Google Hacking Database Bpotravel
Google Hacking Database Pagro The ghdb is an index of search queries (we call them dorks) used to find publicly available information, intended for pentesters and security researchers. Cybercrime google warns of new campaign targeting bpos to steal corporate data tracked as unc6783, the threat actor is likely linked to mr. raccoon, the hacker behind the alleged theft of adobe data from a bpo.
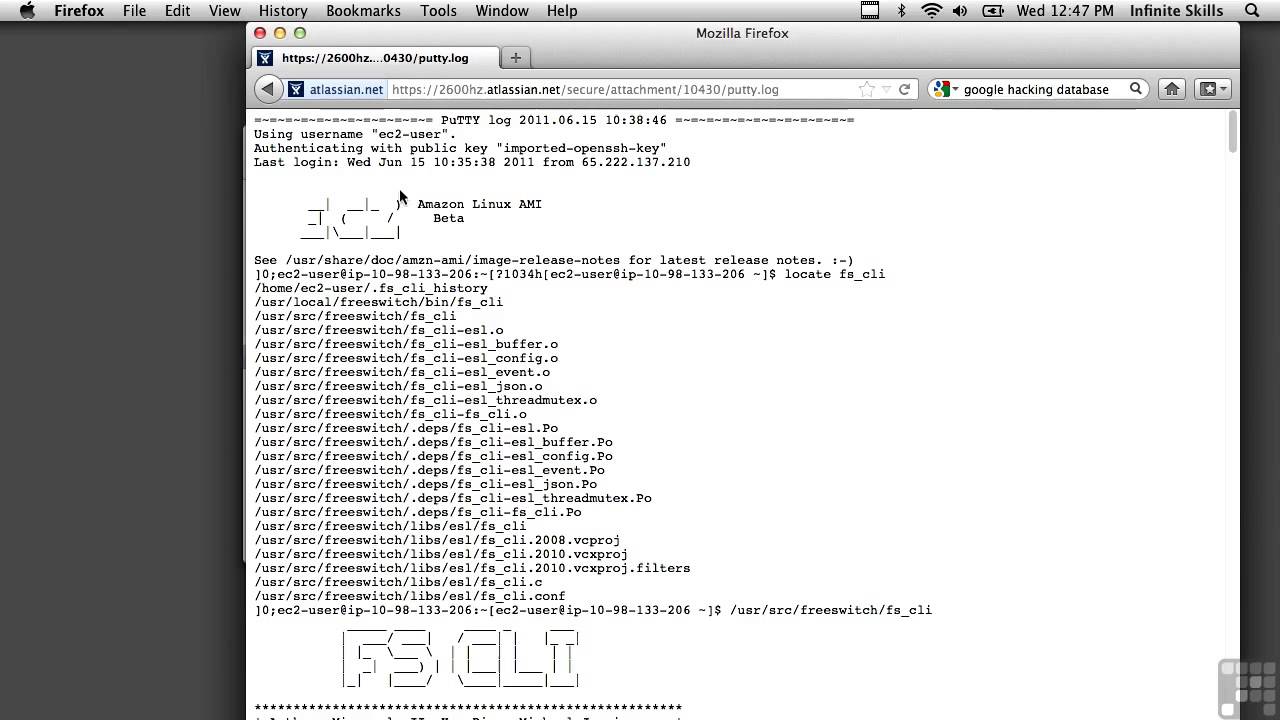
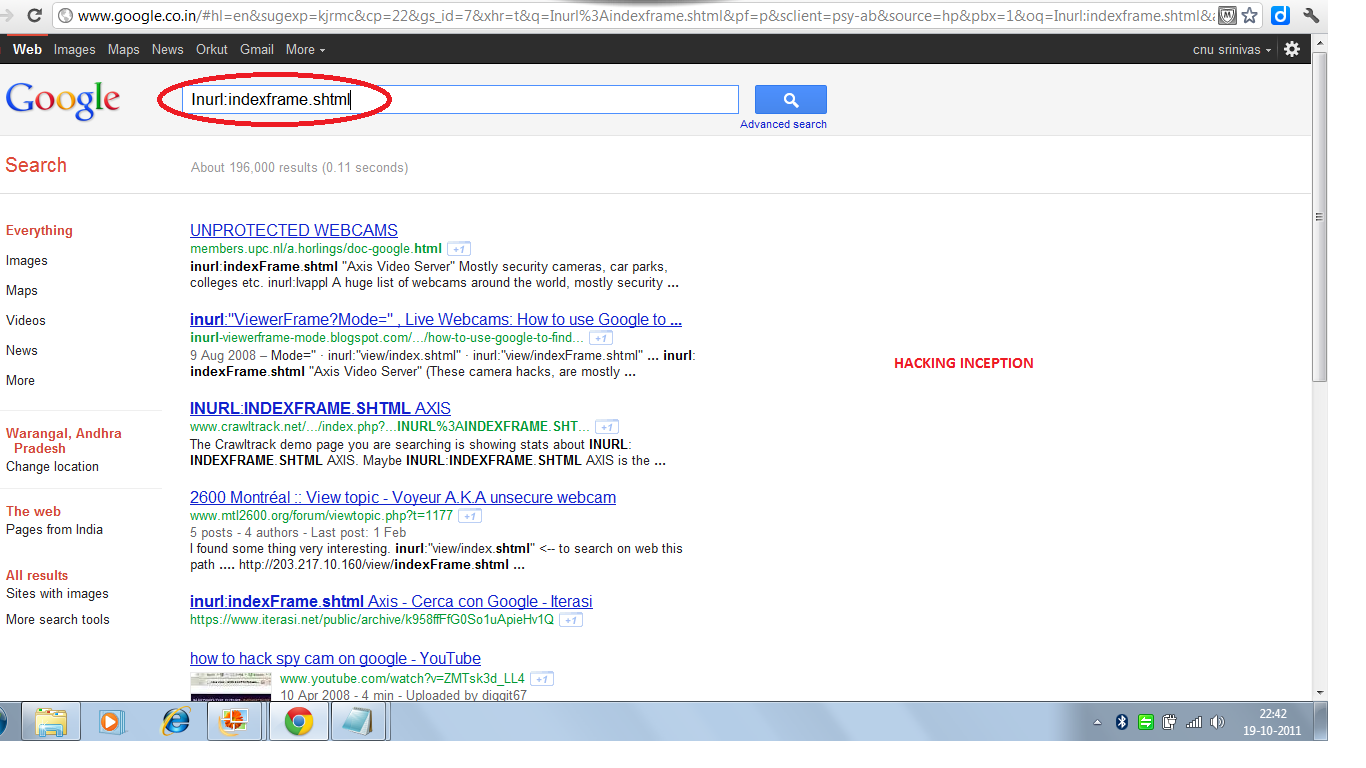
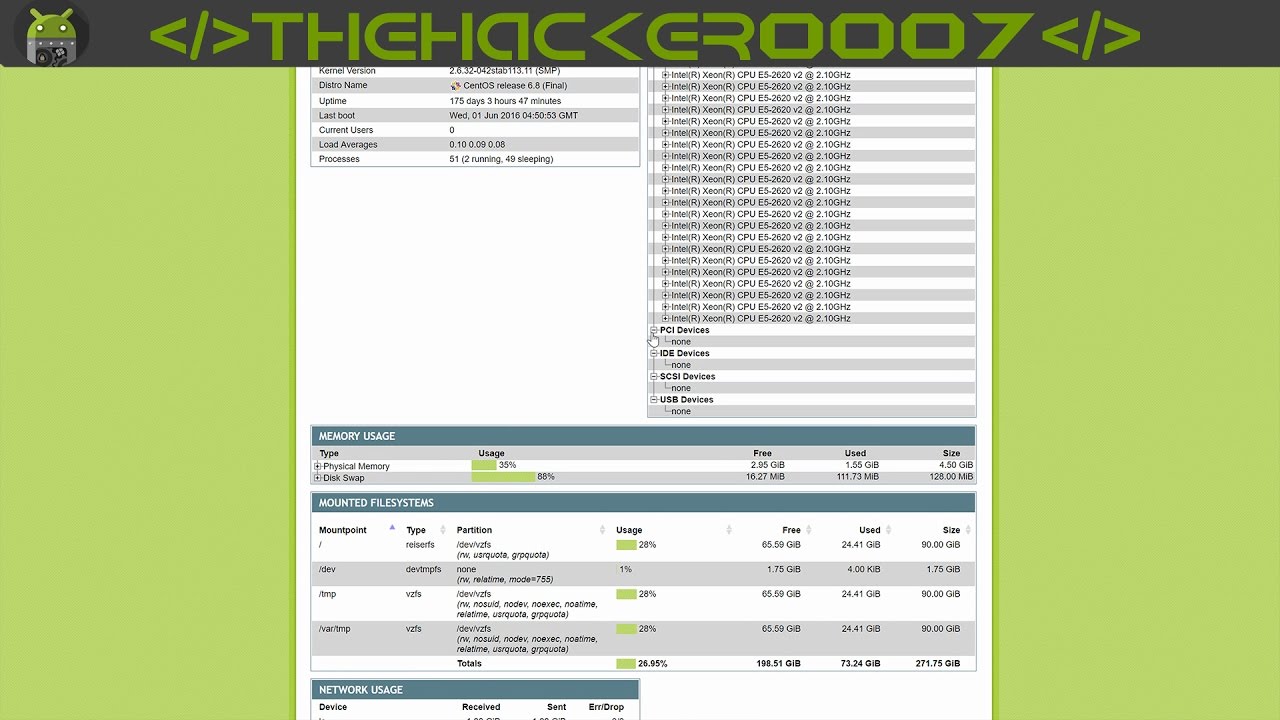
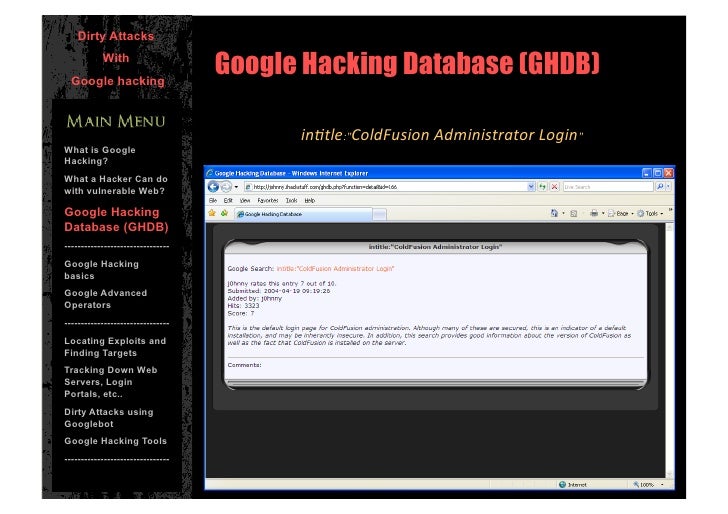
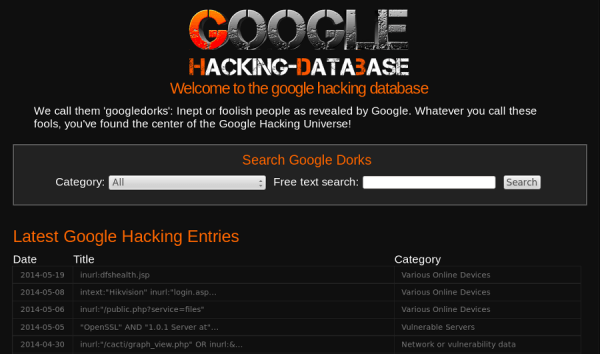
Google Hacking Database Pagro Google hacking database (ghdb) the google hacking database (ghdb) is a collection of advanced google search queries, known as google dorks, used to identify sensitive information and potential vulnerabilities exposed on the internet. Google hacking google hacking, also named google dorking, [1][2] is a hacker technique that uses google search and other google applications to find security holes in the configuration and computer code that websites are using. While google dorking itself is legal (in most countries), it might quickly lead to actions that aren't, such as visiting sites with illegal content. hence using tor or a vpn is recommended. using a search aggregator like searx can enhance search privacy and efficiency. The google hacking database, or ghdb, comprises advanced search queries or google dorks that security experts and white hat hackers employ to identify vulnerabilities, misconfigurations, and exposed sensitive information on websites.

Google Hacking Database Fcode Labs While google dorking itself is legal (in most countries), it might quickly lead to actions that aren't, such as visiting sites with illegal content. hence using tor or a vpn is recommended. using a search aggregator like searx can enhance search privacy and efficiency. The google hacking database, or ghdb, comprises advanced search queries or google dorks that security experts and white hat hackers employ to identify vulnerabilities, misconfigurations, and exposed sensitive information on websites. In sql injection, attackers alter sql queries and inject malicious code by exploiting application vulnerabilities, modifying database information, accessing sensitive data, can issue commands to the system. Tourists are warned to be extra vigilant when making bookings, and google, cyber security teams, and the indonesian hotel and restaurant association are working together to understand the scale of the issue and create solutions as quickly as possible. A security researcher uncovered an exposed online database that was stockpiling user information likely collected via malware infected pcs. Discover the google hacking database (ghdb), a valuable resource for cybersecurity professionals and ethical hackers, providing advanced search techniques and exposing vulnerabilities.
Google Hacking Database Mojoplora In sql injection, attackers alter sql queries and inject malicious code by exploiting application vulnerabilities, modifying database information, accessing sensitive data, can issue commands to the system. Tourists are warned to be extra vigilant when making bookings, and google, cyber security teams, and the indonesian hotel and restaurant association are working together to understand the scale of the issue and create solutions as quickly as possible. A security researcher uncovered an exposed online database that was stockpiling user information likely collected via malware infected pcs. Discover the google hacking database (ghdb), a valuable resource for cybersecurity professionals and ethical hackers, providing advanced search techniques and exposing vulnerabilities.
Google Hacking Database Mojoplora A security researcher uncovered an exposed online database that was stockpiling user information likely collected via malware infected pcs. Discover the google hacking database (ghdb), a valuable resource for cybersecurity professionals and ethical hackers, providing advanced search techniques and exposing vulnerabilities.
Google Hacking Database Bpotravel
Comments are closed.