Graphql Protection Wallarm Documentation

Wallarm Cyber Security Solutions Pdf Vulnerability Computing This document describes how to use wallarm to protect your apis from these attacks by setting graphql policy a set of limits for the graphql requests. being the extended protection, graphql api protection is the part of the advanced api security subscription plan. This document describes how to use wallarm to protect your apis from these attacks by setting graphql policy a set of limits for the graphql requests. being the extended protection, graphql api protection is the part of the advanced api security subscription plan.
Overview Wallarm Documentation By adhering to these limits, you can shield your graphql api from malicious queries, including potential dos attacks. this guide explains how the firewall calculates query attributes like node requests, query depth, and complexity before aligning them with your set parameters. On this page, we’ll survey potential attack vectors for graphql—many of which are denial of service attacks—along with how a layered security posture can help protect a graphql api from malicious operations. Graphql api protection protects your graphql apis against specialized attacks that exploit protocol specific such as batching, nesting queries, introspection, etc. it can prevent resource exhaustion, denial of service (dos), excessive information exposure and other attacks. Api firewall is a high performance proxy with api request and response validation based on openapi and graphql schemas. it is designed to protect rest and graphql api endpoints in cloud native environments.
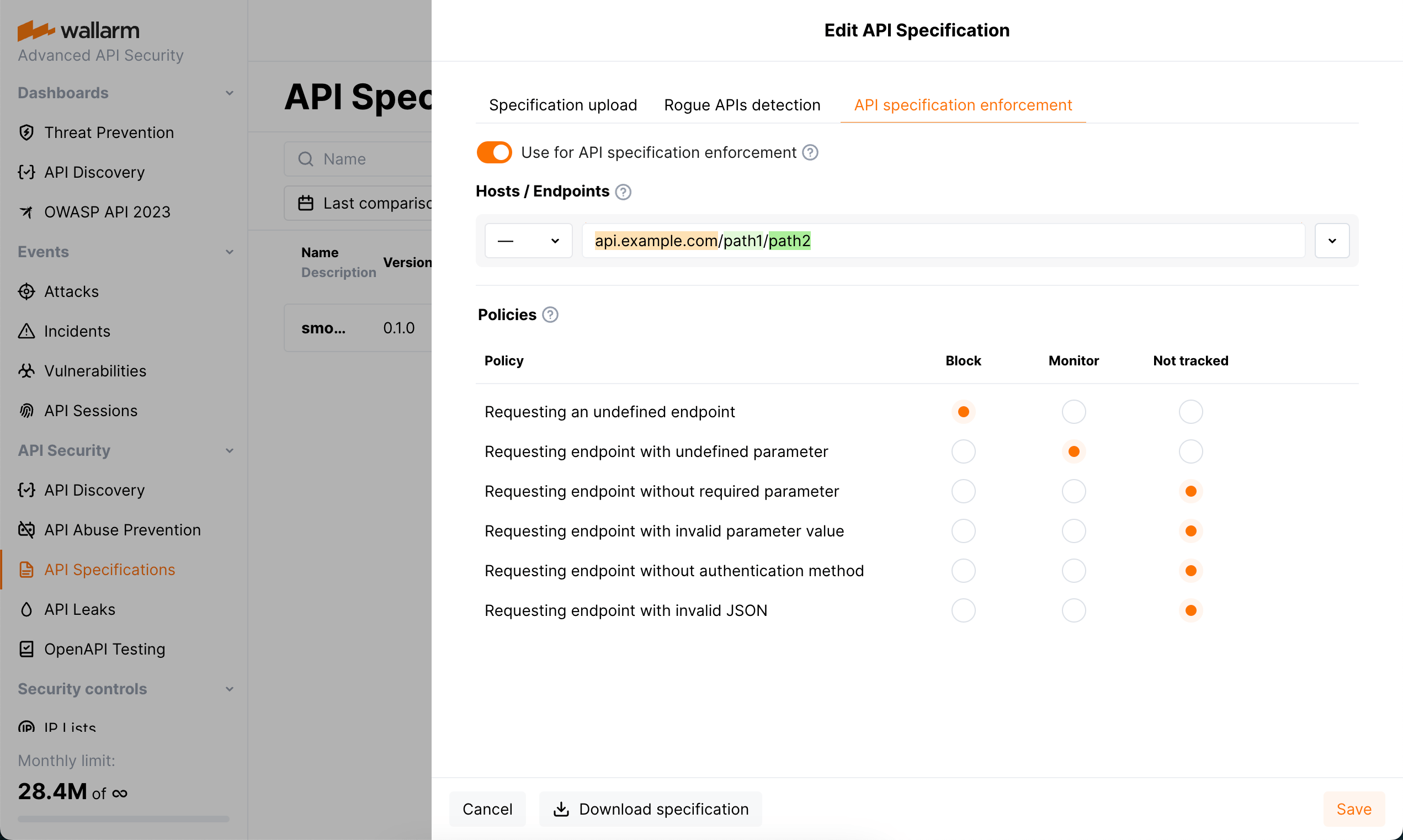
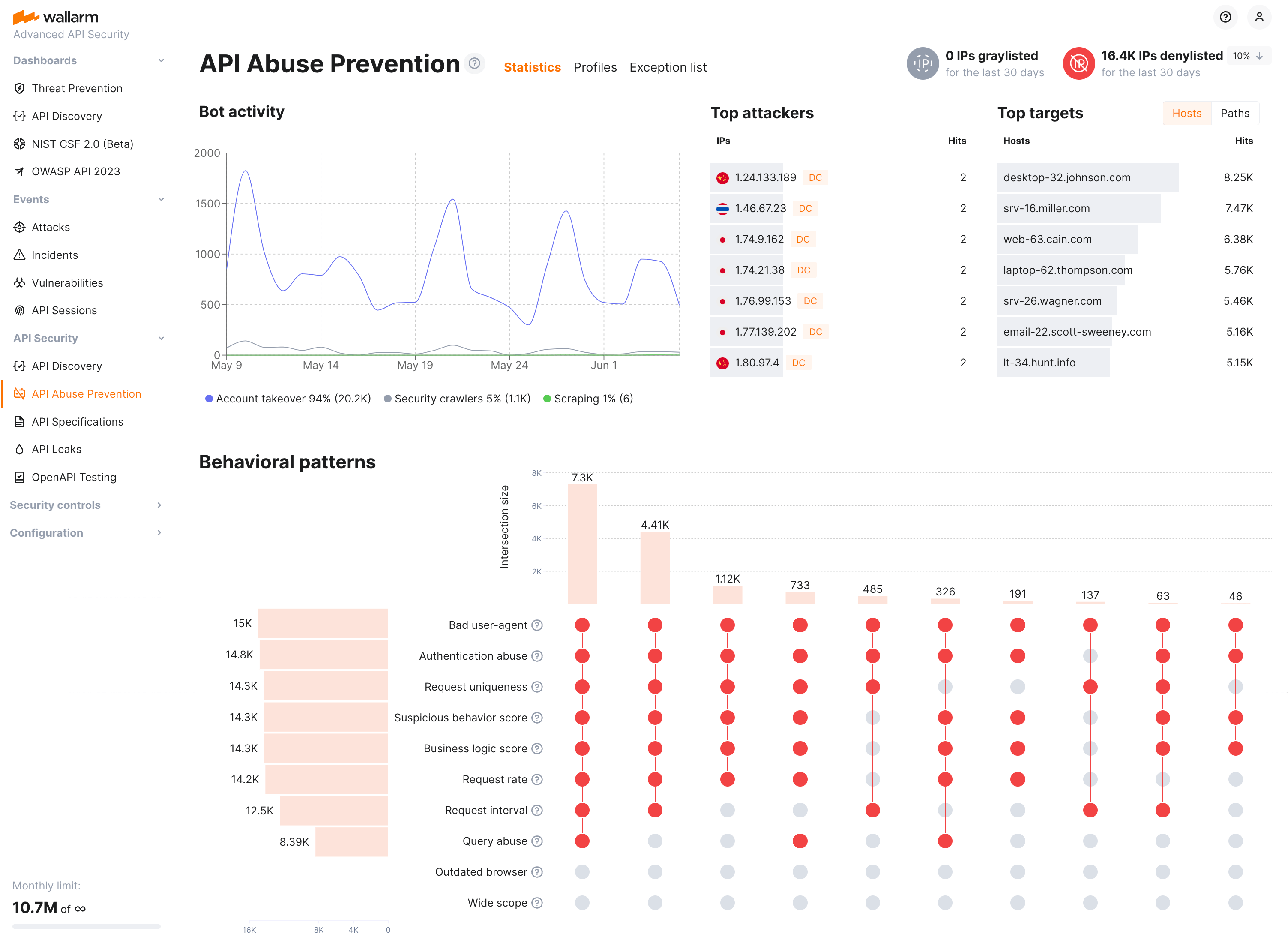
Overview Wallarm Documentation Graphql api protection protects your graphql apis against specialized attacks that exploit protocol specific such as batching, nesting queries, introspection, etc. it can prevent resource exhaustion, denial of service (dos), excessive information exposure and other attacks. Api firewall is a high performance proxy with api request and response validation based on openapi and graphql schemas. it is designed to protect rest and graphql api endpoints in cloud native environments. Rules are used to fine tune the default wallarm behavior during the analysis of requests and their further processing. thus, using rules you can change how the system detects malicious requests and acts when such malicious requests are detected. This guide walks through downloading, installing, and starting wallarm api firewall on docker for graphql api request validation. in graphql mode, the api firewall acts as a proxy, forwarding graphql requests from users to the backend server using either http or the websocket (graphql ws) protocols. Wallarm delivers real time protection for apis and ai agents, stopping automated threats and abuse while also providing full security visibility with complete api inventory and risk detection. Wallarm delivers real time protection for apis and ai agents, stopping automated threats and abuse while also providing full security visibility with complete api inventory and risk detection.
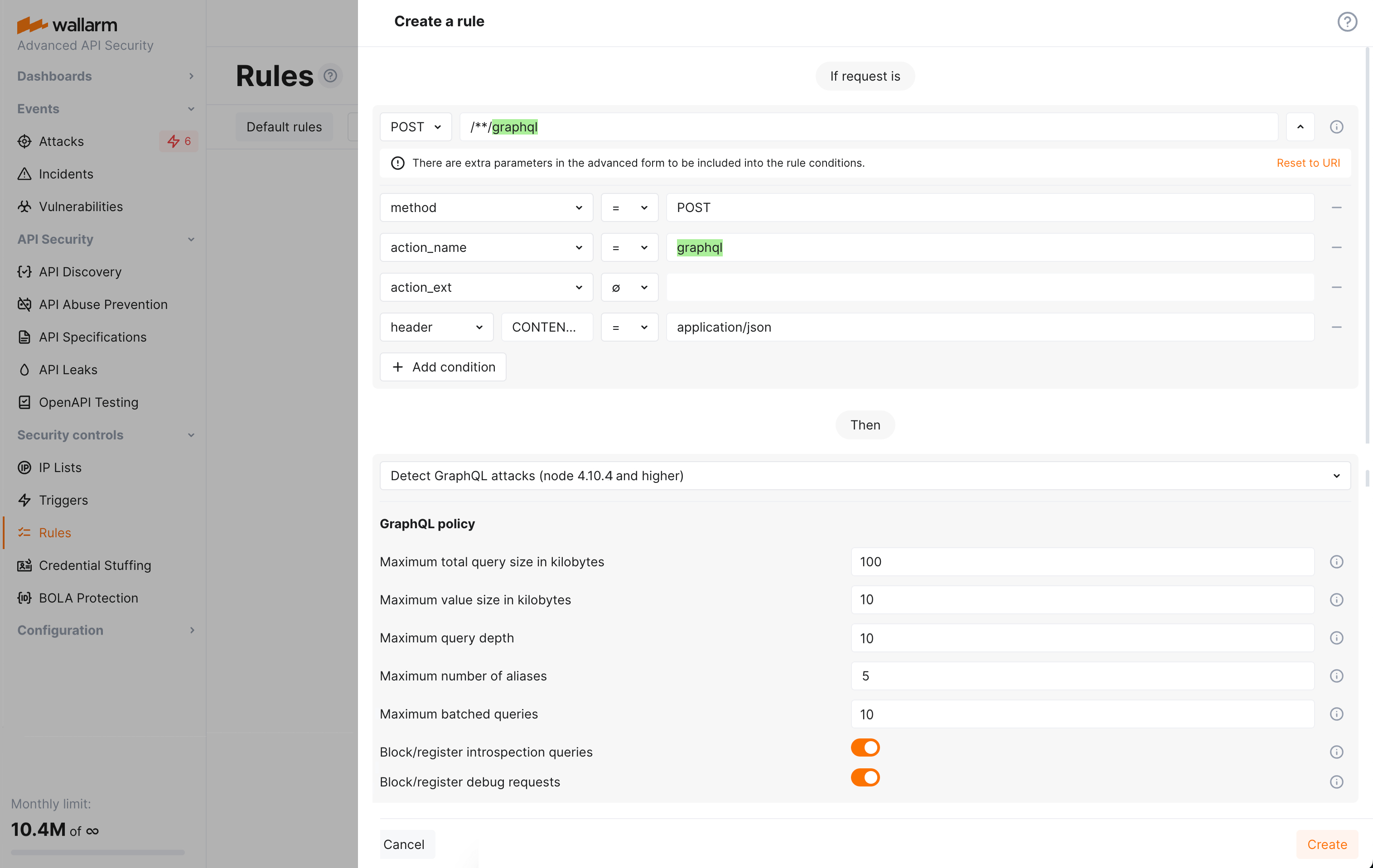
Overview Wallarm Documentation Rules are used to fine tune the default wallarm behavior during the analysis of requests and their further processing. thus, using rules you can change how the system detects malicious requests and acts when such malicious requests are detected. This guide walks through downloading, installing, and starting wallarm api firewall on docker for graphql api request validation. in graphql mode, the api firewall acts as a proxy, forwarding graphql requests from users to the backend server using either http or the websocket (graphql ws) protocols. Wallarm delivers real time protection for apis and ai agents, stopping automated threats and abuse while also providing full security visibility with complete api inventory and risk detection. Wallarm delivers real time protection for apis and ai agents, stopping automated threats and abuse while also providing full security visibility with complete api inventory and risk detection.
Comments are closed.