Hacked Without A Password How Session Hijacking Bypasses 2fa

What Is Session Hijacking And How Do You Prevent It One of the most dangerous and increasingly common threats is session hijacking (also known as cookie theft). this sophisticated attack vector allows criminals to access your accounts without knowing your password or needing your 2fa code, rendering standard sms or app based authentication useless. Learn how attackers bypass 2fa and mfa using session hijacking, aitm phishing, and logic flaws. discover technical examples and strategies to secure your auth.
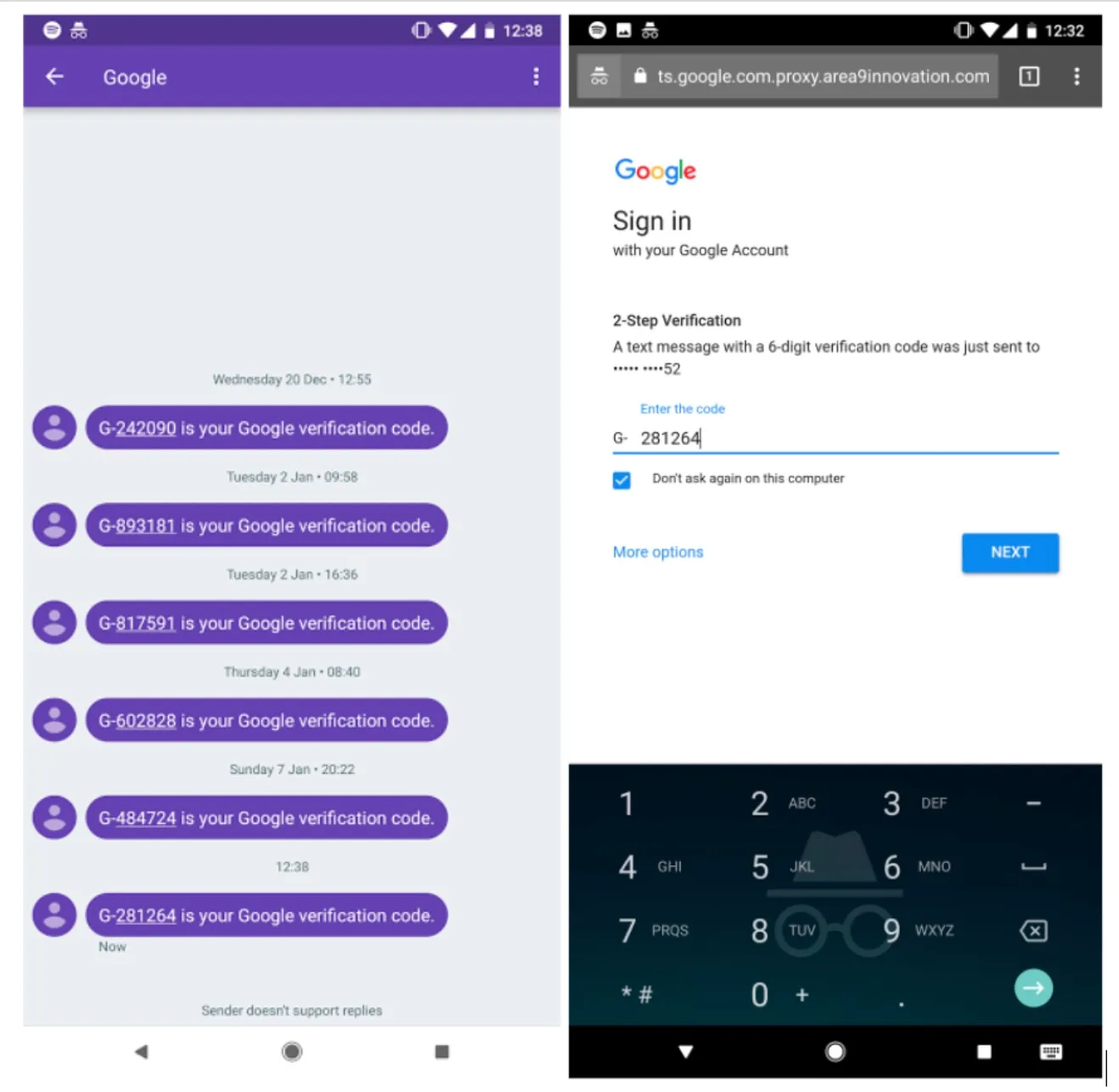
How To Bypass 2fa Two Factor Authentication By stealing browser cookies post authentication, attackers can gain full access to your accounts without needing your password or 2fa codes, effectively bypassing these critical security layers. In this cybersecurity tutorial, we explore the mechanics of "session hijacking" via cookie theft. learn how attackers exploit active session tokens to gain unauthorized access to web accounts. But hackers have found a way to walk right through your front door without needing your password or your 6 digit code. it’s called session hijacking (or "cookie theft"), and it is currently. Attackers steal authenticated session tokens to access accounts without triggering new authentication requirements. this approach bypasses 2fa entirely because the system treats stolen sessions as legitimate.

2fa Bypass Attacks Mitigation Strategies Fortified Health But hackers have found a way to walk right through your front door without needing your password or your 6 digit code. it’s called session hijacking (or "cookie theft"), and it is currently. Attackers steal authenticated session tokens to access accounts without triggering new authentication requirements. this approach bypasses 2fa entirely because the system treats stolen sessions as legitimate. Session hijacking is when an attacker steals or reuses an authenticated session token. learn how it happens, why password changes can fail, and defensive. On an infected device, this deploys a man in the middle attack between user and legitimate account sign in page, “capturing login credentials, tokens, and session cookies in real time,. Learn how session hijacking bypasses mfa by stealing post authentication tokens. discover detection methods and prevention strategies for saas security teams. As enterprises adopt passwordless authentication to eliminate password based attacks, a critical vulnerability remains: session hijacking. this attack bypasses passwordless methods entirely by targeting the session artifacts created after successful authentication.
How Attackers Bypass Two Factor Authentication With Phishing Session hijacking is when an attacker steals or reuses an authenticated session token. learn how it happens, why password changes can fail, and defensive. On an infected device, this deploys a man in the middle attack between user and legitimate account sign in page, “capturing login credentials, tokens, and session cookies in real time,. Learn how session hijacking bypasses mfa by stealing post authentication tokens. discover detection methods and prevention strategies for saas security teams. As enterprises adopt passwordless authentication to eliminate password based attacks, a critical vulnerability remains: session hijacking. this attack bypasses passwordless methods entirely by targeting the session artifacts created after successful authentication.
Comments are closed.