Google Cloud Security Best Practices Identity And Access Management
Google Cloud Security Best Practices Pdf Cloud Computing Security These guides outline some of the best practices for using cloud identity & access management (iam) to manage identities and permissions for your organization. learn more about google. In this blog post, we’ll break down key concepts related to iam, including roles, permissions, identity, least privilege access, and best practices for secure access management.

Google Cloud Security Best Practices Identity And Access Management Hardening google cloud platform systems requires a comprehensive approach that encompasses identity and access management, network security, data encryption, monitoring, patch management, incident. Learn essential google cloud security best practices, common misconfigurations, and how to protect gcp resources from breaches and compliance risks. We will discuss common security challenges organizations face while using gcp and outline nine google cloud security essential best practices that you should implement for a strong cloud security posture. Learn 8 practical google cloud security best practices—from encryption and iam to dspm and devops—to build a resilient, compliant cloud infrastructure.
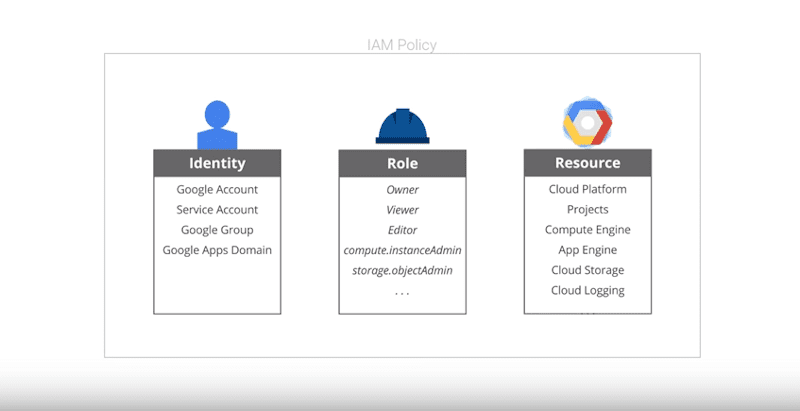
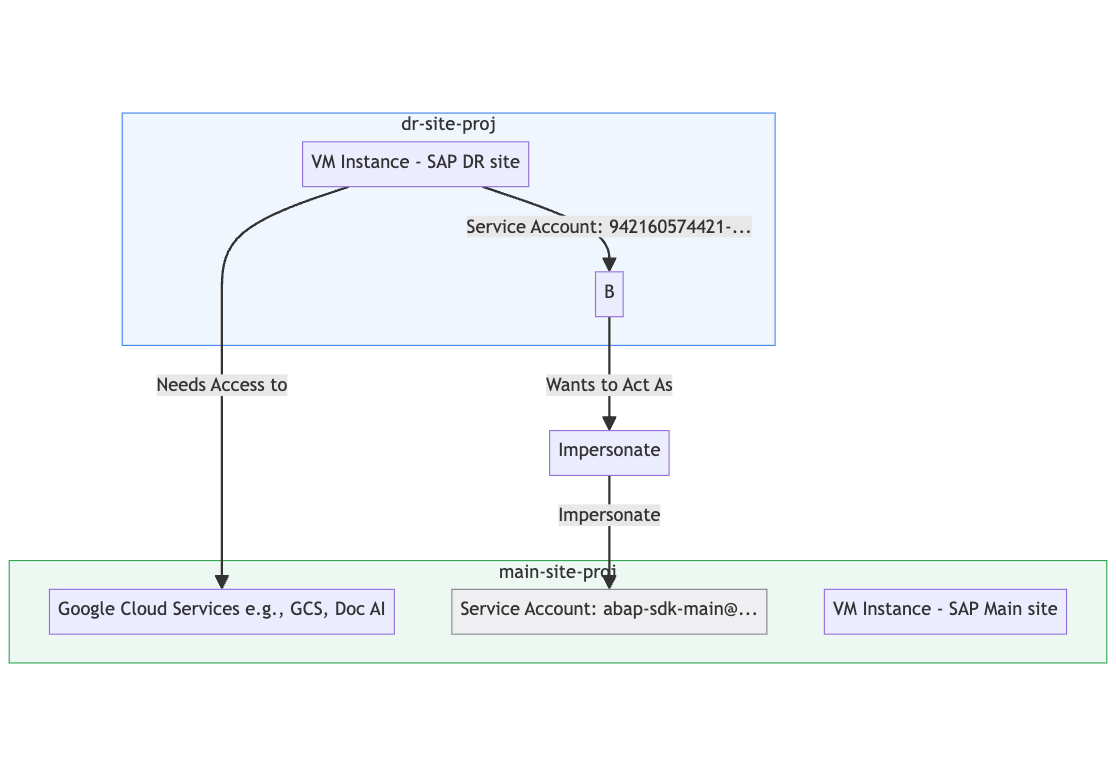
Google Introduces Identity And Access Management For Cloud Platform We will discuss common security challenges organizations face while using gcp and outline nine google cloud security essential best practices that you should implement for a strong cloud security posture. Learn 8 practical google cloud security best practices—from encryption and iam to dspm and devops—to build a resilient, compliant cloud infrastructure. Google cloud platform (gcp) manages identity and access management (iam) information. this article covers the basics and details of the system, as well as detailed instructions on setting up identity and access management (iam) in gcp. One of the most critical — yet often misunderstood — components of gcp’s security model is identity and access management (iam). this guide will walk you through what iam is, why it matters, and how to implement iam best practices to protect resources while enabling productivity. Key aspects of cloud identity and access management, including security protocols, user access controls, and integration strategies. This self paced training course gives participants broad study of security controls and techniques on google cloud.

Account Authentication And Password Management Best Practices Google Google cloud platform (gcp) manages identity and access management (iam) information. this article covers the basics and details of the system, as well as detailed instructions on setting up identity and access management (iam) in gcp. One of the most critical — yet often misunderstood — components of gcp’s security model is identity and access management (iam). this guide will walk you through what iam is, why it matters, and how to implement iam best practices to protect resources while enabling productivity. Key aspects of cloud identity and access management, including security protocols, user access controls, and integration strategies. This self paced training course gives participants broad study of security controls and techniques on google cloud.
Google Cloud Platform Security Checklist Part 1 7 Identity And Key aspects of cloud identity and access management, including security protocols, user access controls, and integration strategies. This self paced training course gives participants broad study of security controls and techniques on google cloud.
Google Cloud Platform Security Checklist Part 1 7 Identity And
Comments are closed.