Going Beyond Compliance With Effective Vulnerability Management
Going Beyond Compliance With Effective Vulnerability Management Vsociety Going beyond compliance with effective vulnerability management poc video description tags #infosec#vulnerabilitymanagement#webinar#vicarius video#vicarius blog#compliance @bskelly 1 post subscribe to user total vcoins 7.1k badges early bird show more comments (0) show 5 more replies @bskelly 1 post subscribe to user total vcoins 7.1k share. Join cyber security expert, derek a. smith, who will outline the key steps to effective vulnerability management and provide an in depth look at the tools, challenges and best practices of each part of the vm lifecycle.
Effective Vulnerability Management Managing Risk In The Vulnerable In this blog, we’ll explore how key technologies — threat intelligence platforms (tips), security information and event management (siem), and generative ai (genai) — can enhance vulnerability management, making security operations more efficient and compliance easier to maintain. Explore the top 10 vulnerability management best practices to protect systems, apply proactive methods, and secure your it infrastructure. Want to learn how vulnerability management supports each of these standards? explore our blog on how vulnerability management helps meet compliance requirements. A robust vulnerability management program naturally leads to better compliance and, more importantly, a stronger, more resilient security posture. start by assessing your current program against these steps.

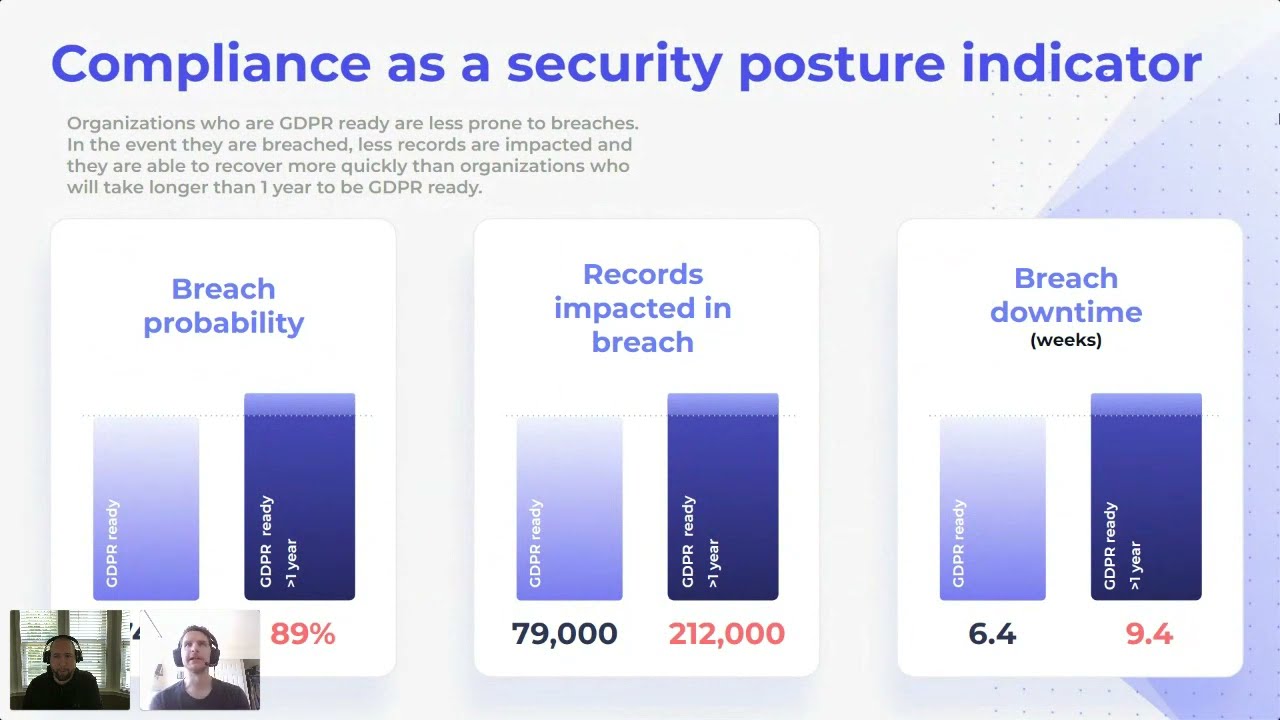
Vulnerability Management For Compliance Want to learn how vulnerability management supports each of these standards? explore our blog on how vulnerability management helps meet compliance requirements. A robust vulnerability management program naturally leads to better compliance and, more importantly, a stronger, more resilient security posture. start by assessing your current program against these steps. Through the adoption and implementation of a robust vulnerability and remediation management system, an organization can make continual improvements to the security posture of its systems, ensuring the on going security of its critical business processes. These aren’t just cautionary tales; they’re signposts pointing to a persistent, industry wide challenge: maintaining effective vulnerability management in the face of constant change. Learn top vulnerability management, scanning, and remediation best practices to protect your systems and reduce security risks effectively. read today!. We explore the importance and common challenges of vulnerability management, and how to build an effective vulnerability management process.

What Is Effective Vulnerability Management Through the adoption and implementation of a robust vulnerability and remediation management system, an organization can make continual improvements to the security posture of its systems, ensuring the on going security of its critical business processes. These aren’t just cautionary tales; they’re signposts pointing to a persistent, industry wide challenge: maintaining effective vulnerability management in the face of constant change. Learn top vulnerability management, scanning, and remediation best practices to protect your systems and reduce security risks effectively. read today!. We explore the importance and common challenges of vulnerability management, and how to build an effective vulnerability management process.

Vulnerability Management A Comprehensive Guide Learn top vulnerability management, scanning, and remediation best practices to protect your systems and reduce security risks effectively. read today!. We explore the importance and common challenges of vulnerability management, and how to build an effective vulnerability management process.
Vulnerability Management Information Compliance Remediation Reporting
Comments are closed.