Guide To Cloud Api Security Preventing Token Abuse

Guide To Cloud Api Security Preventing Token Abuse This surge highlights the urgent need for robust cloud api security frameworks that address technical vulnerabilities and evolving attacker tactics. the anatomy of modern token based attacks cloud apis rely heavily on oauth 2.0 tokens and api keys for authentication, creating a lucrative target for cybercriminals. To secure an api, use a combination of defensive strategies: require https for all traffic, set up strong authentication (oauth 2.0, jwts), conduct thorough input validation, implement rate limiting, practice the principle of least privilege, and watch for abnormal api behavior.
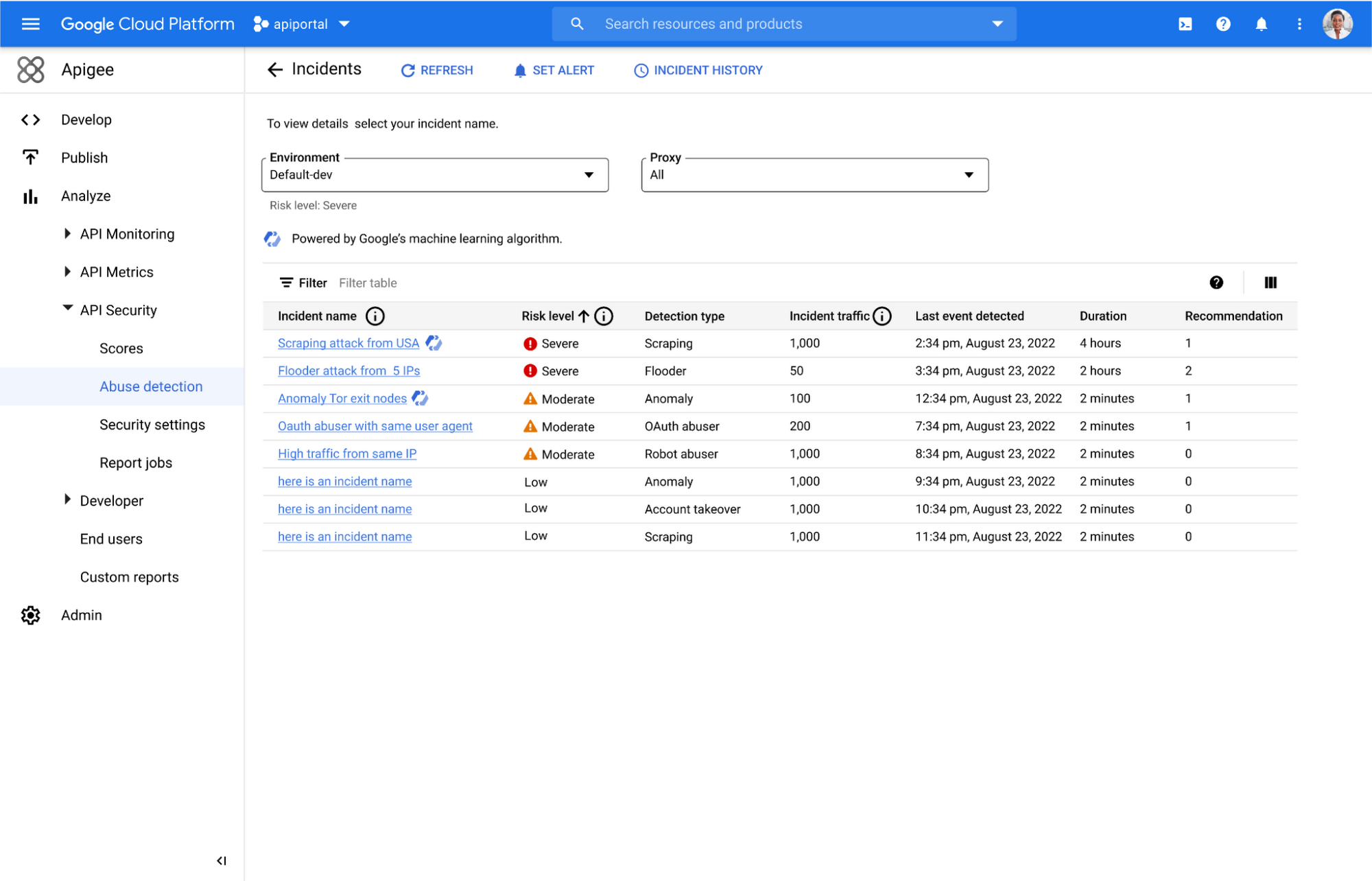
Announcing Api Abuse Detection Powered By Machine Learning Google Securing apis within a cloud environment is paramount for the modern development landscape. this guide offers a comprehensive overview of best practices, addressing both fundamental security principles and the unique challenges presented by cloud platforms. This guide provides an api security master class covering authentication, validation, encryption, and throttling, tailored explicitly for cloud native applications. Prevent api abuse by allowing only validated, good api traffic. vulnerabilities in organizations’ own apis or with third party api integrations can lead to unauthorized data access. consolidate data leakage protection across all saas apps, web apps, and apis. Api security is now central to protecting saas data, preventing oauth and token abuse, and reducing breach risk across interconnected applications.
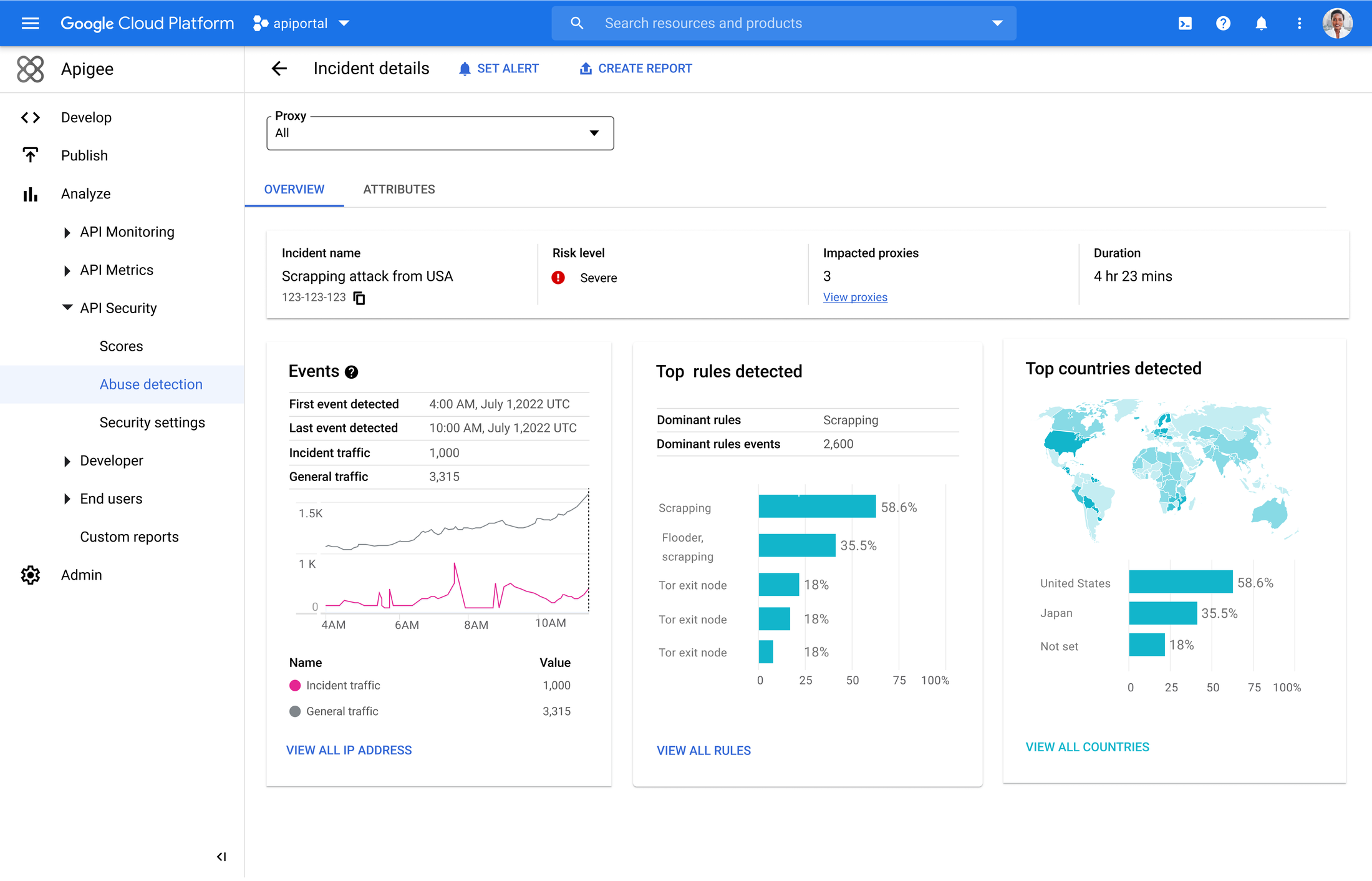
Announcing Api Abuse Detection Powered By Machine Learning Google Prevent api abuse by allowing only validated, good api traffic. vulnerabilities in organizations’ own apis or with third party api integrations can lead to unauthorized data access. consolidate data leakage protection across all saas apps, web apps, and apis. Api security is now central to protecting saas data, preventing oauth and token abuse, and reducing breach risk across interconnected applications. Blog | centex technologies learn how to secure cloud apis against abuse and vulnerabilities. this in depth guide covers common threats, prevention strategies, real world examples, and a security first api development lifecycle. Learn actionable best practices to safeguard your apis, protect sensitive data and stay ahead of evolving cyber threats across industries like healthcare, finance and e commerce. As organizations speed up cloud adoption, api token abuse has emerged as a vital vulnerability vector. current incidents at important platforms like docusign and heroku uncovered systemic dangers in token administration. As organizations accelerate cloud adoption, api token abuse has emerged as a critical vulnerability vector. recent incidents at significant platforms like docusign and heroku exposed systemic risks in token management.
Comments are closed.