Graylog Api Security Intro Demo

Graylog Resource Library This video provides a demo of graylog api security, version 3.6. many organizations report a lack of visibility into their apis as their biggest obstacle to improving api security. Discover and improve your api security with graylog! in this quick demo, rob from resurface now graylog, showcases how graylog helps you understand and manage your api attack surface.
Graylog Api Security Request a live demo to explore powerful log management, real time analysis, and security insights tailored to your needs. Discover and improve your api security with graylog! in this quick demo, rob from resurface now graylog, showcases how graylog helps you understand and manage your api attack surface. With enhanced tools to reduce alert fatigue, cut storage costs, and streamline investigations, this release empowers teams to work more efficiently without sacrificing performance. Watch vp of engineering for graylog api security robert dickinson take you through a detailed demo of api security. find out how to discover your apis, find attacks, and block them.

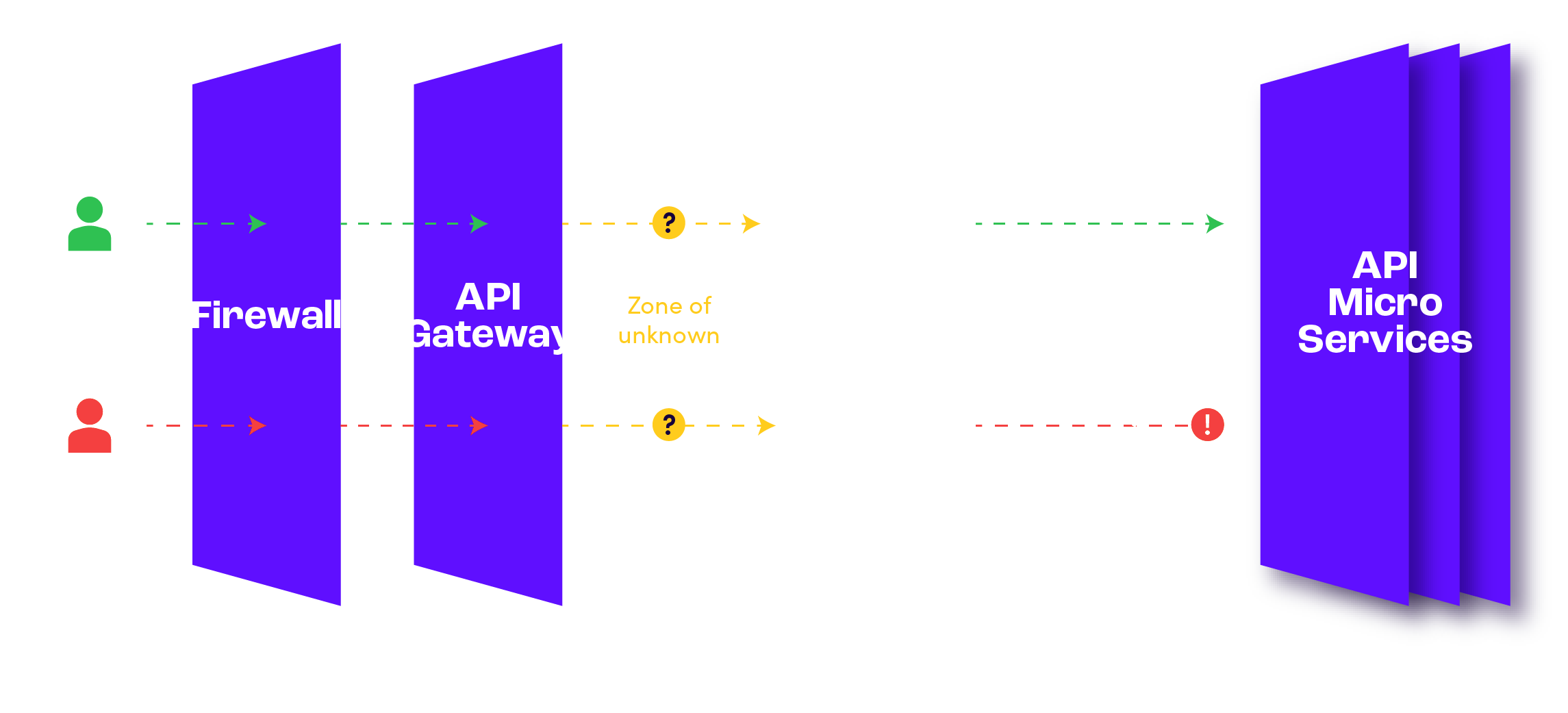
Graylog Resource Library With enhanced tools to reduce alert fatigue, cut storage costs, and streamline investigations, this release empowers teams to work more efficiently without sacrificing performance. Watch vp of engineering for graylog api security robert dickinson take you through a detailed demo of api security. find out how to discover your apis, find attacks, and block them. With graylog api security: discover apis and pii flows in real time, going beyond headers and analyzing full api request and response payloads to identify potential exfiltration attempts faster. Api security has recently become a premier attack surface for bad actors to breach your perimeter while appearing as valid users. Experience graylog security (siem) in a free demo & get answers to your questions! join our team of experts in a live demo or get a custom demo of graylog tailored to you. Graylog api security discovers your apis and the risks from their use by legitimate customers, malicious attackers, partners, and insiders. this protection is accomplished with built in automated and custom signatures and alerts.
Comments are closed.