Gnu Crypto Cipher Gnu Cryptographic Primitives And Tools Version 2 0 0

Cryptographic Primitives Pdf Cryptography Time Complexity It transforms the plaintext to the ciphertext, and the ciphertext back to the plaintext, using the aes in electronic codebook mode with no padding. note also the classes for cipher modes and padding schemes for more complex constructions. Gnu crypto, part of the gnu project, released under the aegis of gnu, aims at providing free, versatile, high quality, and provably correct implementations of cryptographic primitives and tools in the java programming language for use by programmers and end users.

Chapter 2 Cryptographic Tools Pdf Gnu crypto, part of the gnu project, released under the aegis of gnu, aims at providing free, versatile, high quality, and provably correct implementations of cryptographic primitives and tools in the java programming language for use by programmers and end users. This is a java implementation of ent (a pseudorandom number sequence test program) developed by john walker) which applies various tests to sequences of bytes generated by the gnu crypto library pseudo random number generator implementations. The gnu crypto implementation of the java cryptographic extension (jce) provider. Encrypts exactly one block of plaintext. specified by: encryptblock in interface iblockcipher parameters: in the plaintext. inoffset index of in from which to start considering data. out the ciphertext. outoffset index of out from which to store result. throws: java.lang.illegalstateexception if the instance is not initialised.
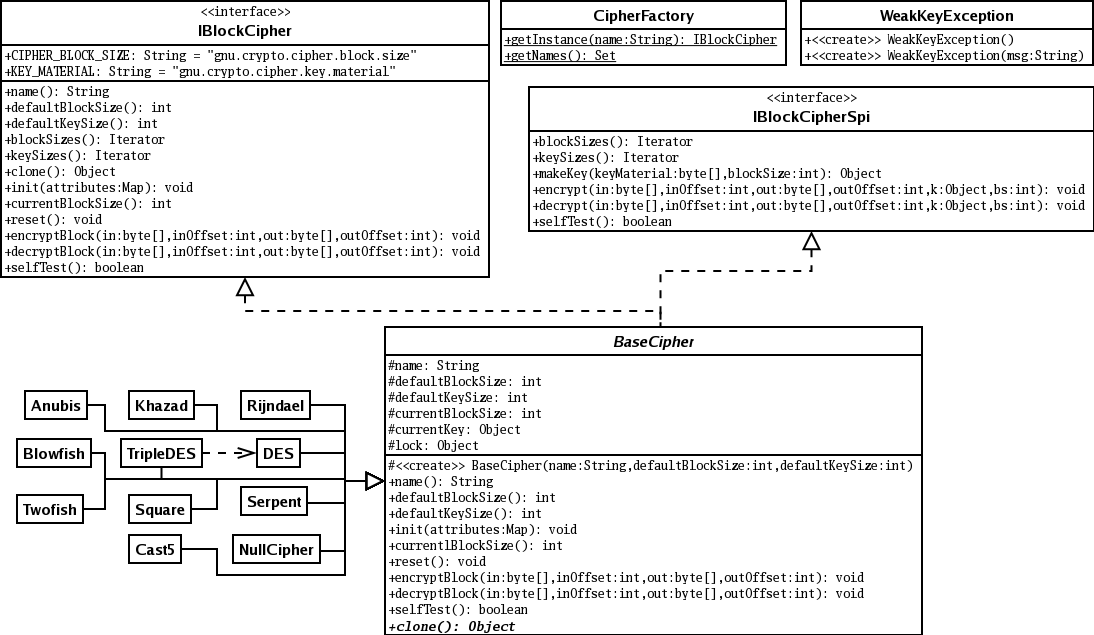
Gnu Crypto Cipher Gnu Cryptographic Primitives And Tools Version 2 0 0 The gnu crypto implementation of the java cryptographic extension (jce) provider. Encrypts exactly one block of plaintext. specified by: encryptblock in interface iblockcipher parameters: in the plaintext. inoffset index of in from which to start considering data. out the ciphertext. outoffset index of out from which to store result. throws: java.lang.illegalstateexception if the instance is not initialised. Libgcrypt is a general purpose crypto library based on the code. used in gnupg. libgcrypt depends on the library `libgpg error', which must be installed correctly before libgcrypt is to be built. libgcrypt is distributed under the lgpl, see the section "license" below for details. build instructions. Full set of java cryptographic tools. gnu crypto is a versatile, and provably correct implementation of cryptographic primitives and tools for use by both programmers and end users. It includes several cryptographic algorithms like aes, des, sha 1, rsa, dsa, diffie hellman, and many others. it also supports x.509 certificates and crls, and pkcs #10 certificate requests, and has a high level filter pipe message processing system. Comparison of cryptography libraries the tables below compare cryptography libraries that deal with cryptography algorithms and have application programming interface (api) function calls to each of the supported features.
Github Ilwoong Crypto Primitives C Implementations Of Cryptographic Libgcrypt is a general purpose crypto library based on the code. used in gnupg. libgcrypt depends on the library `libgpg error', which must be installed correctly before libgcrypt is to be built. libgcrypt is distributed under the lgpl, see the section "license" below for details. build instructions. Full set of java cryptographic tools. gnu crypto is a versatile, and provably correct implementation of cryptographic primitives and tools for use by both programmers and end users. It includes several cryptographic algorithms like aes, des, sha 1, rsa, dsa, diffie hellman, and many others. it also supports x.509 certificates and crls, and pkcs #10 certificate requests, and has a high level filter pipe message processing system. Comparison of cryptography libraries the tables below compare cryptography libraries that deal with cryptography algorithms and have application programming interface (api) function calls to each of the supported features.
Cryptographic Primitives Panther Protocol Documentation It includes several cryptographic algorithms like aes, des, sha 1, rsa, dsa, diffie hellman, and many others. it also supports x.509 certificates and crls, and pkcs #10 certificate requests, and has a high level filter pipe message processing system. Comparison of cryptography libraries the tables below compare cryptography libraries that deal with cryptography algorithms and have application programming interface (api) function calls to each of the supported features.
Comments are closed.