Google Amp Exploited In Phishing Attacks Targeting Enterprise Users
Aitm Phishing Attack Against Enterprise Users Zscaler Explore the exploitation of google amp in phishing attacks, its impact on enterprises, and how keepnet's redirect url analyzer detects and mitigates these threats effectively. Cyber defenders have observed the latest malicious campaigns leveraging the phishing attack vector, in which hackers exploit google accelerated mobile pages (amp) and apply a novel adversary tactic to evade detection.
Cloud Threats Memo Exploiting Google Forms For Phishing Campaigns Threat actors are using google amp urls in phishing campaigns aimed at enterprises as a new detection evasion tactic. Threat actors have begun using google amp urls as links inside their phishing emails as part of a new strategy. these links have a track record of successfully contacting enterprise level workers since they are hosted on trusted domains. Attackers have been abusing a google amp feature that allows newly created pages to be hosted on google amp urls, often using google analytics to track user interaction. these phishing attacks have been successful at bypassing secure email gateways and reaching their intended targets. Cybercriminals embed google amp urls in phishing emails, exploiting google's reputation to evade email protection technology's detection of malicious content. these urls redirect victims.
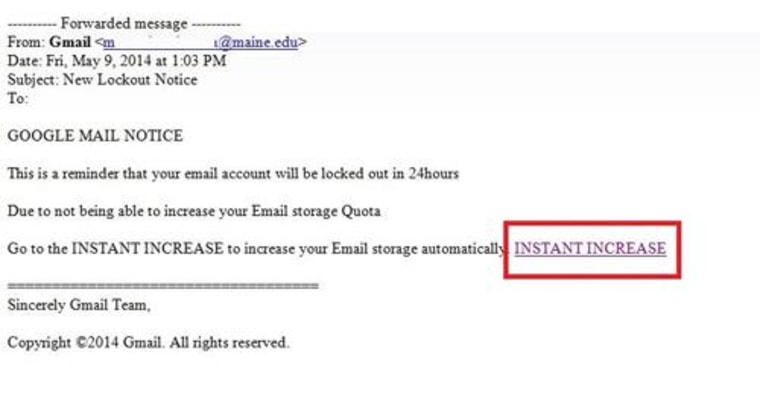
Hackers Target Google Users In Advanced Phishing Attack Attackers have been abusing a google amp feature that allows newly created pages to be hosted on google amp urls, often using google analytics to track user interaction. these phishing attacks have been successful at bypassing secure email gateways and reaching their intended targets. Cybercriminals embed google amp urls in phishing emails, exploiting google's reputation to evade email protection technology's detection of malicious content. these urls redirect victims. Threat actors have been observed abusing google accelerated mobile pages (amp) in phishing campaigns, as a new tactic to evade detection, email protection firm cofense reports. Security researchers are warning of increased phishing activity that abuses google accelerated mobile pages (amp) to bypass email security measures and get to inboxes of enterprise employees. This operation, uncovered by group ib researchers, employs advanced technical strategies to deceive victims and evade detection, including the misuse of google accelerated mobile pages (amp) links and third party javascript libraries. Google amp is an open source html framework designed to create websites optimized for mobile browsers. in this recent campaign, the attackers leveraged websites hosted on google or google.co.uk to exploit the trust associated with these domains and avoid security measures.
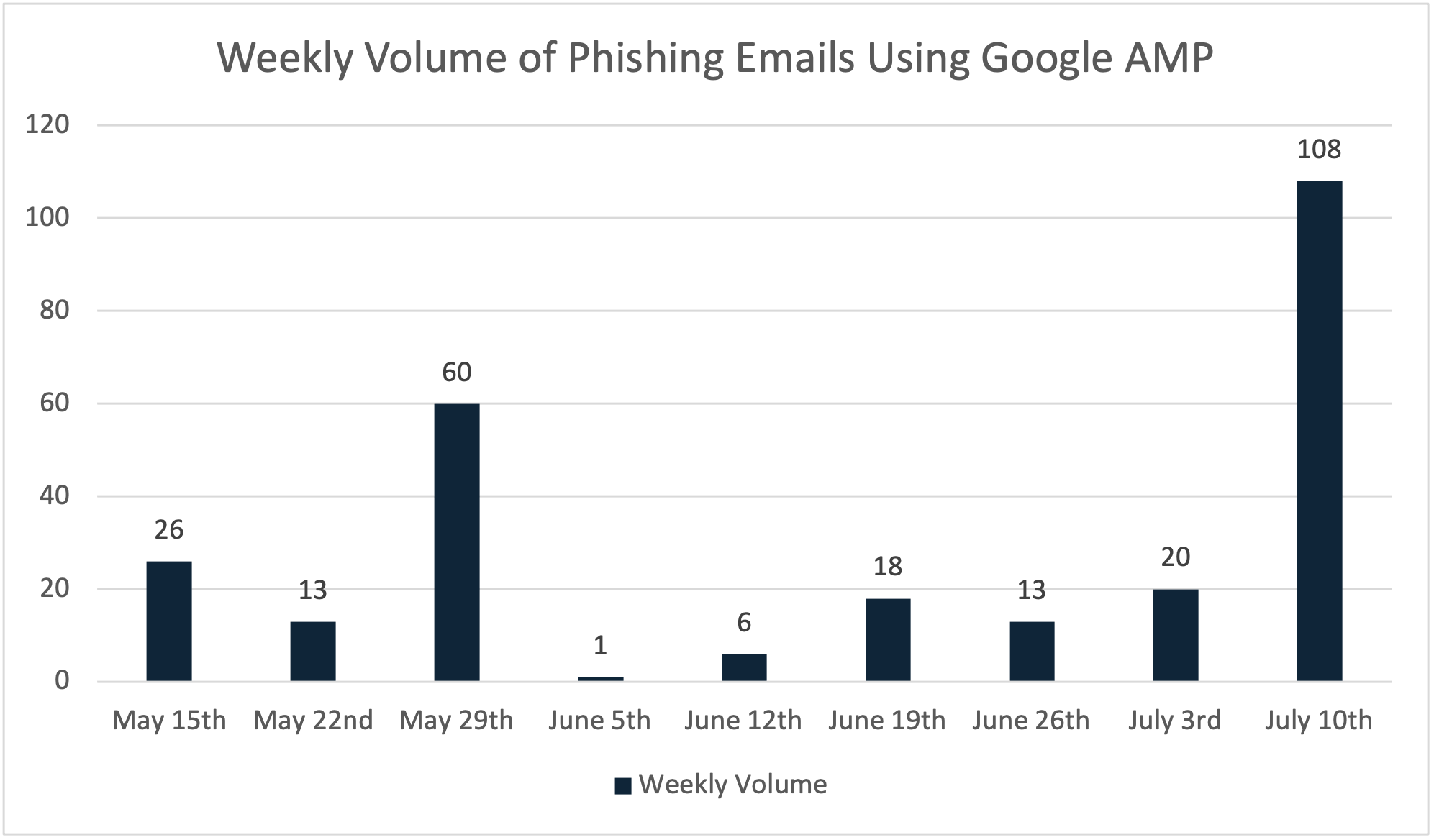
Google Amp The Newest Of Evasive Phishing Tactic Threat actors have been observed abusing google accelerated mobile pages (amp) in phishing campaigns, as a new tactic to evade detection, email protection firm cofense reports. Security researchers are warning of increased phishing activity that abuses google accelerated mobile pages (amp) to bypass email security measures and get to inboxes of enterprise employees. This operation, uncovered by group ib researchers, employs advanced technical strategies to deceive victims and evade detection, including the misuse of google accelerated mobile pages (amp) links and third party javascript libraries. Google amp is an open source html framework designed to create websites optimized for mobile browsers. in this recent campaign, the attackers leveraged websites hosted on google or google.co.uk to exploit the trust associated with these domains and avoid security measures.
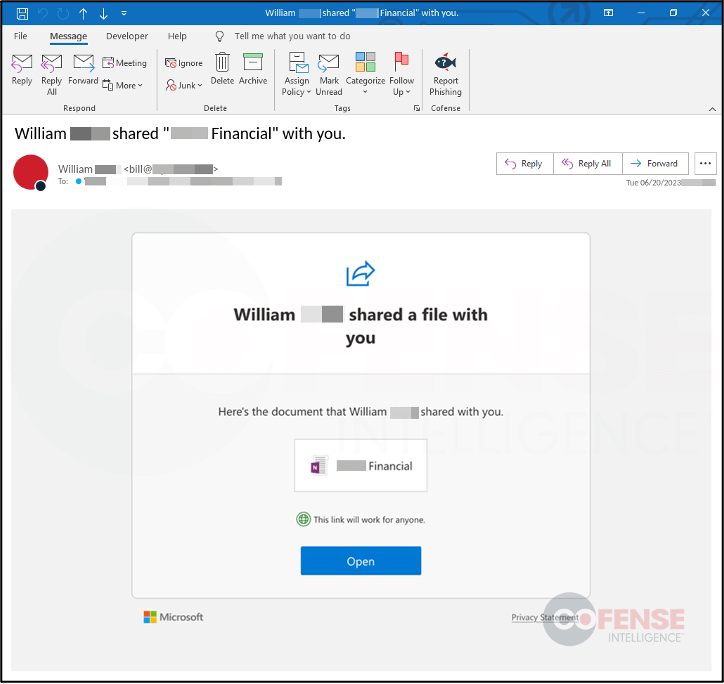
Google Amp The Newest Of Evasive Phishing Tactic This operation, uncovered by group ib researchers, employs advanced technical strategies to deceive victims and evade detection, including the misuse of google accelerated mobile pages (amp) links and third party javascript libraries. Google amp is an open source html framework designed to create websites optimized for mobile browsers. in this recent campaign, the attackers leveraged websites hosted on google or google.co.uk to exploit the trust associated with these domains and avoid security measures.
Comments are closed.