Guide To Zero Trust Identities

An Overview Of Zero Trust Study Guide Pdf Computer Network This article is your comprehensive guide to understanding the role of identity within zta, its benefits, and how leveraging netfoundry can accelerate the journey toward zero trust maturity. Identity is central to a successful zero trust strategy. for further information or help with implementation, contact your customer success team or continue to read through the other chapters of this guide, which span all zero trust pillars.

Describe Identities In Zero Trust Training Microsoft Learn A simple guide to zero trust identity architecture for enterprises. learn steps to secure access, users, and data without complexity. Implementation effort: medium – it and security teams must identify tier zero roles, configure privileged identity management (pim) settings, and transition users to just in time (jit) access workflows. Learn how to implement zero trust security with clear pillars, a practical roadmap, and tactics that solve challenges and cut risk across cloud environments. Federal zero trust data security guide this guide and its companion piece—available from the chief information officers council—provide agencies with critical direction on defining, identifying, and securing data assets.
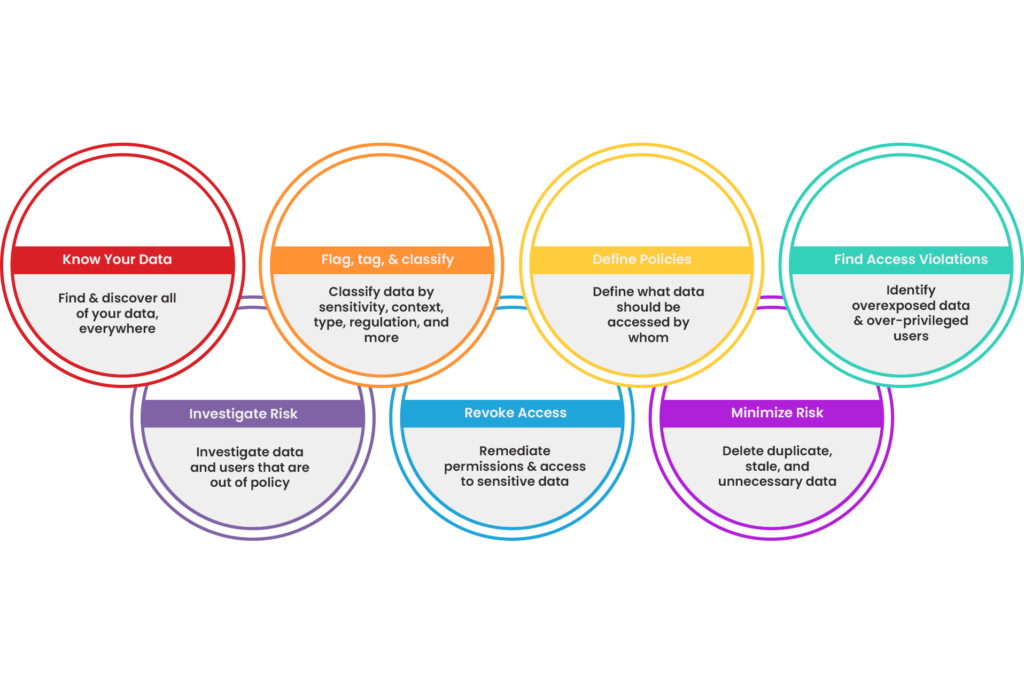
Enable Zero Trust Bigid Learn how to implement zero trust security with clear pillars, a practical roadmap, and tactics that solve challenges and cut risk across cloud environments. Federal zero trust data security guide this guide and its companion piece—available from the chief information officers council—provide agencies with critical direction on defining, identifying, and securing data assets. Simplify zero trust implementation with this detailed guide. learn the policies, compliance, and monitoring strategies to implement zero trust security. Learn what zero trust is, key identity types, and how to build a strong zero trust identity strategy with steps and best practices. Get a comprehensive guide to key zero trust concepts, the most influential frameworks, top zero trust benefits, and best practices for selecting a zero trust vendor. This guide provides a detailed, easy to understand, and fully updated breakdown of the 7 pillars of zero trust, industry best practices, and the nist zero trust principles that shape modern digital security.
Practical Guide To Understanding And Implementing Zero Trust Simplify zero trust implementation with this detailed guide. learn the policies, compliance, and monitoring strategies to implement zero trust security. Learn what zero trust is, key identity types, and how to build a strong zero trust identity strategy with steps and best practices. Get a comprehensive guide to key zero trust concepts, the most influential frameworks, top zero trust benefits, and best practices for selecting a zero trust vendor. This guide provides a detailed, easy to understand, and fully updated breakdown of the 7 pillars of zero trust, industry best practices, and the nist zero trust principles that shape modern digital security.
Comments are closed.