Google Dorks That Reveal Exposed Data

What Are Google Dorks And How Are Google Hacks Used The google hacking database (ghdb) is a collection of advanced google search queries, known as google dorks, used to identify sensitive information and potential vulnerabilities exposed on the internet. Companies like red sentry have developed solutions that fold this reality into penetration testing and continuous monitoring, using search based signals alongside direct scanning to show you the same exposed surfaces an attacker would see. what is a google dork? from advanced search operator to attack primitive.

Useful Google Dorks For Open Source Intelligence Investigations Google dorking is a technique that uses advanced search operators to find very specific content that ordinarily won't show up with a normal search query. these operators allow you to pinpoint. Explore a comprehensive, categorized list of google dorks for bug bounty hunting, osint research, ethical hacking, and security exposure discovery. learn and use powerful search queries. It is the process of using advanced search operators (dorks) to find specific information on google that is not readily available through normal searches. this often includes sensitive files, exposed servers, and vulnerable web applications. In this guide, we are going to look at how investigators use google dorks to identify exposed secrets, how to think about the underlying data types (environment files, git artefacts, backup archives), and how to do this work responsibly.
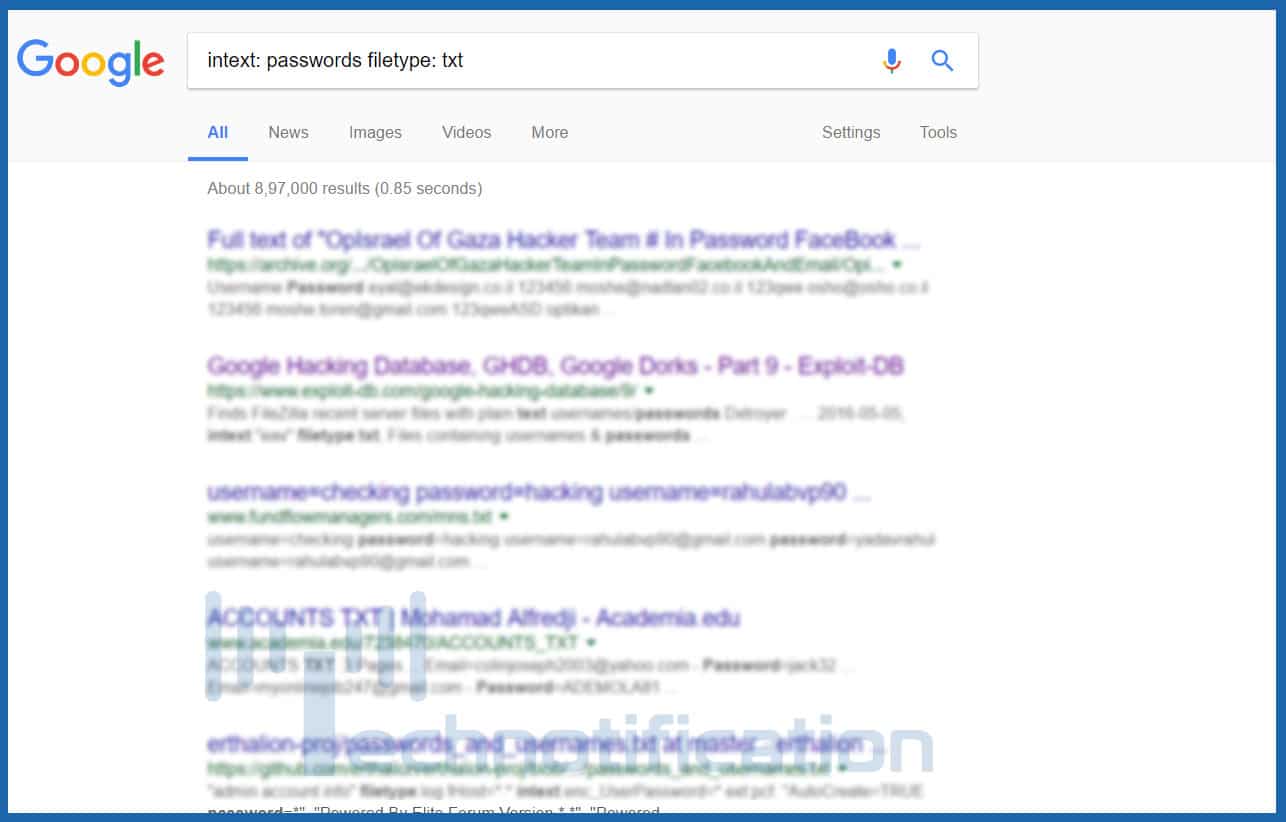
Google Dorks Use Google For Hacking Websites Databases And Cameras It is the process of using advanced search operators (dorks) to find specific information on google that is not readily available through normal searches. this often includes sensitive files, exposed servers, and vulnerable web applications. In this guide, we are going to look at how investigators use google dorks to identify exposed secrets, how to think about the underlying data types (environment files, git artefacts, backup archives), and how to do this work responsibly. Gain access to sensitive files like customer data and even full server backups by exploring these lesser known s3 subdomains: and that’s it, folks! with these search strings in your toolkit, you’ll be able to uncover the hidden gems of the internet. This list is about powerful search techniques for discovering exposed emails, passwords, confidential files, and sensitive information using advanced google search operators. In the hands of a threat actor, google transforms from a simple search engine into a powerful reconnaissance weapon. google dorks, advanced search operators, are used to uncover sensitive information inadvertently exposed online, including vast amounts of personally identifiable information (pii). What are google dorks? google dorks are advanced search queries used to identify sensitive data, vulnerabilities, and exposed information indexed by google. essential for penetration testers, bug bounty hunters, digital investigators, and anyone interested in web security.
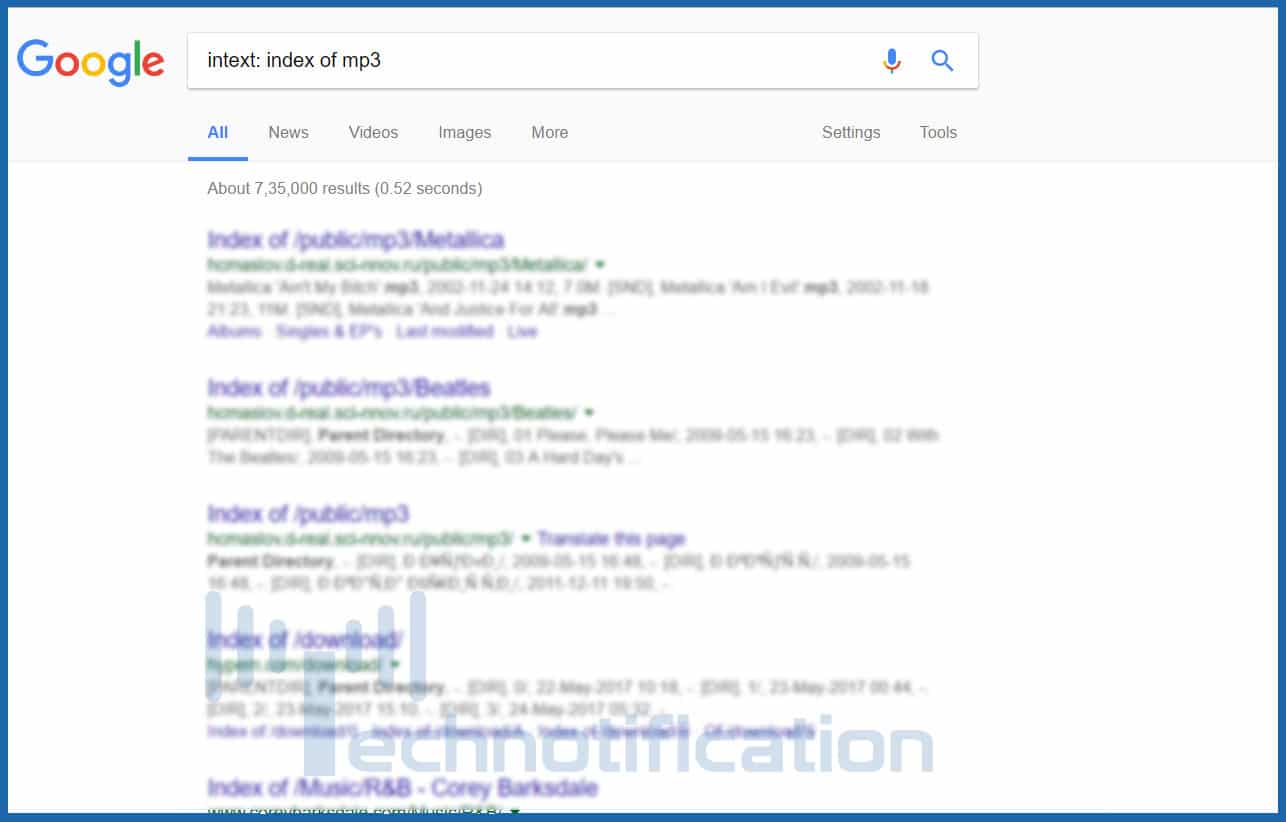
Google Dorks Use Google For Hacking Websites Databases And Cameras Gain access to sensitive files like customer data and even full server backups by exploring these lesser known s3 subdomains: and that’s it, folks! with these search strings in your toolkit, you’ll be able to uncover the hidden gems of the internet. This list is about powerful search techniques for discovering exposed emails, passwords, confidential files, and sensitive information using advanced google search operators. In the hands of a threat actor, google transforms from a simple search engine into a powerful reconnaissance weapon. google dorks, advanced search operators, are used to uncover sensitive information inadvertently exposed online, including vast amounts of personally identifiable information (pii). What are google dorks? google dorks are advanced search queries used to identify sensitive data, vulnerabilities, and exposed information indexed by google. essential for penetration testers, bug bounty hunters, digital investigators, and anyone interested in web security.
.png)
Mitigating Data Breaches With Osint Authentic8 In the hands of a threat actor, google transforms from a simple search engine into a powerful reconnaissance weapon. google dorks, advanced search operators, are used to uncover sensitive information inadvertently exposed online, including vast amounts of personally identifiable information (pii). What are google dorks? google dorks are advanced search queries used to identify sensitive data, vulnerabilities, and exposed information indexed by google. essential for penetration testers, bug bounty hunters, digital investigators, and anyone interested in web security.

Hacking Exposed Leveraging Google Dorks Shodan And Censys For Cyber
Comments are closed.