Hackers Turn Your Printer Into Admin Access Print Spooler Exploit
Hacker Briefly Hijacks Insecure Printers Bbc News On the client side (i.e. the target), we should now be able to execute the following commands to connect to the shared printer and coerce the print spooler service to download and install the vulnerable printer driver locally. How do print spooler remain vulnerable in 2025? discover how attackers exploit them and how wizlynx group helps secure your infrastructure.

Be Aware Attackers Exploit Windows Print Spooler This specific vulnerability enables remote code execution (rce), where attackers can exploit the flaw by sending specially crafted requests to the print spooler service, allowing them to run arbitrary code in the context of system —the highest level of privilege in windows. The core of this vulnerability is that through adding a printer port that points to the system folder and by rebooting the spooler service, the attacker gets to run its malicious file when the spooler reloads, running as system, and "prints" to the folder specified in the printer port. Print spooler vulnerabilities like printnightmare enable rce and privilege escalation. learn how to harden or safely disable it on your windows servers. This vulnerability exists due to an authorisation bypass bug in the print spooler service spoolsv.exe on windows systems, which allows authenticated remote users to install print drivers using the rpc call rpcaddprinterdriver and specify a driver file located on a remote location.
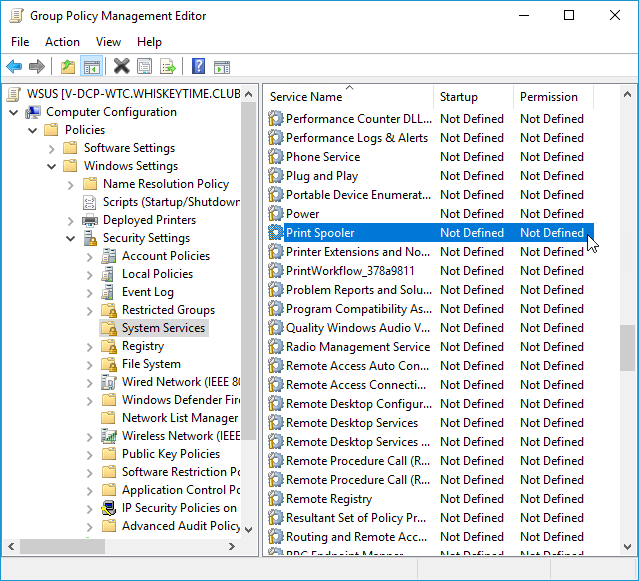
How Check And Patch The Printnightmare Exploit Pdq Print spooler vulnerabilities like printnightmare enable rce and privilege escalation. learn how to harden or safely disable it on your windows servers. This vulnerability exists due to an authorisation bypass bug in the print spooler service spoolsv.exe on windows systems, which allows authenticated remote users to install print drivers using the rpc call rpcaddprinterdriver and specify a driver file located on a remote location. The print spooler service can be abused by an authenticated remote attacker to load a dll through a crafted dcerpc request, resulting in remote code execution as nt authority\system. Learn how the spoolfool vulnerability escalates privileges in windows using print spooler, and explore two exploitation methods. Printnightmare explained: learn about the windows print spooler vulnerability and how papercut helps you maintain a secure printing environment now. Cve 2024 38198 is an "elevation of privilege" vulnerability. in plain terms, it allows an attacker with low privileges on a windows machine to gain higher level or even system privileges — letting them control the system, install malware, or steal sensitive info.
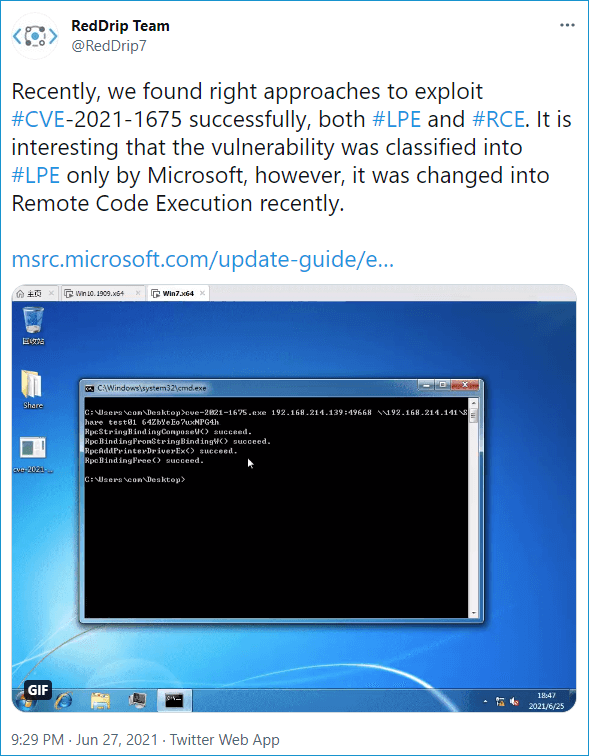
How Check And Patch The Printnightmare Exploit Pdq The print spooler service can be abused by an authenticated remote attacker to load a dll through a crafted dcerpc request, resulting in remote code execution as nt authority\system. Learn how the spoolfool vulnerability escalates privileges in windows using print spooler, and explore two exploitation methods. Printnightmare explained: learn about the windows print spooler vulnerability and how papercut helps you maintain a secure printing environment now. Cve 2024 38198 is an "elevation of privilege" vulnerability. in plain terms, it allows an attacker with low privileges on a windows machine to gain higher level or even system privileges — letting them control the system, install malware, or steal sensitive info.
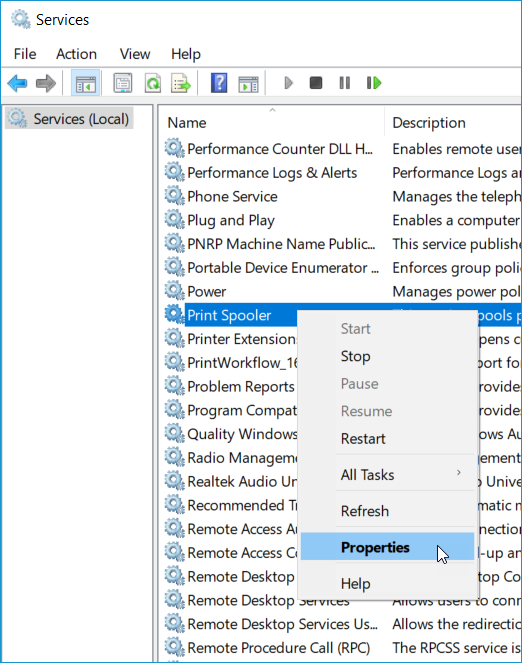
Printnightmare An Exploit Using The Windows Print Spooler Fix Update Printnightmare explained: learn about the windows print spooler vulnerability and how papercut helps you maintain a secure printing environment now. Cve 2024 38198 is an "elevation of privilege" vulnerability. in plain terms, it allows an attacker with low privileges on a windows machine to gain higher level or even system privileges — letting them control the system, install malware, or steal sensitive info.
Comments are closed.