Goodware Hash Sets Sans Internet Storm Center
Sans Edu Internet Storm Center Sans Internet Storm Center In your threat hunting process, you can search for interesting files across your infrastructure via sets of malware hashes. some of them are freely available like on malware bazaar [1]. In this episode of the sans internet storm center's stormcast, we cover the latest cybersecurity threats and defenses, including python delivered malware, goodware hash sets,.

Sans Internet Storm Center Cert eu disclosed on april 2 3, 2026 that the european commission's europa web hosting platform on aws was breached through the trivy supply chain compromise (cve 2026 33634). this is the highest profile governmental victim disclosure to date. key details from the cert eu advisory:. In this episode of the sans internet storm center's stormcast, we cover the latest cybersecurity threats and defenses, including python delivered malware, goodware hash sets, ssl tls protocol updates, and critical vulnerabilities in asus routers and paessler prtg. Sans.edu internet storm center. today's top story: teampcp supply chain campaign: update 007 cisco source code stolen via trivy linked breach, google gtig tracks teampcp as unc6780, and cisa kev deadline arrives with no standalone advisory;more honeypot fingerprinting scans;. Hashes are a nice way to identify malware samples, payload, or any type of suspicious files (i usually share the hash of the malware analyzed in my diaries). in your threat hunting process, you can search for interesting files across your infrastructure via sets of malware hashes.

Sans Internet Storm Center Sans.edu internet storm center. today's top story: teampcp supply chain campaign: update 007 cisco source code stolen via trivy linked breach, google gtig tracks teampcp as unc6780, and cisa kev deadline arrives with no standalone advisory;more honeypot fingerprinting scans;. Hashes are a nice way to identify malware samples, payload, or any type of suspicious files (i usually share the hash of the malware analyzed in my diaries). in your threat hunting process, you can search for interesting files across your infrastructure via sets of malware hashes. Stormcast 01 06 24: python sweatrat, goodware hashes, ssl tls changes 2024, malicious chrome extensions and more jan 6, 2025. Hashes are a nice way to identify malware samples, payload, or any type of suspicious files (i usually share the hash of the malware analyzed in my diaries). in your threat hunting process, you can search for interesting files across your infrastructure via sets of malware hashes. Stormcast january 5th 2024: python sweatrat, goodware hashes, ssl tls changes 2024, malicious chrome extensions and more jan 5, 2025. A daily summary of cyber security news from the sans internet stormcenter.
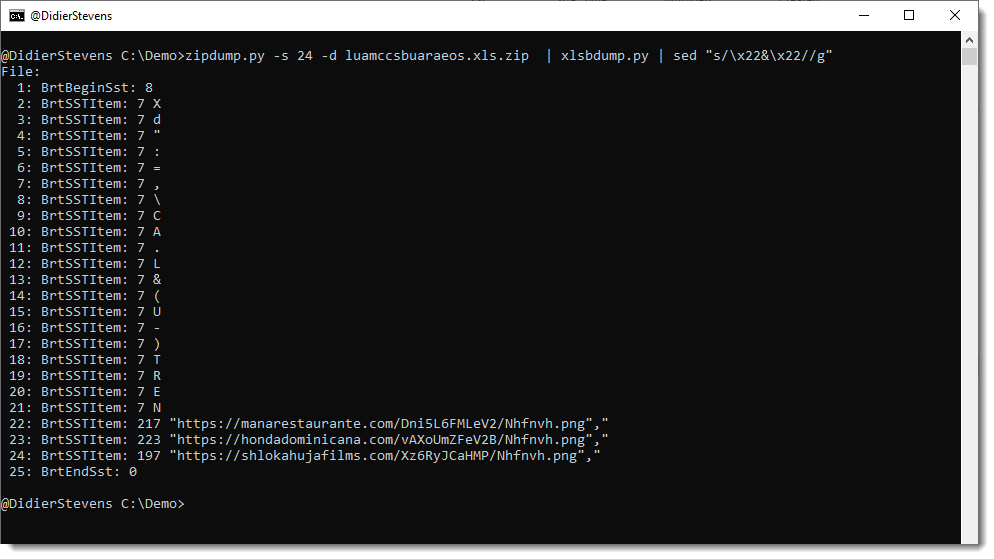
Sans Edu Internet Storm Center Sans Internet Storm Center Stormcast 01 06 24: python sweatrat, goodware hashes, ssl tls changes 2024, malicious chrome extensions and more jan 6, 2025. Hashes are a nice way to identify malware samples, payload, or any type of suspicious files (i usually share the hash of the malware analyzed in my diaries). in your threat hunting process, you can search for interesting files across your infrastructure via sets of malware hashes. Stormcast january 5th 2024: python sweatrat, goodware hashes, ssl tls changes 2024, malicious chrome extensions and more jan 5, 2025. A daily summary of cyber security news from the sans internet stormcenter.
Comments are closed.