Github Yubie Re Ida Jm Xorstr Decrypt Plugin Attempts To Decrypt Jm
Encode Decode Encrypt Decrypt Plugin Bubble Attempts to decrypt jm xorstr in some x64 binaries yubie re ida jm xorstr decrypt plugin. Attempts to decrypt jm xorstr in some x64 binaries releases · yubie re ida jm xorstr decrypt plugin.

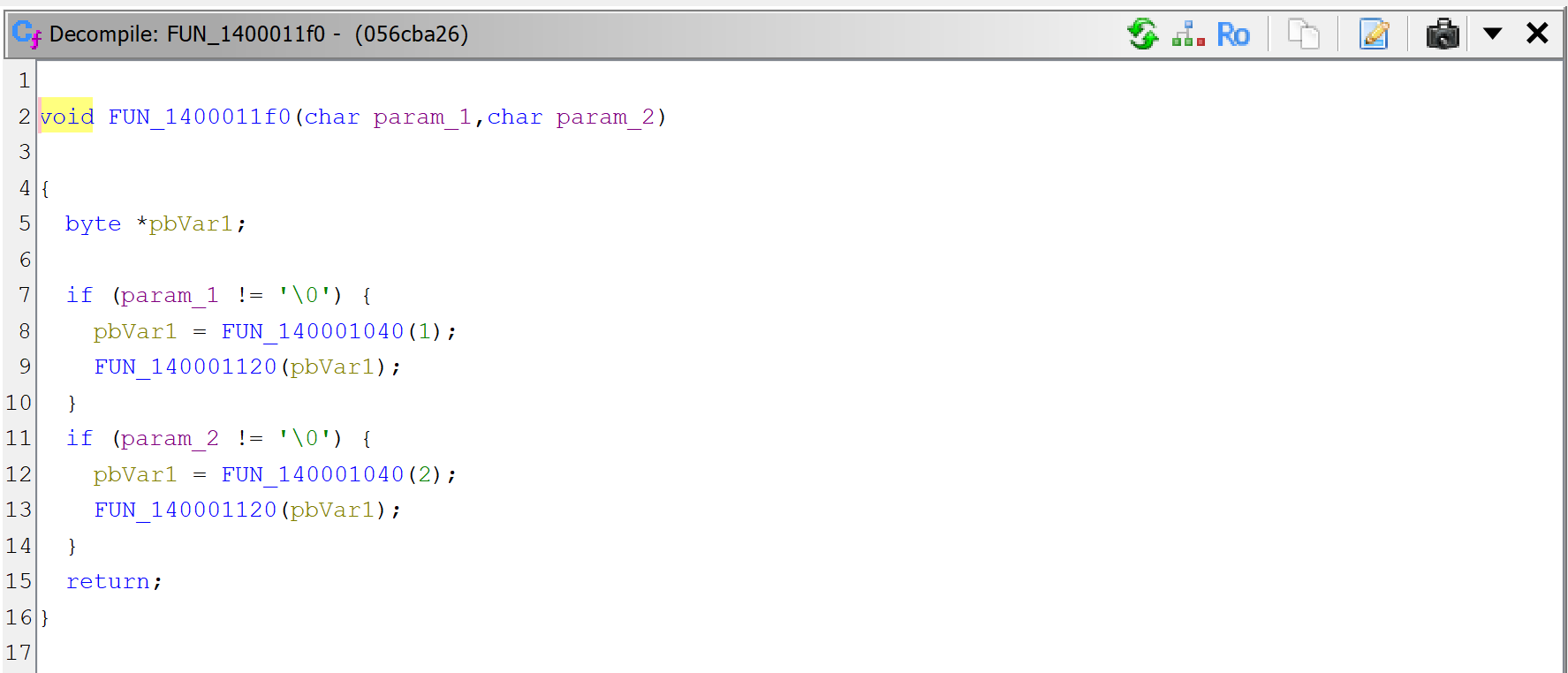
News Explorer Florida Tries Again After Failed Bitcoin Reserve Bill Finds where the initial mov is for the key or data. this matches the stack address and checks that it is being written to with a mov. this moves backwards. returns the instruction where the first mov is for the data or key. this moves backwards. There aren’t any open issues. you could search all of github or try an advanced search. Yubie re has 20 repositories available. follow their code on github. Attempts to decrypt jm xorstr in some x64 binaries file finder · yubie re ida jm xorstr decrypt plugin.
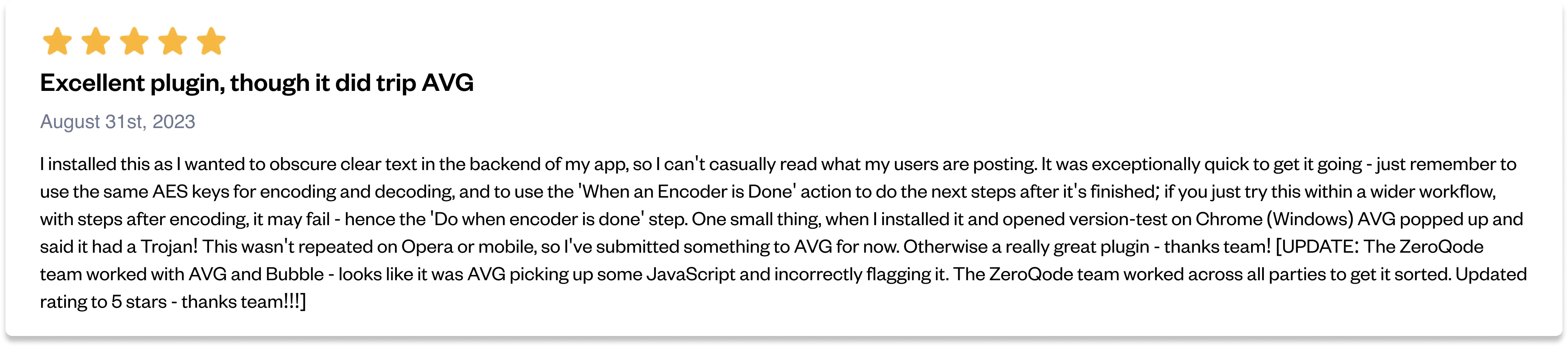
Encode Decode Encrypt Decrypt Plugin Bubble Yubie re has 20 repositories available. follow their code on github. Attempts to decrypt jm xorstr in some x64 binaries file finder · yubie re ida jm xorstr decrypt plugin. This video is intended to get you started creating ida plugins with python, recognize the importance of deobfuscating strings and work on translating assembly to a higher level language (i.e. python). There have been a few attempts at decrypting strings from malware that use this library (or a variation of the technique). while these are good references they don't cover all of the cases in a generic way which is our goal. A comprehensive list of plugins for ida pro. know of a plugin not in the list? saw a typo? a better way to describe a plugin? go to the repo and send a pr! if you feel you have the skills to improve this terrible ui please feel free to contribute too! loading author: vincent mallet. see source. An ai powered assistant for ida 9.0 to accelerate reverse engineering of c games.

Encode Decode Encrypt Decrypt Plugin Bubble This video is intended to get you started creating ida plugins with python, recognize the importance of deobfuscating strings and work on translating assembly to a higher level language (i.e. python). There have been a few attempts at decrypting strings from malware that use this library (or a variation of the technique). while these are good references they don't cover all of the cases in a generic way which is our goal. A comprehensive list of plugins for ida pro. know of a plugin not in the list? saw a typo? a better way to describe a plugin? go to the repo and send a pr! if you feel you have the skills to improve this terrible ui please feel free to contribute too! loading author: vincent mallet. see source. An ai powered assistant for ida 9.0 to accelerate reverse engineering of c games.
How To Use Jeb Auto Decrypt Strings In Protected Binary Code Jeb In A comprehensive list of plugins for ida pro. know of a plugin not in the list? saw a typo? a better way to describe a plugin? go to the repo and send a pr! if you feel you have the skills to improve this terrible ui please feel free to contribute too! loading author: vincent mallet. see source. An ai powered assistant for ida 9.0 to accelerate reverse engineering of c games.
Comments are closed.