in one notable case, an unidentified threat actor deployed a cryptocurrency miner using the described method. This blog explains about misconfigurations on default ports in docker, their risks, impacts, and methods to mitigate them. Hackers exploit misconfigured docker apis to mine cryptocurrency using tor anonymity network. attackers create a new docker instance, access host system files, and deploy crypto miners via tor. “attackers are exploiting misconfigured docker apis to gain access to containerized environments, then using tor to mask their activities while deploying crypto miners,” trend micro researchers sunil bharti and shubham singh said in an analysis published last week. Threat actors are exploiting misconfigured docker remote api servers by deploying the gafgyt malware, potentially enabling them to launch ddos attacks against these vulnerable systems. Hackers behind a cryptomining campaign have managed to avoid detection since 2019. the attacks exploited misconfigured docker apis that allowed them to gain network entry and ultimately sets up a backdoor on compromised hosts to mine cryptocurrency, researchers said.
Comments are closed.